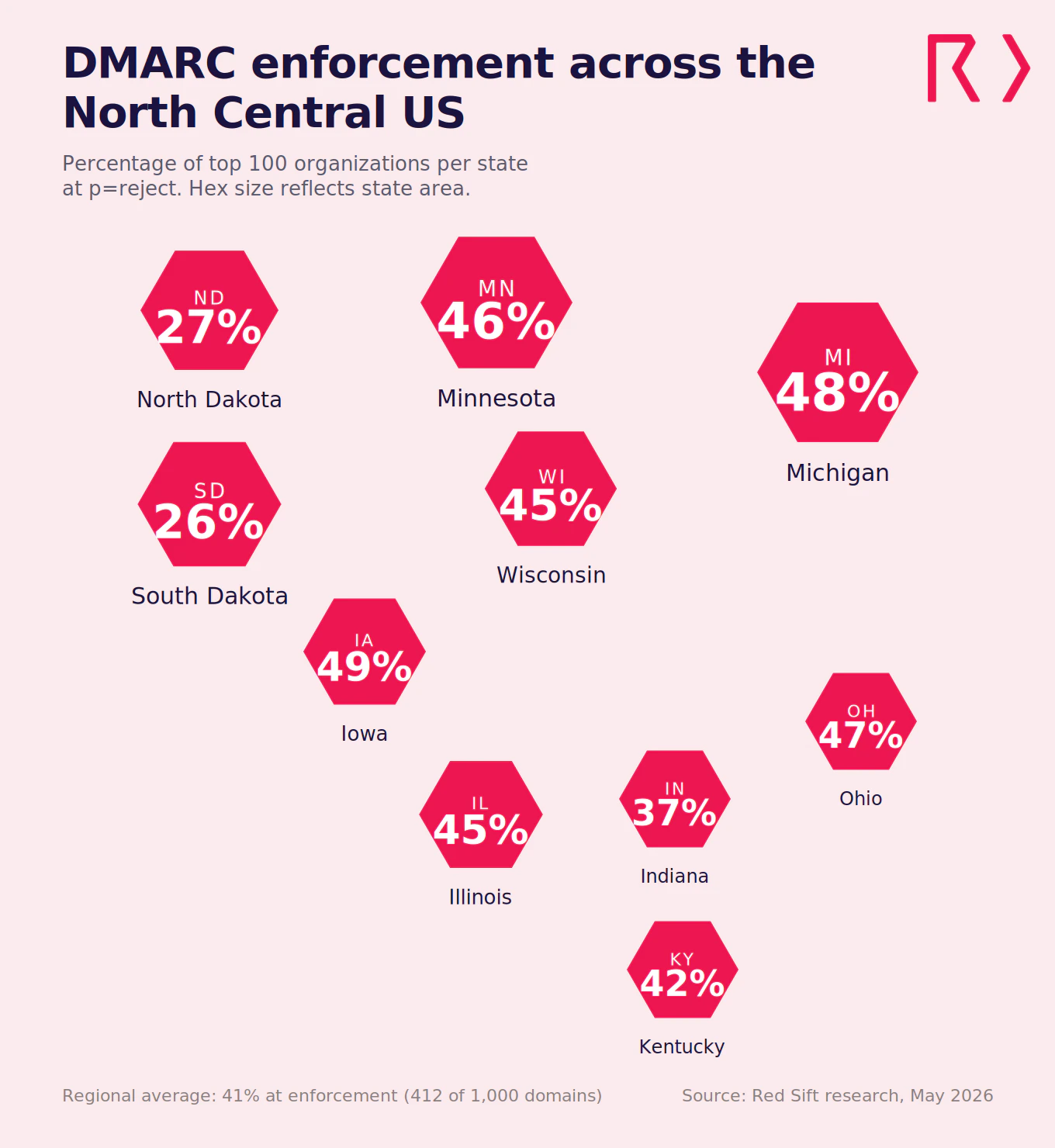
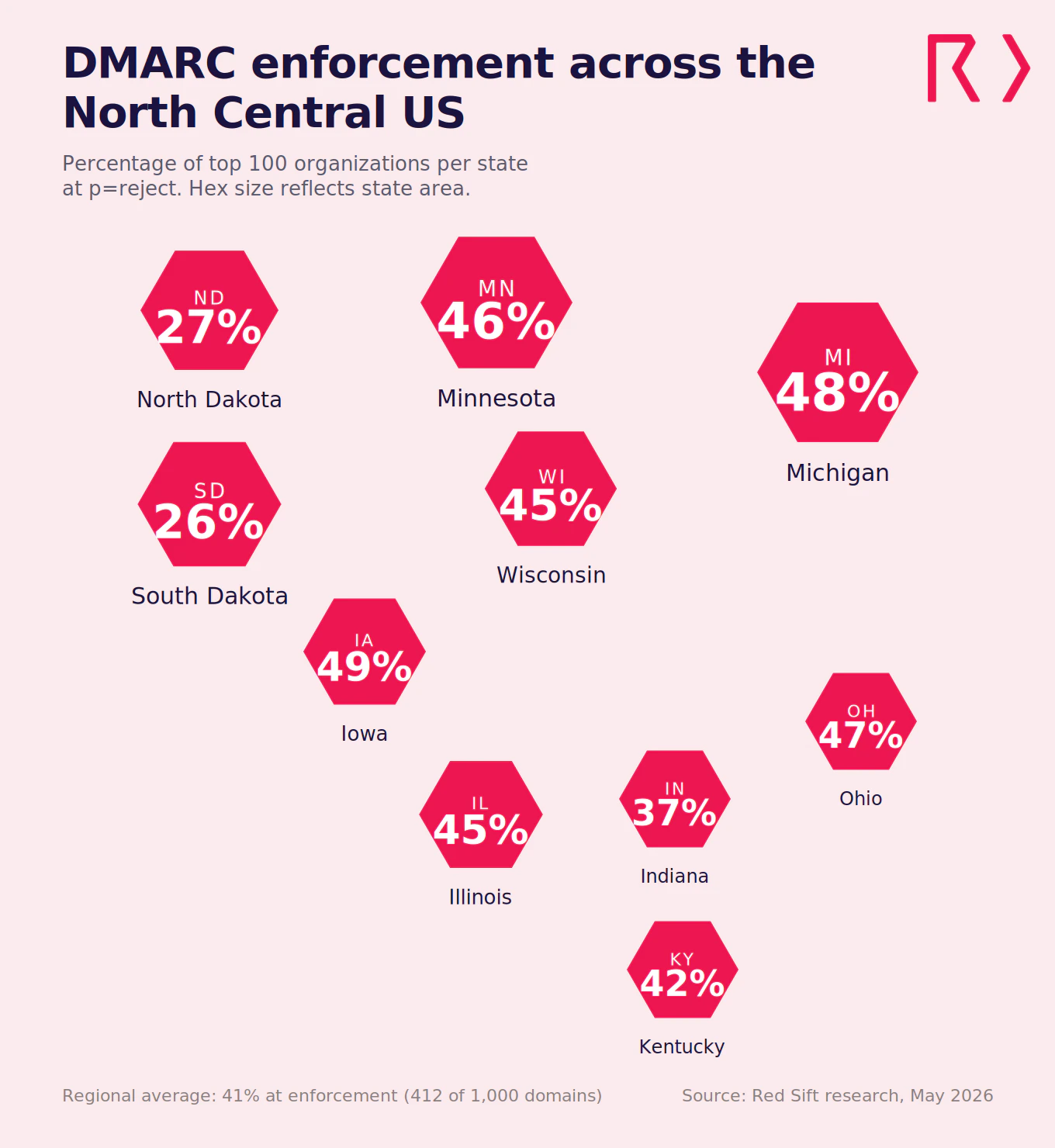
Red Sift analyzed 1,000 domains belonging to the largest organizations across ten North Central states, and found that only 412 (41%) have reached full DMARC enforcement. The North Central region is the manufacturing backbone of the United States, the center of the country’s agricultural output, and home to financial services hubs that process trillions of dollars in transactions each year. Despite that concentration of economic activity, 59% of the region’s top organizations aren’t blocking spoofed email. Similar research on different regions by Red Sift includes the Northeast (35%), Mid-Atlantic (44%), Southwest (40%), and Heartland (36%).
Key takeaways
- Only 412 of 1,000 domains (41%) across ten North Central states have reached DMARC enforcement (p=reject)
- 283 domains (28.3%) run p=none policies that monitor but take no action against spoofed emails
- 210 domains (21%) sit at p=quarantine, close to full protection but not finishing the move to reject
- 95 domains (9.5%) have no DMARC record published at all
- Iowa leads the region at 49% enforcement. South Dakota trails at 26%
What does the research reveal about email authentication in the North Central U.S.?
Red Sift analyzed 100 domains from the top organizations in each of ten North Central states: Illinois, Indiana, Iowa, Kentucky, Michigan, Minnesota, North Dakota, Ohio, South Dakota, and Wisconsin. The results show a region where the industrial and agricultural core of the country still leaves the majority of its domains unprotected against email impersonation.
