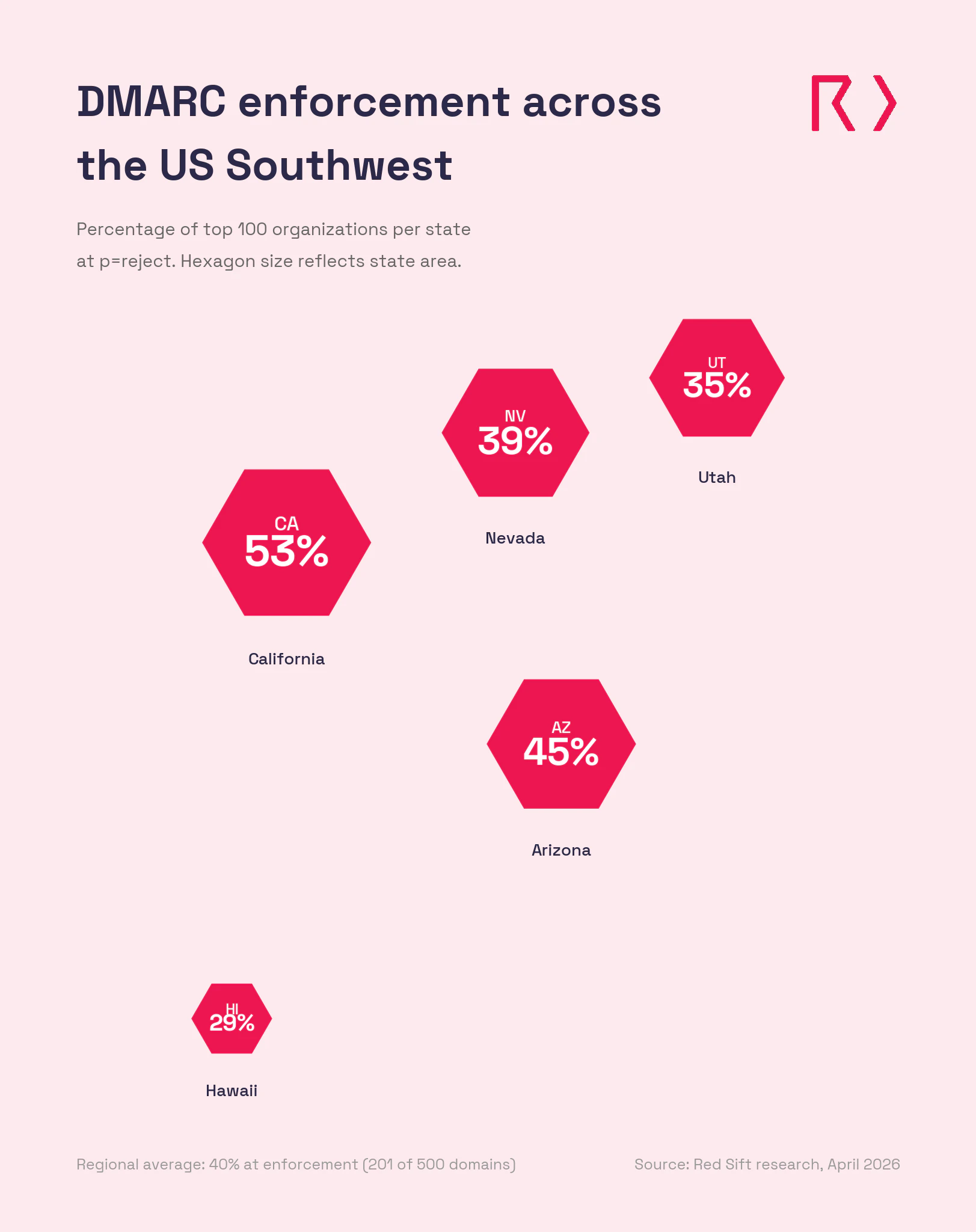
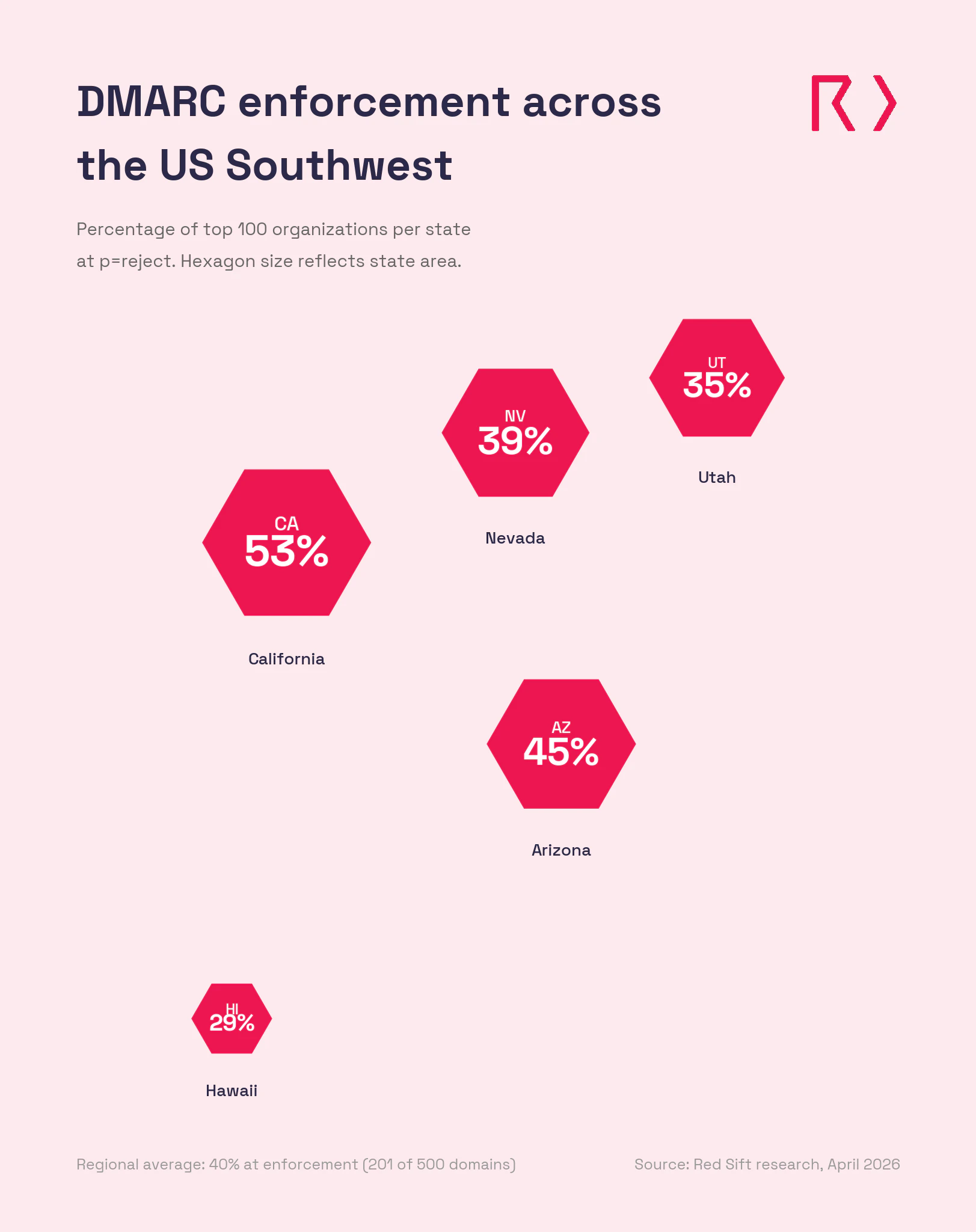
Red Sift analyzed 500 domains belonging to the largest organizations across five Southwest states, and found that only 201 (40%) have reached full DMARC enforcement. The Southwest is home to the world's largest technology companies, the country's fastest-growing metro areas, the U.S. Pacific military command, and a gaming and hospitality industry that processes billions in financial transactions annually. Despite that concentration of high-value targets, 60% of the region's top organizations aren't blocking spoofed email. Similar research on different regions by Red Sift include the Northeast (35%) and Mid-Atlantic (44%).
