Public PKI and digital certificates provide an acceptable baseline for most internet properties, but some carry far greater risk than others. Properties like your application login page, payment flows, corporate domains, and anything that could damage your brand if impersonated are prime targets for attackers. Those properties must be protected by actively building defenses using technologies such as Certificate Transparency (CT) and CAA. While we've gone into great detail before on High-Assurance CT, we wanted to focus on the practical aspects of detecting unauthorized issuances, applying available prevention mechanisms, and configuring high-assurance monitoring with Red Sift Certificates.
What is Certificate Transparency?
Certificate Transparency (CT) is an open standard that requires publicly trusted Certificate Authorities (CAs) to log every certificate they issue to publicly auditable append-only logs. As a result, any certificate issued for your domain is visible to anyone.
CT was designed to address a fundamental weakness in Public PKI: any CA in the trust store can technically issue a certificate for any domain. It doesn't prevent this, but it makes unauthorized issuances detectable. Red Sift has been ingesting and processing CT logs since 2017, building one of the most comprehensive certificate discovery data stores available.
Public PKI failures aren't theoretical; see our history of attacks against public PKIs for incidents that CT and CAA would have caught.
Layer 1: Start with a Basic CAA Policy
The first line of defense is prevention, and that starts with a DNS CAA (Certification Authority Authorization) policy. A CAA policy lets you declare which CAs are permitted to issue certificates for your domain. Without a policy, any CA can issue a certificate for your properties. Even a basic CAA configuration dramatically reduces your attack surface.
Recommended baseline: Basic CAA policy with default CT monitoring settings.
Defining a CAA policy. Now, let's set up a CAA policy with Red Sift Certificates. Before locking anything down, find out who's currently issuing for your domains. Otherwise, a new record could break legitimate issuance overnight. The Issuer facet on the Certificates page surfaces this instantly. Filtering on "Hostnames contains redsift.com", for example, returns Let's Encrypt (114), Google Trust Services (34), Sectigo (24), and Amazon (4).
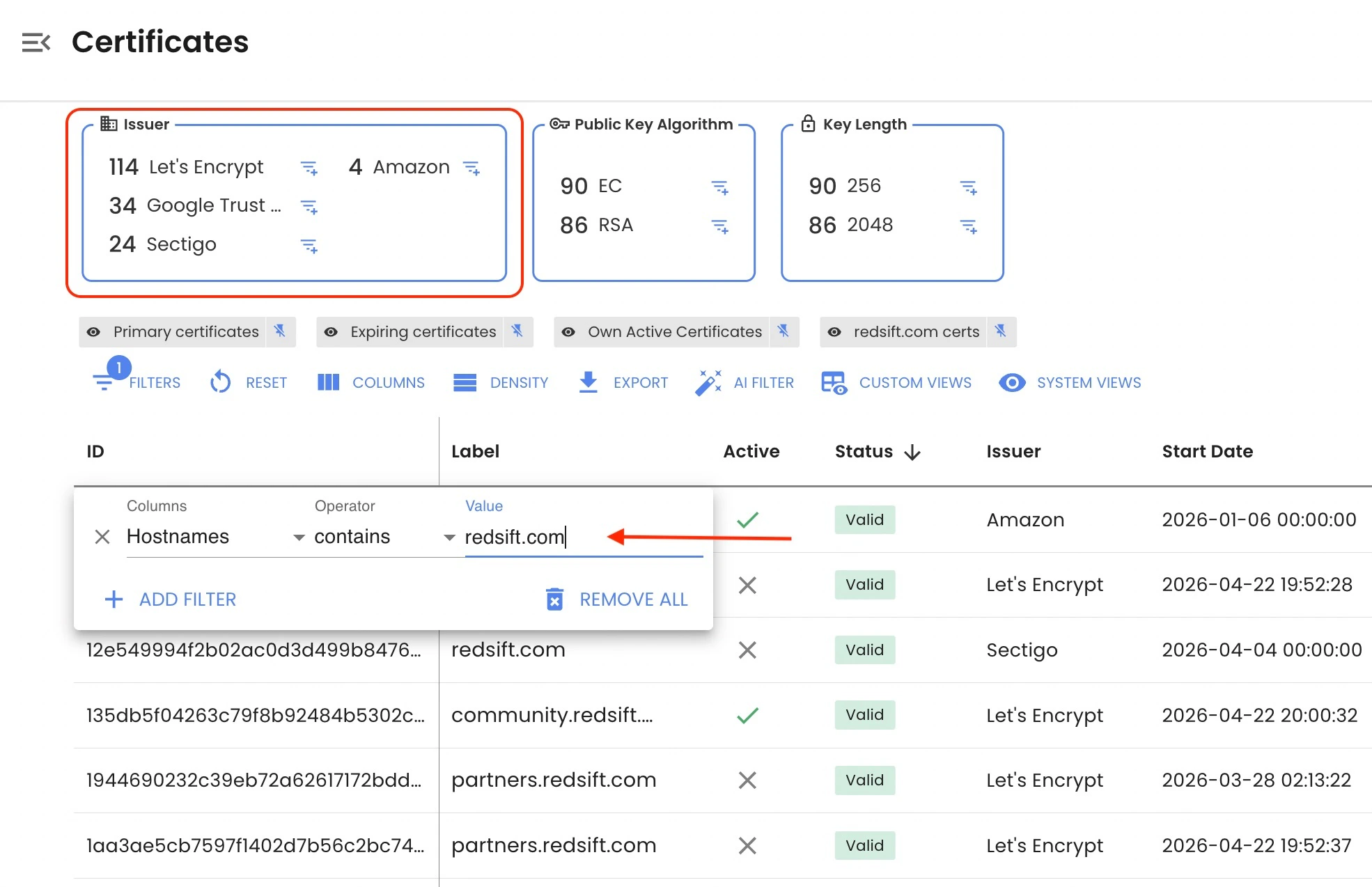
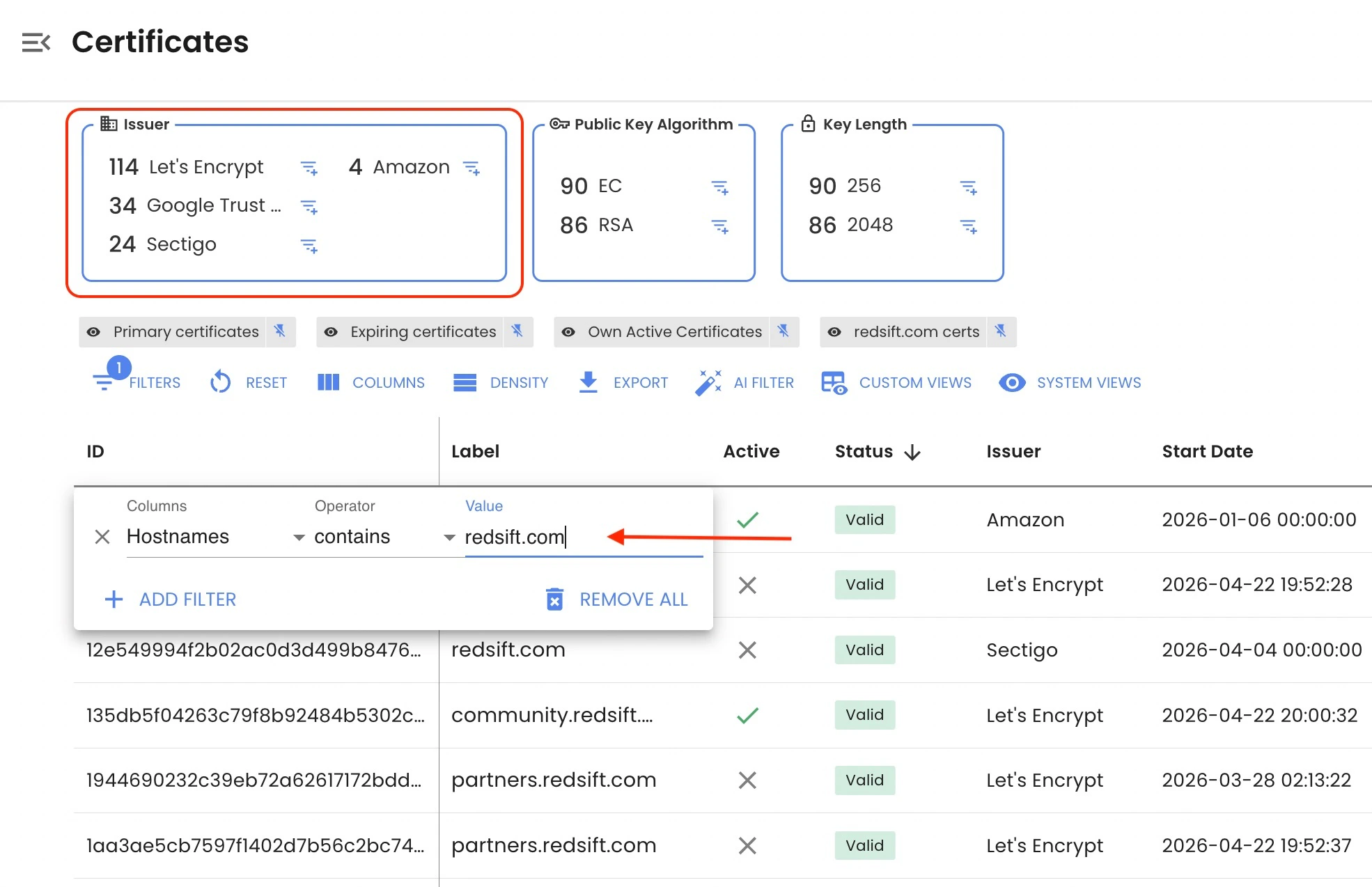
That list translates directly into a CAA policy that you need to set up on your DNS record:
redsift.com. CAA 0 issue "letsencrypt.org" redsift.com. CAA 0 issue "pki.goog" redsift.com. CAA 0 issue "sectigo.com" redsift.com. CAA 0 issue "amazon.com" redsift.com. CAA 0 issuewild "letsencrypt.org" redsift.com. CAA 0 issuewild "pki.goog" redsift.com. CAA 0 issuewild "sectigo.com" redsift.com. CAA 0 iodef "mailto:security@redsift.com"
issue covers regular certificates, and issuewild covers wildcards. Tighten the wildcard list to only the CAs you actually use for wildcard issuance; the "wildcard" filter in Red Sift Certificates, combined with a "hostnames" filter, shows your current wildcard usage. Need some help with the identifier domains? You can use this CAA generator to look up the correct identifier domain for each CA.
