Phishing remains a top driver of breaches and fraud. Financial services are a prime target because email moves money, resets passwords, and confirms identity. Verizon’s 2025 Data Breach Investigations Report again lists social engineering and phishing among the most common paths to incidents. With research by Red Sift previously highlighting the widening gap in U.S. commercial banking, where over 50% remain vulnerable to spoofing attempts.
Criminals now use AI tools to write better lures, localize language, and personalize at scale. Microsoft and industry reporting show attackers using AI to improve phishing success, not just volume, alongside increasing brand impersonations. Social engineering is quickly becoming the go to attack method for many bad actors, as the human link in most companies remains the weakest.
The cost is real. The FBI reports global exposed losses from business email compromise in the tens of billions of dollars, with continued year-over-year growth. Payments redirection and invoice fraud remain common.
What Red Sift’s Fintech research shows
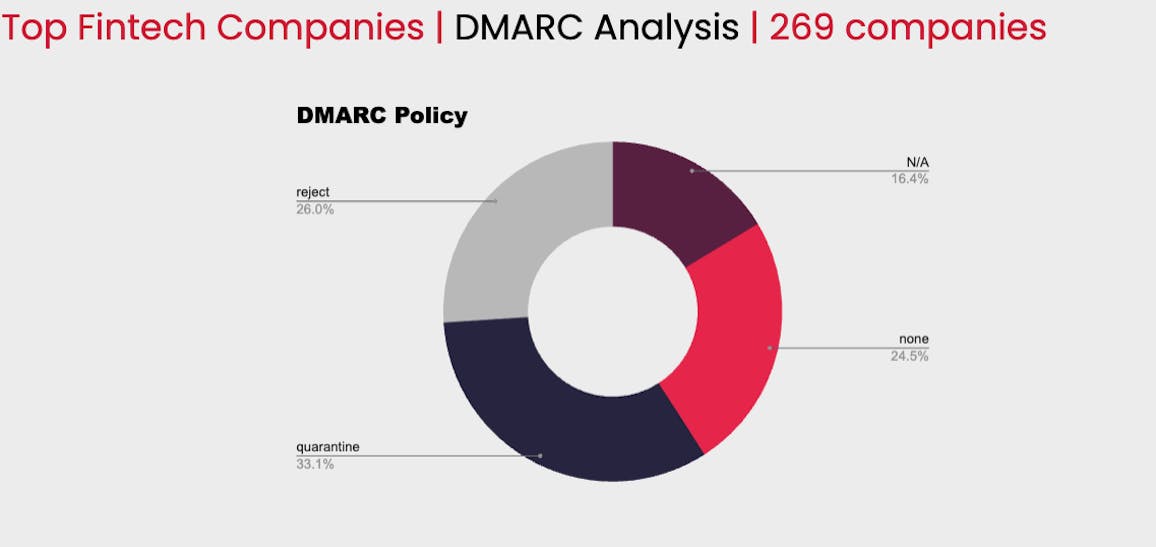
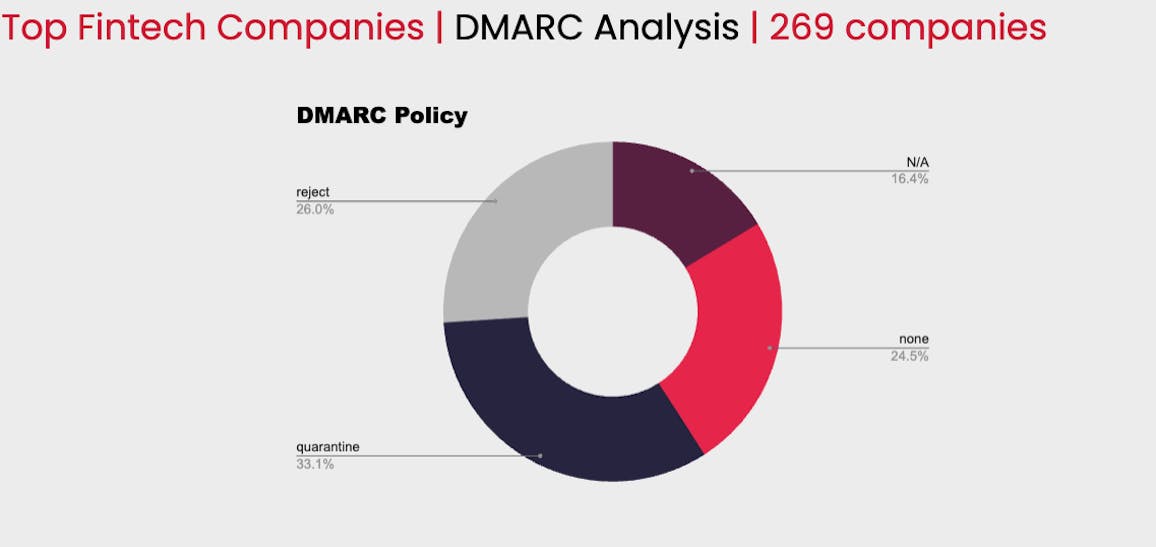
From 269 top Fintech companies:
At enforcement: 159 (59.1%)
- p=reject: 70 (26.0%)
- p=quarantine*: 89 (33.1%)
*some protection but not the strictest form of enforcement found at p=reject
Unprotected: 110 (40.9%)
- p=none: 66 (24.5%)
- no DMARC record: 44 (16.4%)
If you are unprotected, anyone can send “verify a charge,” “update your bank info,” or “reset your password” emails that appear to come from your domain. This is a direct path to account takeover, payment fraud, and data disclosure. Financial sector reports from FS-ISAC and ENISA highlight phishing and social engineering as persistent, high-impact risks for banks, payments, and Fintech firms.
