Key takeaways
- 50.5% of Boston's top organizations have reached DMARC enforcement (p=reject), meaning 49.5% remain exposed
- 22 domains (22.2%) have no meaningful DMARC protection at all, running either p=none or no DMARC record
- 27 domains (27.3%) are stuck at quarantine, just weeks away from full protection but not finishing the job
- Google, Microsoft, and Yahoo now reject non-compliant bulk email at the SMTP level, making enforcement a deliverability issue as much as a security one
What does the research reveal regarding email authentication?
Red Sift's latest DMARC compliance analysis looked at 99 domains belonging to Boston's top organizations. The results paint a clear picture: this city's businesses are split almost evenly between protected and exposed.
Just over half, 50 domains (50.5%), have reached p=reject. That's the DMARC policy level that actually blocks spoofed emails from reaching inboxes. The other 49 domains? They're either partially protected or completely open to impersonation.
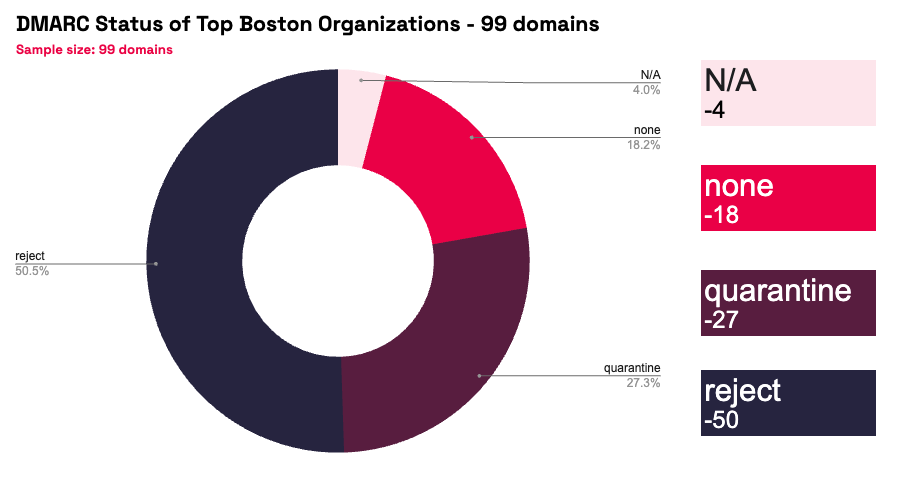
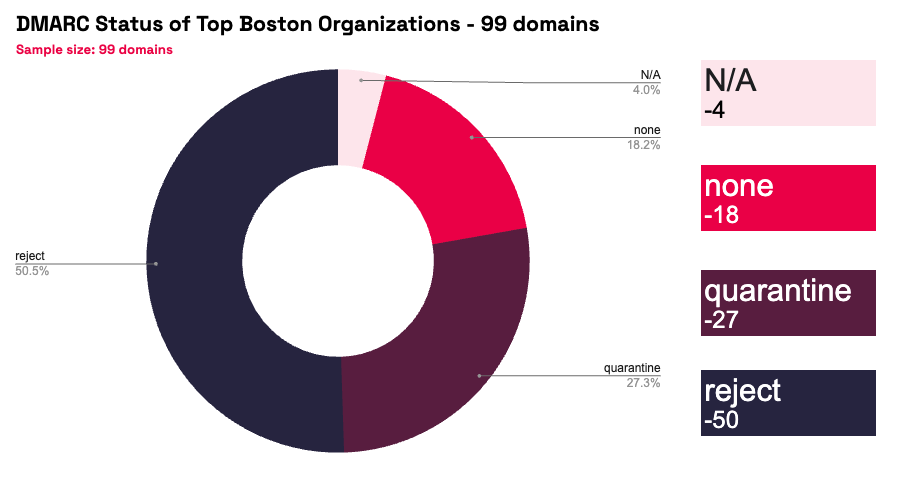
22 of those 49 domains have no effective DMARC protection whatsoever. That includes 18 domains running a p=none policy (which monitors but takes zero action against spoofed emails) and 4 domains with no DMARC record published at all.