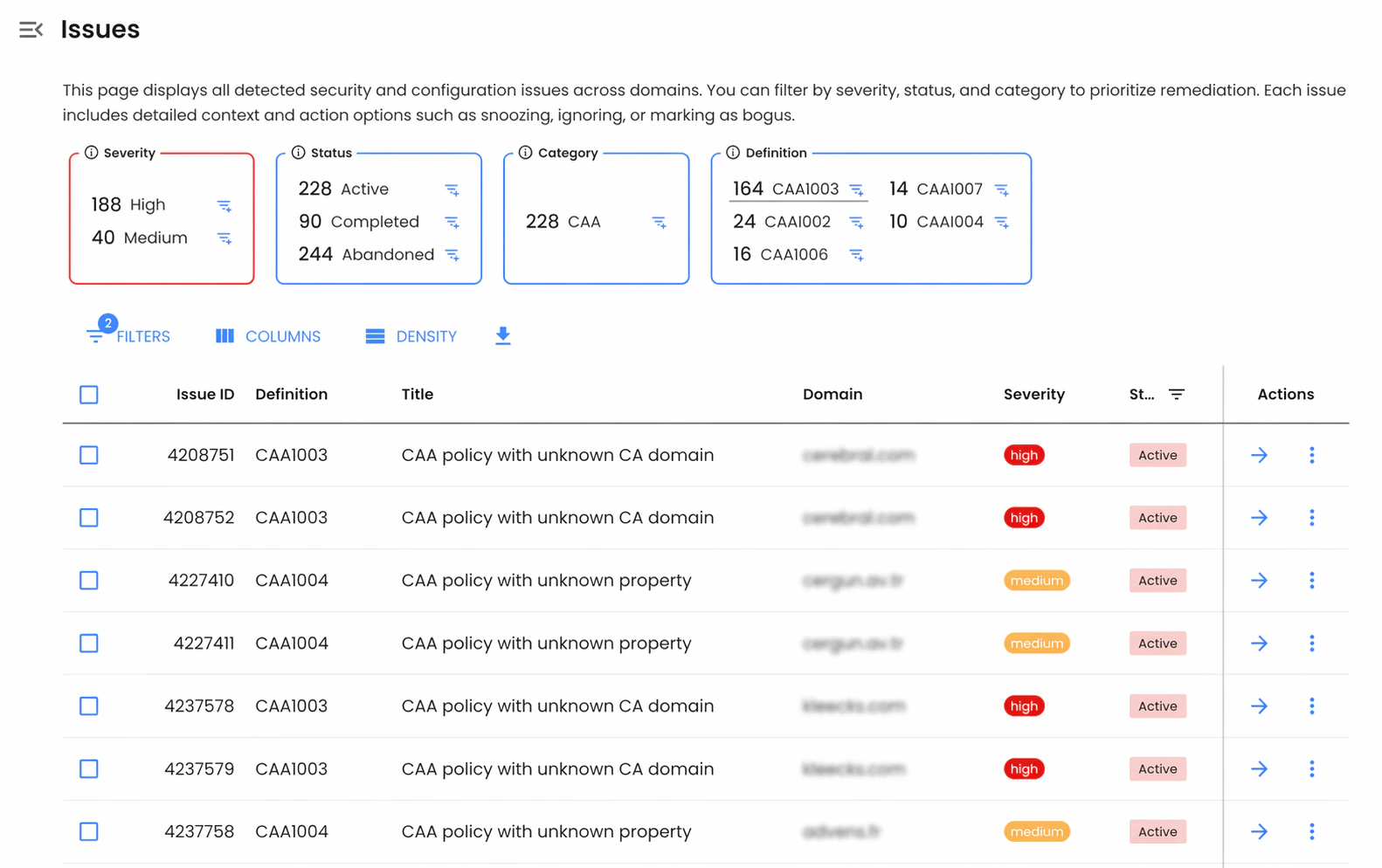
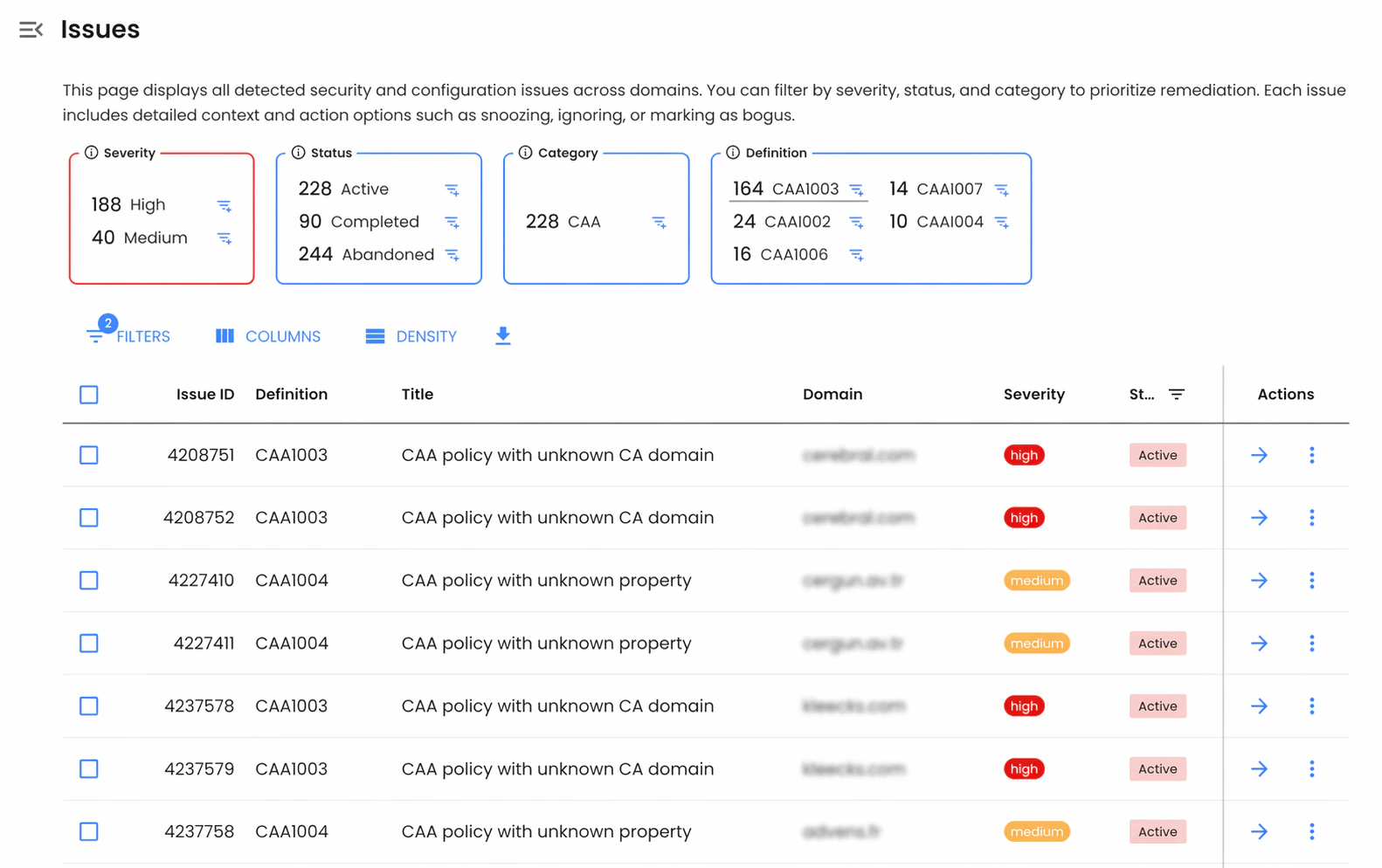
CAs are required to check and honor CAA records before issuance. Should a discovered certificate violate your CAA policy, Red Sift Certificates will flag the CAA configuration issue (for example, like a malformed CAA record or missing property) and push an alert to you for visibility.