Why this matters to customers
- Account takeover: Users hand over credentials after a convincing “fraud alert.” Attacker drains funds and sets mailbox rules to hide warnings. This is a common pattern in BEC and consumer fraud.
- Payments redirection: Spoofed invoices or payout updates change destination accounts. Losses are often unrecoverable
- Trust erosion: Repeated spoofing trains customers to ignore real alerts. Sector studies warn about downstream fraud and reputational damage.
Why Fintech is so exposed right now
- Many legitimate senders: PSPs, marketing clouds, ticketing, support tools, and product systems all email “as you.” More senders mean more gaps. FS-ISAC notes the convergence of cybercrime and fraud across the financial sector.
- High-value prompts: Statements, chargebacks, payouts, and MFA emails are urgent and easy to mimic. ENISA’s finance overview flags these as common phish lures.
- Better lures through AI: Reports show attackers using AI to craft fluent, targeted emails that bypass simple user checks.
How DMARC, SPF, and DKIM reduce risk
- SPF lists authorized sending hosts for your domain.
- DKIM signs mail so receivers can verify it was not altered.
- DMARC tells receivers what to do when SPF or DKIM fail and aligns identity with the visible From: domain. The DMARC standard is defined in RFC 7489 and is recommended by CISA for phishing defense.
Moving to “p=reject” (enforcement) blocks direct domain spoofing before messages reach inboxes. This reduces successful phishing, lowers BEC risk, and protects customers during high-risk flows such as password resets and payment alerts. CISA guidance stresses that clear governance and phased rollout address the main concerns about “breaking mail.”
Get started on your DMARC journey today with Red Sift OnDMARC.