Across all 1,000 domains, 41% have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts the North Central region ahead of the Northeast (35%) and Heartland (36%), just behind the Southwest (40%), and still trailing the Mid-Atlantic (44%) in Red Sift’s ongoing cross-region comparison.
State-by-state breakdown
- Iowa (49% at enforcement): Iowa leads the North Central region with 49 domains at p=reject, the strongest enforcement rate in the study. The state is one of the largest agricultural producers in the country, a growing center for data center development, and home to a financial services and insurance cluster in Des Moines. 24 domains run p=none, 21 sit at p=quarantine, and 6 have no record. For a state that handles billions in agricultural commodity trading and insurance underwriting, 49% is the highest rate Red Sift has recorded outside the Mid-Atlantic and New York, but more than half of its top organizations still lack full protection.
- Michigan (48% at enforcement): Michigan comes in second with 48 domains at p=reject. The state is the center of the American automotive industry, with Detroit and its surrounding counties home to the headquarters of major automakers and a vast supplier network. Michigan also has a significant defense sector, a growing technology industry, and major research universities. 24 domains run p=none, 21 sit at p=quarantine, and 7 have no record. Automotive supply chains run on purchase orders, tooling contracts, and just-in-time delivery confirmations that all travel by email. A spoofed domain targeting a Tier 1 supplier can disrupt production lines and redirect payments across the entire chain.
- Ohio (47% at enforcement): Ohio has 47 domains at p=reject and the joint-lowest N/A rate in the study at 4. The state is a manufacturing and healthcare powerhouse, home to major hospital systems, financial institutions, defense installations including Wright-Patterson Air Force Base, and a logistics network that connects the eastern and western halves of the country. 23 domains run p=none and 26 sit at p=quarantine. Those 26 quarantine domains have done the hard work already. The move from quarantine to reject is a short project that finishes a job mostly complete.
- Minnesota (46% at enforcement): Minnesota has 46 domains at p=reject. The state is home to one of the highest concentrations of Fortune 500 companies per capita in the country, spanning healthcare, medical devices, retail, financial services, and food production. Minneapolis-St. Paul anchors a corporate economy where email is the primary channel for vendor negotiations, claims processing, and supply chain coordination. 28 domains run p=none, 18 sit at p=quarantine, and 8 have no record. A state with that density of major corporations should be pushing past 50%, not sitting below it.
- Illinois (45% at enforcement): Illinois has 45 domains at p=reject. Chicago is the financial and commodities trading capital of the Midwest, home to the CME Group and CBOE, major banking operations, a massive healthcare sector, and one of the largest transportation and logistics networks in the country. 23 domains run p=none, 27 sit at p=quarantine, and 5 have no record. Illinois has the highest quarantine count in the study at 27. That’s 27 organizations that have identified their senders, configured SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail), and set a quarantine policy. The step from quarantine to reject typically takes 6 to 8 weeks.
- Wisconsin (45% at enforcement): Wisconsin ties Illinois with 45 domains at p=reject. The state is a major manufacturing center, the country’s largest dairy producer, and home to a healthcare and insurance industry spread across Milwaukee and Madison. 31 domains run p=none, 19 sit at p=quarantine, and 5 have no record. The 31 domains at p=none are watching spoofed emails arrive in their DMARC reports without blocking any of them. The data is there. Nobody’s acting on it.
- Kentucky (42% at enforcement): Kentucky has 42 domains at p=reject. The state is a national logistics hub, with Louisville serving as the main air hub for UPS and a center for healthcare, bourbon distilling, and automotive manufacturing. 29 domains run p=none, 21 sit at p=quarantine, and 8 have no record. Shipping confirmations, customs paperwork, and payment instructions for a logistics-heavy state like Kentucky all move by email. A spoofed domain targeting those workflows can redirect shipments or payments before anyone flags it.
- Indiana (37% at enforcement): Indiana has 37 domains at p=reject and the joint-lowest N/A rate in the study at 4. The state is a manufacturing and pharmaceutical hub, home to one of the largest concentrations of pharmaceutical companies in the country alongside significant defense operations at Crane Naval Surface Warfare Center and a motorsports industry based in Indianapolis. 33 domains run p=none, the highest none count in the study, and 26 sit at p=quarantine. 33 domains collecting DMARC data without acting on it is a problem, especially in a state where pharmaceutical supply chain communications and defense procurement emails are high-value targets.