Layer 2: Setting up CT Monitoring
CAA prevents compliant CAs from issuing unauthorized certificates, but it doesn't stop a compromised or rogue CA. CT monitoring is how you detect what CAA can't prevent.
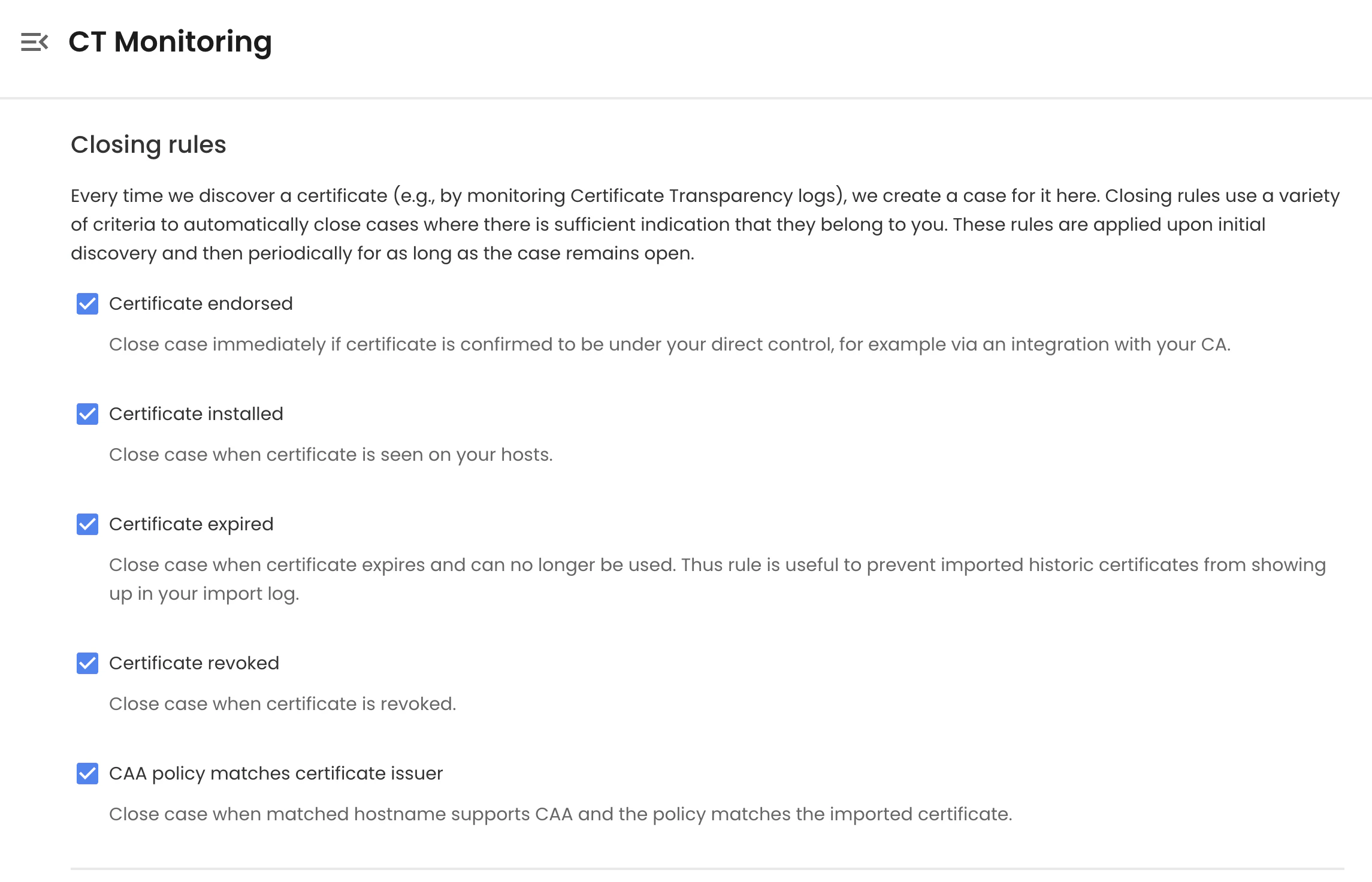
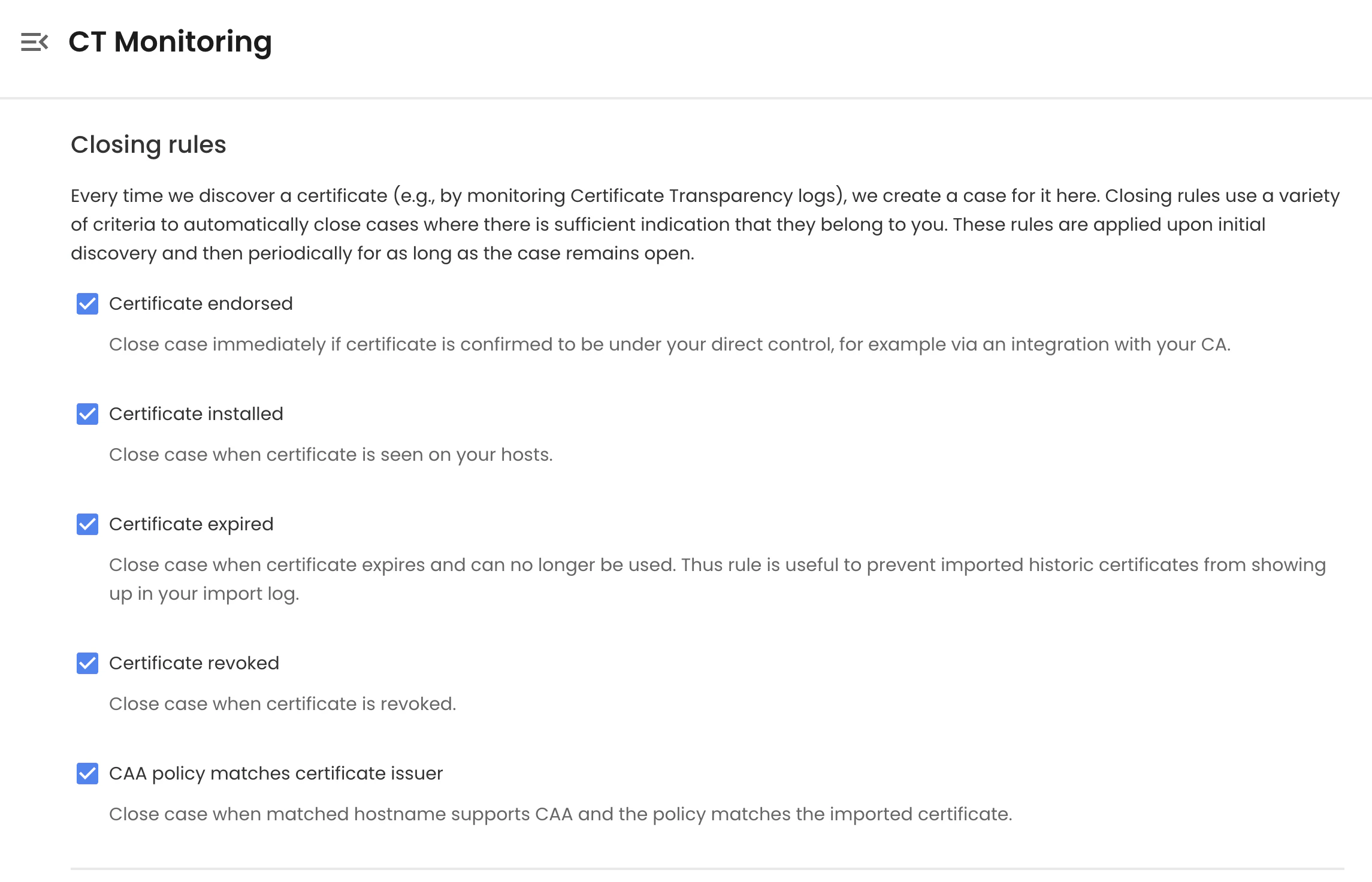
Red Sift Certificates continuously monitors CT logs and creates a case for every newly discovered certificate that matches your domains. Each case is automatically evaluated against a set of closing and escalation rules to determine whether the certificate is legitimate, unexpected, or a potential indicator of compromise.