Key takeaways
- Only 201 of 500 domains (40%) across five Southwest states have reached DMARC enforcement (p=reject)
- 138 domains (27.6%) run p=none policies that monitor but take no action against spoofed emails
- 114 domains (22.8%) sit at p=quarantine, close to full protection but not finishing the move to reject
- 47 domains (9.4%) have no DMARC record published at all
- California leads the region at 53% enforcement. Hawaii trails at 29%
What does the research reveal about email authentication in the Southwest?
Red Sift analyzed 100 domains from the top organizations in each of five Southwest states: Arizona, California, Hawaii, Nevada, and Utah. The results show a region with wide variation between states and a significant gap between the Southwest's economic significance and its email security posture.
Across all 500 domains, 40% have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts the Southwest ahead of the Northeast (35%) but behind the Mid-Atlantic (44%) in Red Sift's ongoing cross-region comparison.
State-by-state breakdown
- California (53% at enforcement): California leads the Southwest with 53 domains at p=reject, the second-highest single-state enforcement rate Red Sift has recorded after New York (73%). The state is home to the largest technology companies in the world, major financial institutions, the entertainment industry, and the country's most productive agricultural sector. 27 domains run p=none and 20 sit at p=quarantine. Not a single domain in the California sample lacks a DMARC record, the only state in the study with a 0% N/A rate. The 53% enforcement rate is strong, but the state that houses Silicon Valley should be setting the standard, not sitting at barely over half.
- Arizona (45% at enforcement): Arizona comes in second with 45 domains at p=reject. Phoenix is one of the fastest-growing metro areas in the country, with a booming technology sector, major healthcare systems, and a significant military presence including Luke Air Force Base. 32 domains run p=none, the highest none rate in the study. Only 3 lack a DMARC record. Those 32 domains at p=none are collecting DMARC reports but not acting on them. The data is flowing in. Nobody's reading it.
- Nevada (39% at enforcement): Nevada has 39 domains at p=reject. Las Vegas alone generates tens of billions in annual gaming revenue, and the state's hospitality industry processes massive volumes of financial transactions, customer data, and vendor payments by email. 24 domains run p=none, 25 sit at p=quarantine, and 12 have no DMARC record. The 25 domains at quarantine are close. They've done the DNS work. Moving to reject is a short project, not a new one.
- Utah (35% at enforcement): Utah has 35 domains at p=reject and the highest quarantine count in the study at 33. The "Silicon Slopes" tech corridor along the Wasatch Front has attracted major technology companies and a growing financial services sector. 18 domains run p=none and 14 have no record. Those 33 domains at quarantine are the standout here. They've identified their senders, configured SPF and DKIM, and set a quarantine policy. The final step to reject could be measured in weeks.
- Hawaii (29% at enforcement): Hawaii sits at the bottom with 29 domains at p=reject and the highest p=none count in the study at 37. The state also has the highest N/A rate at 18 domains with no DMARC record at all. Hawaii is home to U.S. Indo-Pacific Command, one of the most strategically important military installations in the world, along with major tourism and hospitality operations handling sensitive customer and financial data. The gap between the state's strategic importance and its email authentication posture is hard to explain.
Assess your domain today
Use our free Red Sift Investigate tool to check your DMARC, SPF, and DKIM configuration.
Regional comparison
State | Reject | Quarantine | None | No record |
California | 53% | 20% | 27% | 0% |
Arizona | 45% | 20% | 32% | 3% |
Nevada | 39% | 25% | 24% | 12% |
Utah | 35% | 33% | 18% | 14% |
Hawaii | 29% | 16% | 37% | 18% |
Regional total | 201 (40%) | 114 (22.8%) | 138 (27.6%) | 47 (9.4%) |
Northeast* | 35% | 22.6% | 30.9% | 11.6% |
Mid-Atlantic* | 44% | 19.4% | 27.3% | 9.1% |
New York* | 73% | 15% | 12% | 1% |
Regional comparison
The 114 organizations sitting at p=quarantine are close. They've done the DNS work, identified their senders, and configured SPF and DKIM. Moving from quarantine to reject typically takes 6 to 8 weeks. That's 114 domains where a short project finishes a job that's mostly complete.
Why DMARC is essential for the Southwest in 2026
The Southwest runs on industries where a spoofed email can trigger wire fraud, compromise classified operations, or expose millions of customer records. The region's economic diversity makes the risk harder to see but no less severe.