The remaining 27 domains sit at p=quarantine. These organizations have done most of the work. Their spoofed emails get flagged and routed to spam folders. But they haven't taken the final step to reject, which means fraudulent messages can still reach recipients.
For a city that's home to major financial services firms, healthcare providers, universities, and technology companies, a 49.5% vulnerability rate is a problem worth fixing.
Why DMARC is essential in 2026
Two years ago, DMARC was a best practice. In 2026, it's a baseline requirement. Three things changed.
The major mailbox providers now reject unauthenticated email
Google and Yahoo started requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025. As of late 2025, Google moved to strict SMTP-level enforcement, meaning non-compliant emails now receive permanent rejection errors (550 codes) rather than temporary deferrals.
These three providers control over 80% of global email infrastructure. If your domain doesn't meet their authentication standards, your emails don't reach customers. That's not a security risk. That's a business continuity problem.
BEC losses keep climbing
The FBI's IC3 reported $2.77 billion in business email compromise losses in 2024, with 21,442 complaints filed. BEC was the second most financially damaging cybercrime category, behind only investment fraud. Total reported cybercrime losses hit $16.6 billion in 2024, a 33% jump from the year before.
BEC attacks rely on email impersonation. An attacker sends an email that appears to come from a trusted executive, supplier, or partner, and convinces the recipient to transfer funds or share sensitive data. DMARC at enforcement (p=reject) blocks these spoofed messages before they reach the target.
Compliance frameworks now mandate it
PCI DSS 4.0.1 requires DMARC for organizations handling payment card data. The UK's NCSC has long recommended enforcement-level DMARC for public sector organizations. NIS2 across the EU pushes similar email authentication requirements. For regulated industries in Boston (financial services, healthcare, education), DMARC isn't optional. It's a compliance obligation.
It's also a deliverability issue
This isn't just about security. Organizations without DMARC enforcement risk having legitimate emails rejected or routed to spam by Google, Microsoft, and Yahoo. Marketing campaigns, invoices, customer communications, and partner correspondence all depend on deliverability. A missing or weak DMARC policy now directly impacts revenue.
Why choose Red Sift OnDMARC
Red Sift OnDMARC is built for organizations that want to reach DMARC enforcement quickly and stay there.
- Get to enforcement in weeks, not months: The industry average for DMARC implementation is around 32 weeks using manual approaches. Red Sift OnDMARC typically gets organizations to p=reject in 6 to 8 weeks. The platform automates the complex parts: identifying all legitimate sending sources, managing SPF and DKIM configurations, and providing clear guidance on what to fix and when.
- Dynamic SPF that prevents configuration drift: SPF records have a hard limit of 10 DNS lookups. As organizations add more third-party email services (marketing platforms, CRMs, ticketing systems, billing tools), they quickly hit that ceiling. Red Sift's Dynamic SPF technology manages this automatically, keeping SPF valid without manual record juggling.
- Full visibility across every sending source: OnDMARC processes DMARC aggregate and forensic reports into a clear dashboard that shows exactly who's sending email on behalf of your domain, whether it's authorized, and whether it's passing authentication. No more parsing raw XML. No more guessing which third-party service is misconfigured.
- Built for complex environments: Boston's largest organizations don't run simple email setups. They use dozens of third-party senders, manage multiple domains and subdomains, and operate across departments that each have their own tools. OnDMARC is designed for this complexity, with multi-domain management, granular reporting, and integrations that scale as your email infrastructure grows.
- Ongoing monitoring after enforcement: Reaching p=reject isn't the finish line. New sending services get added. Configurations drift. Acquisitions bring new domains into scope. OnDMARC provides continuous monitoring and alerting so your DMARC posture stays enforced, even as your email ecosystem changes.
For the 27 Boston organizations currently at quarantine, the move to reject is within reach. For the 22 with no effective protection, the time to start is now.
Jack leads content, PR, GEO, and email security research at Red Sift.