Closing Rules
Closing rules automatically resolve cases where there is sufficient evidence that the certificate is legitimate:
Closing Rules
Rule | Notes |
Certificate is endorsed (marked known) | Triggered when a certificate is imported via a CA integration or marked via API. These are certificates guaranteed to be under your control, so cases are closed immediately. |
Certificate is installed on your hosts | Confirmed via active host observation |
Certificate is expired | Prevents historic certificates from cluttering the queue |
Certificate is revoked | Closes cases for certificates revoked by the issuing CA and no longer usable |
CAA policy matches certificate issuer | Confirms the CA was authorized to issue. Applies only to hostnames with a CAA record in place |
Issuer matches known keywords | Closes cases where the issuer name matches a trusted keyword list. |
Case has been open for N days without escalation | Auto-closes stale cases that haven't triggered any escalation rule. Recommended: 30 days. |
Layer 3: High-Assurance CT Monitoring
Standard CT monitoring flags anomalies reactively. High-Assurance CT Monitoring takes a more rigorous approach: it builds a complete inventory of every certificate you own, then treats anything in CT logs that isn't in that inventory as suspicious by default.
This requires two things:
- A complete "known-good" inventory. Built by importing certificates via CA integrations or the Create Certificate API. Every imported certificate is automatically marked as endorsed (known to be under your control).
- Tight escalation rules. Configured to escalate any certificate that isn't accounted for within a short window.
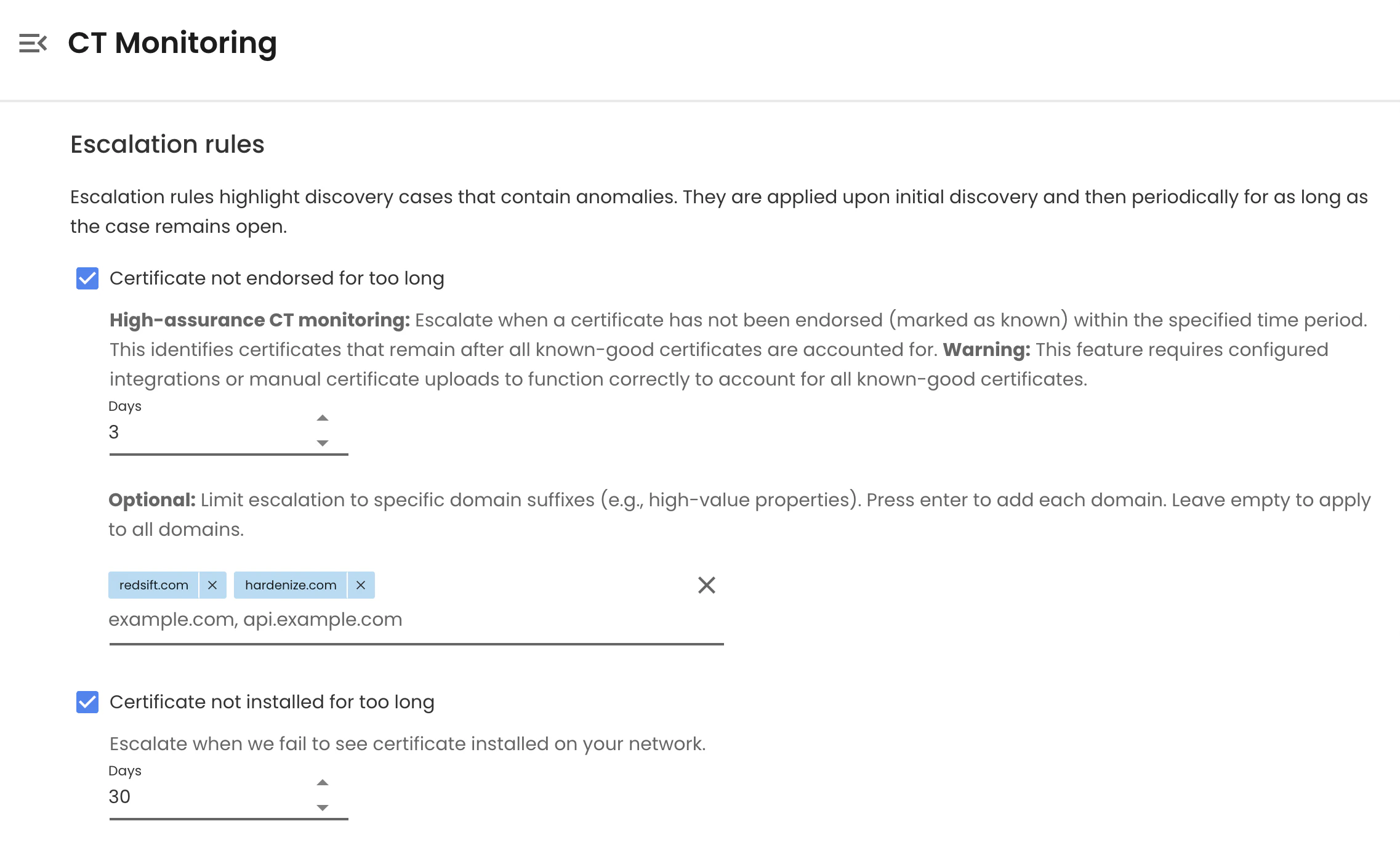
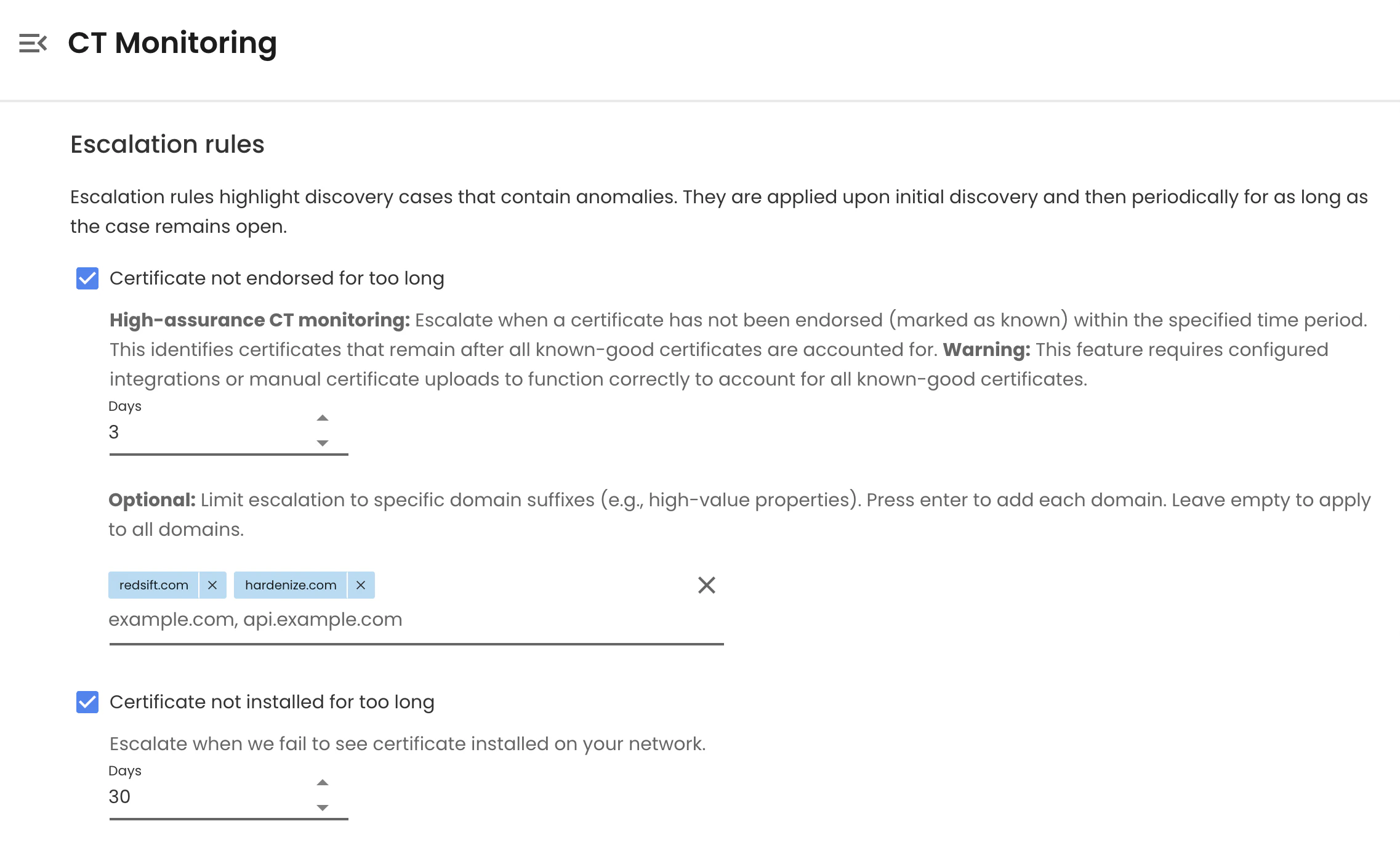
Escalation Rules
Rule | Notes |
Certificate not endorsed within X days | Core high-assurance rule. Recommended: 1-3 days (default is 30). Optionally scope to high-value domains only. |
Certificate not seen installed on hosts | Detects certificates issued but never deployed. Recommended: 30 days. |
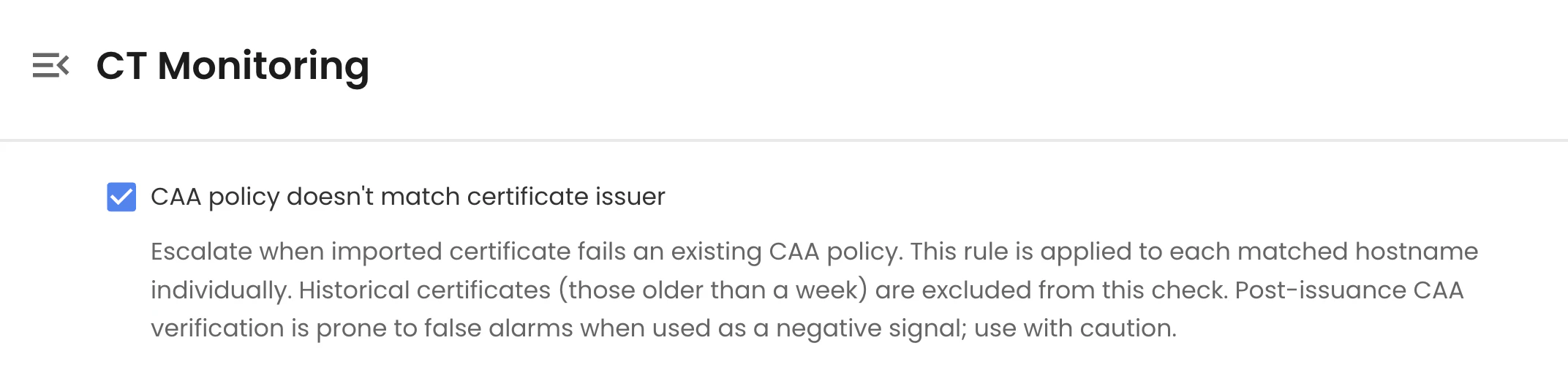
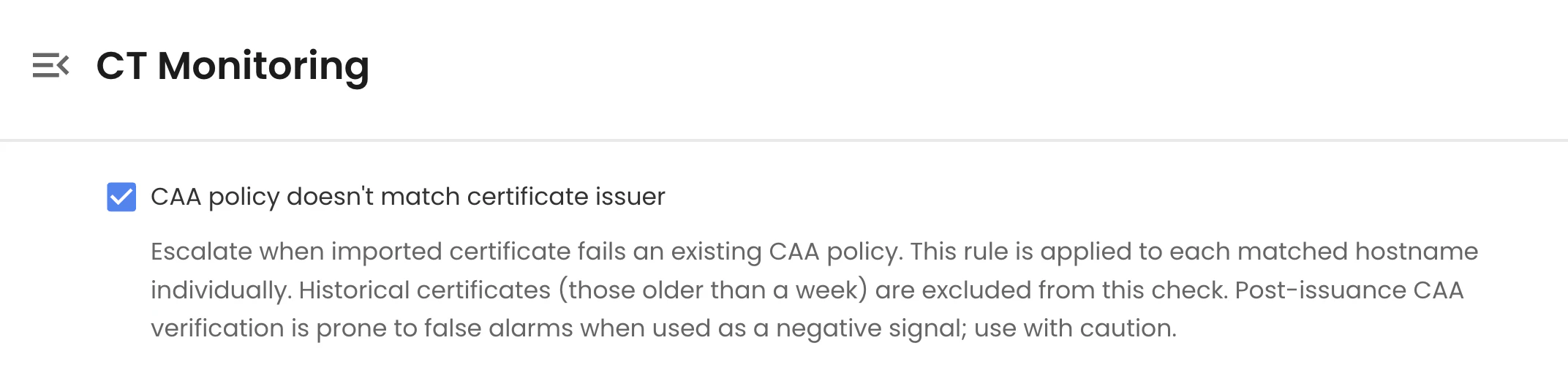
CAA policy doesn't match certificate issuer | Indicates issuance outside your allowed CA policy. Use with caution. |
Certificate is not CT-compliant | May indicate non-standard issuance or a certificate submitted outside normal CA workflows |
Certificate issuer is not in the allowed CA list | Requires defining an explicit allowlist of trusted issuers |
Issuer matches suspicious keywords | E.g., unknown CA names, internal/test CAs, known risky issuers |
Certificate exceeds maximum lifetime | Flags policy violations, e.g., validity over 200 days |
Note: CT logs have an inherent merge delay, up to 24 hours for some logs. Red Sift processes certificates as they appear in CT logs, in near real time but not instantly.
Bringing it all together
Certificate Transparency turns an invisible risk, where any CA can issue for any domain, into a publicly auditable signal. But raw CT data is noisy; turning it into a reliable early-warning system requires a known-good inventory, sensible closing rules, and tight escalation thresholds.
Red Sift Certificates brings these three layers together in one place: CAA policy enforcement, continuous CT monitoring, and high-assurance escalation backed by nearly a decade of CT log ingestion. Start with the recommended baseline, then tighten escalation rules on your highest-value domains as your known-good inventory matures.
Ready to get started? Sign up for a Red Sift Certificates Lite trial, or log in to set up high-assurance CT Monitoring for your domains if you already have an account.
Bhushan is the leading Principal Engineer for Red Sift's Certificate products and innovation.






