Key takeaways
- 57 domains (57%) have reached DMARC enforcement (p=reject), leaving 43% exposed
- 21 domains (21%) run p=none policies that monitor but take no action against spoofed emails
- 20 domains (20%) sit at quarantine, close to full protection but not finishing the move to reject
- 2 domains (2%) have no DMARC record published at all
What does the research reveal regarding email authentication?
Washington D.C. has a DMARC problem that's hard to ignore given the city's role in shaping cybersecurity standards for the rest of the country.
Red Sift's analysis of 100 domains belonging to D.C.'s top organizations found that 57 (57%) have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts D.C. ahead of Boston (50.5%) but well behind New York (72.7%) in Red Sift's cross-city comparison.
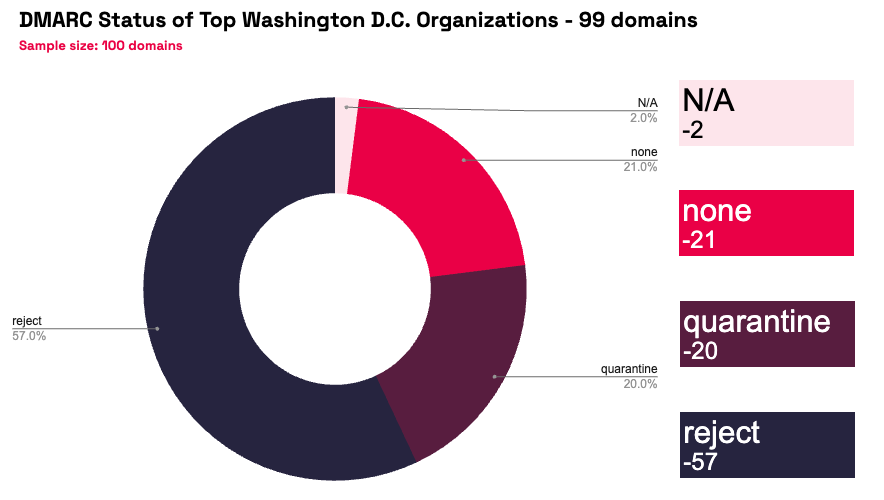
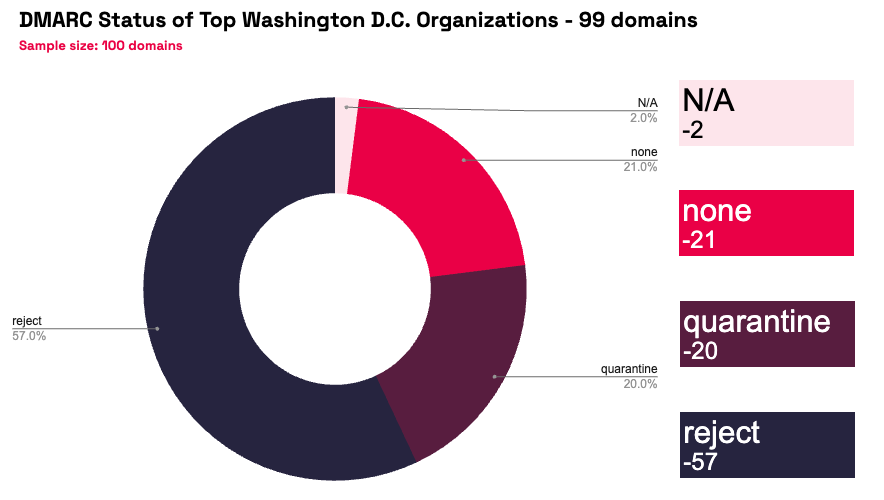
The remaining 43 domains break into three groups. 20 sit at p=quarantine, where spoofed emails get routed to spam but aren't blocked outright. These organizations have done most of the technical work, and the move to enforcement typically takes 6 to 8 weeks. 21 domains run p=none, which means they've published a DMARC record but it does nothing to stop fraudulent emails from landing in inboxes. And 2 domains have no DMARC record at all.
That 43% gap is notable for a city that houses CISA, NIST, the NSA, and the federal agencies that set the cybersecurity agenda for both government and the private sector. D.C. is where the rules get written. But a significant share of its top organizations aren't following them.
Why DMARC is essential in 2026
D.C. sits at the intersection of government, lobbying, defense contracting, and policy. Every one of those sectors depends on trusted email communication. And every one of them is a prime target for impersonation attacks.
The city runs on trust, and email is how that trust gets exploited
Government affairs, procurement, policy coordination, and lobbying all rely heavily on email. BEC attackers know this. A spoofed email from a government contractor to a federal agency, or from a lobbying firm to a congressional office, can trigger wire transfers, expose sensitive information, or compromise ongoing negotiations. The FBI's IC3 reported $2.77 billion in BEC losses in 2024, and nearly $8.5 billion lost between 2022 and 2024 combined. D.C.'s concentration of high-value, trust-dependent communication makes it a rich target.
Federal mandates already push DMARC adoption
CISA's Binding Operational Directive 18-01 required federal agencies to implement DMARC at enforcement back in 2017. NIST guidelines recommend DMARC as a core email security control. The irony is that while the federal government has driven DMARC adoption across its own agencies, the broader D.C. business community, including the contractors, consultancies, and firms that work alongside government, hasn't kept pace. A federal agency with strong DMARC is still vulnerable if a trusted contractor's domain can be spoofed.
Mailbox providers have moved from guidelines to enforcement
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025. As of late 2025, Google now issues permanent rejection errors for non-compliant messages. For D.C. organizations sending procurement updates, policy briefs, event invitations, or stakeholder communications, a missing or weak DMARC policy means those messages may never arrive.
Compliance pressure is building from multiple directions
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data. NIS2 applies to any D.C. firm with EU operations or clients. And cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For D.C.'s defense contractors and government services firms, DMARC is becoming a contract requirement, not just a best practice.
Why choose Red Sift OnDMARC
D.C. organizations operate in a uniquely complex environment: government compliance requirements, multi-stakeholder communication chains, classified and sensitive information flows, and vendor ecosystems that span the public and private sectors. Red Sift OnDMARC is built for that complexity.
- Enforcement in 6 to 8 weeks: Manual DMARC projects average around 32 weeks. OnDMARC accelerates that to 6 to 8 weeks by automating source identification, SPF and DKIM configuration, and enforcement readiness checks. For the 20 D.C. organizations at quarantine, the final step to reject could be measured in weeks.
- Dynamic SPF for sprawling sender lists: D.C. organizations tend to have long lists of authorized email senders: government portals, CRM platforms, event management tools, marketing services, and more. SPF records have a hard limit of 10 DNS lookups, and it's easy to exceed that in a complex environment. Red Sift's Dynamic SPF manages this automatically, keeping authentication valid without manual record management.
- Clear reporting across every domain: OnDMARC converts raw DMARC aggregate and forensic reports into a dashboard that shows every service sending email on behalf of your domains. Security and compliance teams get immediate visibility into what's authorized, what's failing authentication, and what needs fixing. No XML parsing. No guesswork.
- Continuous monitoring for organizations that can't afford drift: Government contractors and regulated firms face ongoing audit and compliance requirements. OnDMARC provides continuous monitoring and alerting, so enforcement holds even as new senders are added, domains change hands, or infrastructure evolves through mergers and acquisitions.
D.C. sets the cybersecurity standard for the rest of the country. The 57% of organizations already at enforcement have proven it's achievable. For the 43% that haven't, the gap between policy and practice is one that Red Sift OnDMARC can close.
Jack leads content, PR, GEO, and email security research at Red Sift.