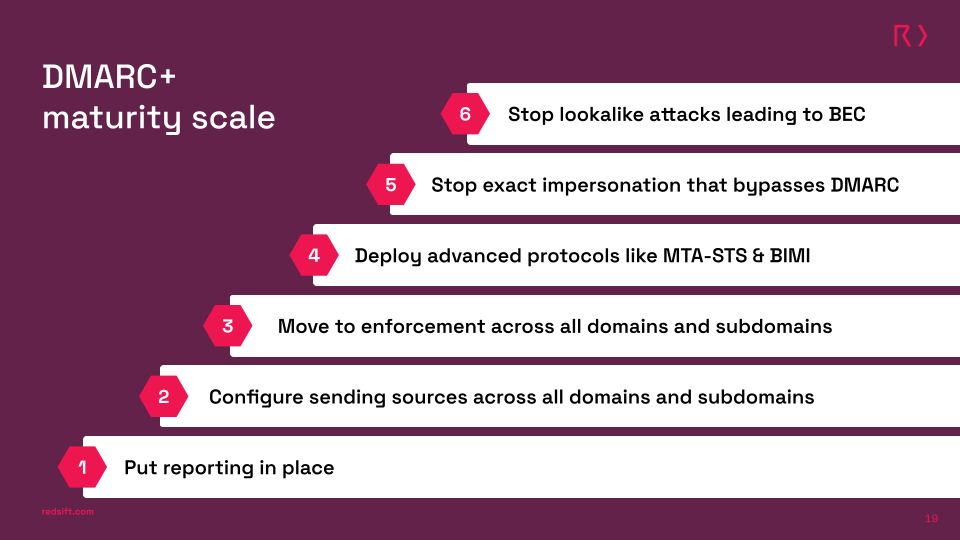
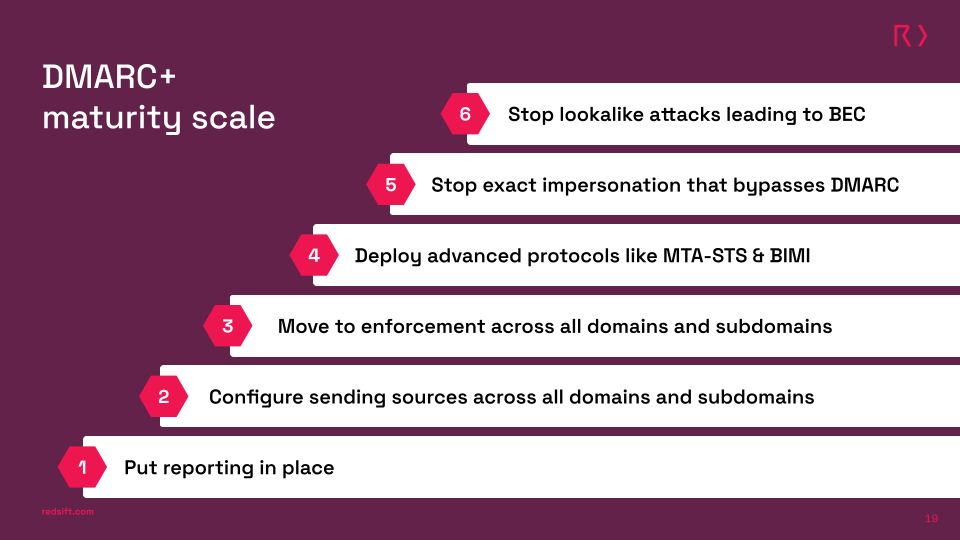
Practical path to enforcement
Turn on visibility:
- Publish a DMARC record on every domain and route reports to a monitored inbox or platform. Start with a monitoring policy (p=none) so you see who is sending on your behalf. Use Microsoft’s aggregate DMARC reports for extra sender detail if you run M365.
Map all senders:
- From your reports, list product mail, marketing platforms, PSPs, support tools, and any unknown sources. Group by vendor and owner.
Fix authentication
- SPF: keep within DNS lookup limits; where you’re hitting limits, use Dynamic/Hosted SPF to simplify maintenance.
- DKIM: enable signing for each sender and align it with the visible From domain. The implementation guide covers alignment checks and common fixes.
Phase to enforcement, stream by stream:
- Move low-risk or well-configured streams to p=quarantine, watch for bounces or gaps, then advance to p=reject. A staged rollout is recommended to avoid mail disruption. Note: Bulk senders including Google, Yahoo and Microsoft now require DMARC at at least p=none.
Prove and maintain
- Track: spoofed mail blocked, unknown senders eliminated, % of traffic aligned, and time to enforcement.
- Keep monitoring. DMARC is not “set and forget”, vendors change keys and routes. Continuous reporting prevents drift that can break delivery even after you reach enforcement.
For Fintech companies looking to keep their customers secure, enforcing DMARC at p=reject is the first practical step to a mature and scaled cybersecurity strategy. From there, the path to stronger protection is as simple as 6 easy steps.
Today the discussion should focus on prevention over cost. For tomorrow might bring questions on the long-lasting damage of an attack and how it could have been mitigated.
Jack leads content, PR, GEO, and email security research at Red Sift.