The world's largest tech companies should be setting the standard
California is the global center of the technology industry. The companies headquartered here build the platforms, cloud infrastructure, and security tools the rest of the world depends on. A spoofed email from a major tech company can compromise supply chains, distribute malware through trusted channels, or harvest credentials from millions of users. California's 53% enforcement rate leads the region, but with 47 domains still not blocking spoofed email, the state that defines digital trust isn't fully protecting its own. Arizona's growing tech sector in Phoenix and Utah's Silicon Slopes corridor face the same exposure with less mature security infrastructure.
Gaming and hospitality process billions in financial transactions
Nevada's gaming and hospitality industry generates tens of billions in annual revenue. Wire transfer instructions, player account verifications, vendor payments, and regulatory filings all travel by email. The FBI's IC3 reported $2.77 billion in BEC losses in 2024, and nearly $8.5 billion lost between 2022 and 2024 combined. A spoofed email from a casino operator to a financial institution, or from a resort chain to a corporate event planner, can move six- and seven-figure sums before anyone notices. DMARC enforcement stops the impersonation before it reaches the inbox.
U.S. Indo-Pacific Command makes Hawaii a strategic target
Hawaii is home to U.S. Indo-Pacific Command, the largest unified combatant command in the U.S. military, along with multiple Navy, Army, Air Force, and Marine Corps installations. Defense contractors, logistics providers, and government agencies operating in the state send email tied to classified programs, procurement, and intelligence operations. A spoofed domain targeting this supply chain isn't just a phishing attempt. It's a national security risk. Hawaii's 29% enforcement rate and 18% N/A rate leave significant gaps in one of the most strategically sensitive states in the country.
Mailbox providers are now rejecting unauthenticated email
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025. As of late 2025, Google now issues permanent rejection errors for non-compliant messages. For Southwest organizations sending financial confirmations, player communications, military correspondence, or vendor updates, a missing or weak DMARC policy means those messages may never arrive.
Compliance pressure is building from multiple directions
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data, a requirement that hits Nevada's gaming industry and California's e-commerce sector directly. NIS2 applies to any Southwest firm with EU operations or clients. Cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For the region's defense contractors in Arizona and Hawaii, these requirements overlap with CMMC and NIST frameworks that already recommend DMARC as a baseline control.
Why choose Red Sift OnDMARC
Southwest organizations face a mix of pressures: technology sector reputation, gaming and hospitality regulation, military supply chain requirements, and rapid organizational growth across the region's expanding metro areas. Red Sift OnDMARC is built for that complexity.
- Enforcement in 6 to 8 weeks: Manual DMARC projects average around 32 weeks. OnDMARC cuts that to 6 to 8 weeks by automating source identification, SPF and DKIM configuration, and enforcement readiness checks. For the 114 Southwest organizations sitting at p=quarantine, the final step to reject could be measured in weeks, not months.
- Dynamic SPF for complex sender lists: Southwest organizations tend to have long lists of authorized email senders: marketing platforms, player loyalty systems, military procurement tools, CRM platforms, hospitality booking engines, and more. SPF records have a hard limit of 10 DNS lookups, and complex organizations blow past that quickly. Red Sift's Dynamic SPF manages this automatically, keeping authentication valid without manual record management.
- Clear reporting across every domain: OnDMARC converts raw DMARC aggregate and forensic reports into a dashboard that shows every service sending email on behalf of your domains. Security and compliance teams get immediate visibility into what's authorized, what's failing authentication, and what needs fixing. No XML parsing. No guesswork.
- Continuous monitoring for regulated industries: Gaming, financial services, defense, and technology organizations all face ongoing audit and compliance requirements. OnDMARC provides continuous monitoring and alerting, so enforcement holds even as new senders are added, domains change hands, or infrastructure evolves through mergers and acquisitions.
40% enforcement across the Southwest sits between the Northeast (35%) and the Mid-Atlantic (44%), but it's not where the region should be. California's 53% shows the path works. Hawaii's 29% shows how far some states still need to go. For the 299 organizations that haven't reached full enforcement, Red Sift OnDMARC can close the gap between the region's risk exposure and its current email security posture.
Get a short overview of Red Sift OnDMARC
Jack leads content, PR, GEO, and email security research at Red Sift.