- North Dakota (27% at enforcement): North Dakota has 27 domains at p=reject and the second-highest N/A rate in the study at 21. The state is a major energy producer thanks to the Bakken oil formation, a significant agricultural exporter, and home to military installations including Minot Air Force Base, which hosts one of the country’s nuclear ICBM wings. 38 domains run p=none and 14 sit at p=quarantine. A state hosting nuclear weapons infrastructure and processing billions in energy transactions should not have 21% of its top organizations missing a DMARC record entirely.
- South Dakota (26% at enforcement): South Dakota sits at the bottom with 26 domains at p=reject, the lowest enforcement rate in the North Central region and one of the lowest single-state rates Red Sift has recorded. The state is home to a major financial services and credit card processing cluster in Sioux Falls, alongside agriculture, tourism, and Ellsworth Air Force Base. 30 domains run p=none and 27 have no DMARC record at all, the highest N/A rate in the study. South Dakota’s 27% N/A rate is the highest Red Sift has seen since South Dakota and North Dakota’s neighbor states in the Heartland study. For a state whose economy depends on financial services and credit card processing, that gap is hard to explain.
Review your domain today
Use our free Red Sift Investigate tool to check your DMARC, SPF, and DKIM configuration.
Regional comparison
State | Reject | Quarantine | None | No record |
Iowa | 49% | 21% | 24% | 6% |
Michigan | 48% | 21% | 24% | 7% |
Ohio | 47% | 26% | 23% | 4% |
Minnesota | 46% | 18% | 28% | 8% |
Illinois | 45% | 27% | 23% | 5% |
Wisconsin | 45% | 19% | 31% | 5% |
Kentucky | 42% | 21% | 29% | 8% |
Indiana | 37% | 26% | 33% | 4% |
North Dakota | 27% | 14% | 38% | 21% |
South Dakota | 26% | 17% | 30% | 27% |
Regional total | 412 (41.2%) | 210 (21%) | 283 (28.3%) | 95 (9.5%) |
Northeast* | 35% | 22.6% | 30.9% | 11.6% |
Mid-Atlantic* | 44% | 19.4% | 27.3% | 9.1% |
Southwest* | 40% | 22.8% | 27.6% | 9.4% |
Heartland* | 36% | 22.4% | 31.9% | 9.2% |
New York* | 73% | 15% | 12% | 1% |
What the quarantine numbers tell us
The 210 organizations sitting at p=quarantine are close. They’ve done the DNS work, identified their senders, and configured SPF and DKIM. Moving from quarantine to reject typically takes 6 to 8 weeks. That’s 210 domains where a short project finishes a job that’s mostly complete.
Illinois and Indiana stand out here with 27 and 26 quarantine domains respectively. If those organizations moved to reject, Illinois would jump to 72% enforcement and Indiana to 63%. The infrastructure is in place. The final policy change is what’s missing.
Why DMARC is essential for the North Central region in 2026
The North Central region runs on industries where a spoofed email can trigger wire fraud, disrupt manufacturing supply chains, compromise pharmaceutical integrity, or intercept financial transactions worth millions. The region’s spread across ten states and multiple critical sectors makes the risk broad and the stakes high.
Manufacturing supply chains are the region’s biggest email fraud exposure
Michigan, Ohio, Indiana, Illinois, Wisconsin, and Kentucky form the country’s manufacturing core. Automotive supply chains, pharmaceutical production, industrial equipment, and food processing all depend on email for purchase orders, shipping confirmations, quality certifications, and payment instructions. The FBI’s IC3 logged $3.04 billion in BEC losses in 2025, with 86% of those funds moving via wire transfer or ACH. Manufacturing companies are high-value targets because their payment workflows involve large sums, multiple vendors, and time-sensitive approvals spread across complex supply chains. A spoofed email from a Tier 1 automotive supplier to an OEM, or from a pharmaceutical ingredient vendor to a manufacturer, can redirect six- and seven-figure payments before anyone catches it. DMARC enforcement at p=reject stops the impersonation before it reaches the inbox.
Agriculture and food production connect the entire region
Iowa, Minnesota, Wisconsin, North Dakota, and South Dakota are among the country’s largest agricultural producers. Grain trading, dairy processing, livestock auctions, ethanol production, and the vendor payment networks that connect farmers, processors, distributors, and retailers all run on email. Supply chain communications, including commodity contracts, phytosanitary certificates, delivery confirmations, and payment instructions, move through inboxes every day. A spoofed domain targeting a grain elevator, a dairy cooperative, or a food distributor can redirect payments, delay shipments, or introduce fraudulent instructions into supply chains that feed the country. The 28.3% of North Central domains sitting at p=none are watching this happen in their DMARC reports without blocking any of it.
Financial services and insurance hubs process trillions in transactions
Chicago’s financial district is one of the most important in the world, processing commodities trades, derivatives, and banking transactions worth trillions annually. Des Moines is one of the largest insurance centers in the country. Sioux Falls processes a significant share of the nation’s credit card transactions. Financial services firms, insurers, and payment processors are prime BEC targets because their workflows involve high-value transfers, policy payouts, and interbank communications. A spoofed email targeting a wire transfer approval, an insurance claim payment, or a credit card settlement can move large sums before fraud controls catch up. The 95 domains with no DMARC record at all are the most exposed, but the 283 at p=none are also at risk as enforcement tightens.
Military installations and defense contractors need stronger protection
North Dakota hosts Minot Air Force Base, home to one of the country’s nuclear ICBM wings and a B-52 bomber squadron. Ohio hosts Wright-Patterson Air Force Base, the headquarters of the Air Force Materiel Command. Kentucky’s Fort Knox and Indiana’s Crane Naval Surface Warfare Center add to the region’s defense footprint. Defense contractors, research partners, and government agencies operating in these states send email tied to procurement, logistics, and sensitive programs. North Dakota’s 27% enforcement rate and 21% N/A rate are among the lowest Red Sift has recorded, and they belong to a state where a spoofed domain targeting the defense supply chain is not just a phishing attempt. It’s a national security risk.
Mailbox providers are now rejecting unauthenticated email
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025 with its own enforcement for high-volume senders to Outlook, Hotmail, and Live.com addresses. Non-compliant messages are now rejected outright. For North Central organizations sending manufacturing purchase orders, agricultural invoices, insurance claims, or financial correspondence, a missing or weak DMARC policy means those messages may never arrive. The 95 domains with no DMARC record at all are the most exposed, but the 283 at p=none are also at risk as enforcement tightens across all major mailbox providers.
Compliance pressure spans every major North Central industry
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data, hitting financial services, retail, and manufacturing companies across the region. NIS2 applies to any North Central firm with EU operations or clients. Cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For defense contractors in Ohio and North Dakota, CMMC and NIST frameworks already recommend DMARC as a baseline control. And for pharmaceutical companies in Indiana, FDA supply chain integrity guidance increasingly references email authentication as part of vendor verification.
Protect your domain with Red Sift OnDMARC
North Central organizations face a mix of pressures: manufacturing supply chain fraud targeting, agricultural commodity complexity, financial services transaction volume, and defense installation security. Red Sift OnDMARC is built for that complexity.
- Enforcement in 6 to 8 weeks: Manual DMARC projects average around 32 weeks. OnDMARC cuts that to 6 to 8 weeks by automating source identification, SPF and DKIM configuration, and enforcement readiness checks. For the 210 North Central organizations sitting at p=quarantine, the final step to reject could be measured in weeks, not months.
- Dynamic SPF for complex sender lists: North Central organizations tend to have long lists of authorized email senders: manufacturing ERP systems, commodity trading platforms, insurance claims processors, logistics tools, financial transaction systems, and marketing platforms. SPF records have a hard limit of 10 DNS lookups, and complex organizations blow past that quickly. Red Sift’s Dynamic SPF manages this automatically, keeping authentication valid without manual record management.
- Clear reporting across every domain: OnDMARC converts raw DMARC aggregate and forensic reports into a dashboard that shows every service sending email on behalf of your domains. Security and compliance teams get immediate visibility into what’s authorized, what’s failing authentication, and what needs fixing. No XML parsing. No guesswork.
- Continuous monitoring for regulated industries: Manufacturing, financial services, defense, pharmaceutical, and agricultural organizations all face ongoing audit and compliance requirements. OnDMARC provides continuous monitoring and alerting, so enforcement holds even as new senders are added, domains change hands, or infrastructure evolves through mergers and acquisitions.
41% enforcement across the North Central region puts it ahead of the Northeast (35%) and Heartland (36%), but still behind the Mid-Atlantic (44%). Iowa’s 49% shows the path works. South Dakota’s 26% shows how far some states still need to go. For the 588 organizations that haven’t reached full enforcement, Red Sift OnDMARC can close the gap between the region’s risk exposure and its current email security posture.
Get a short overview of Red Sift OnDMARC
Jack leads content, PR, GEO, and email security research at Red Sift.






