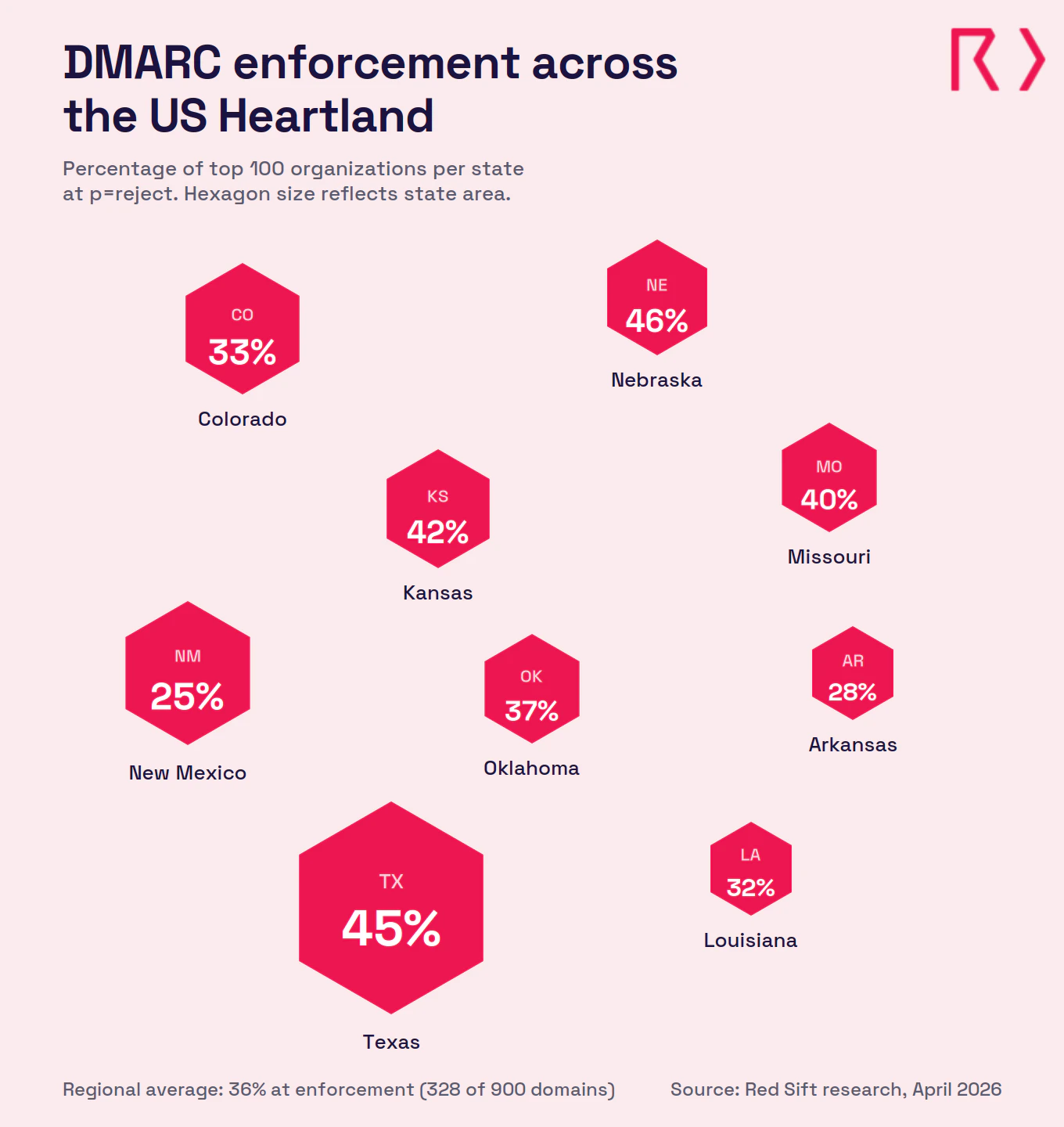
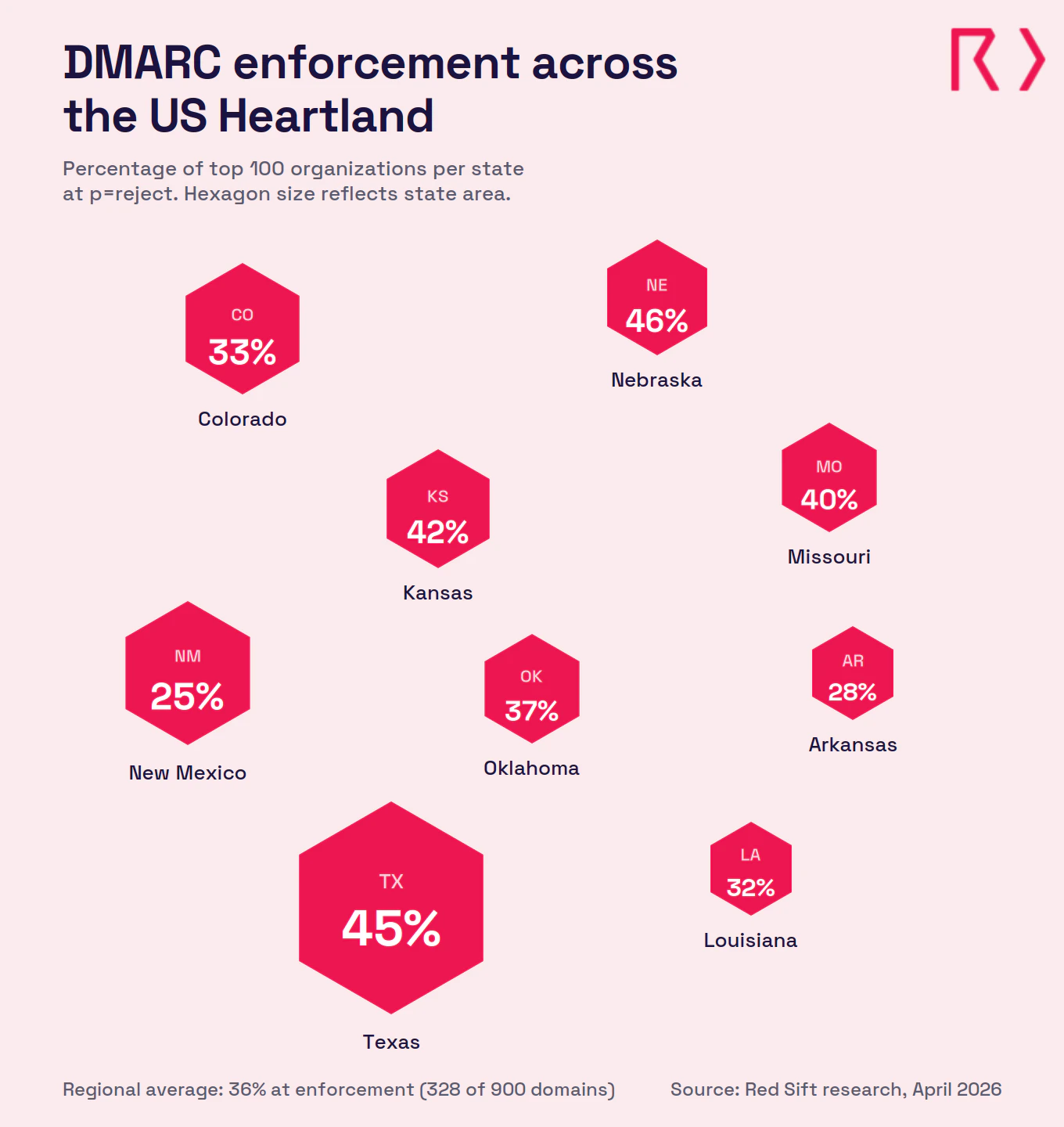
Red Sift analyzed 900 domains belonging to the largest organizations across nine Heartland states, and found that only 328 (36%) have reached full DMARC enforcement. The Heartland powers the country's energy industry, feeds its population, and hosts some of the most strategically sensitive military and research installations in the world. Despite that concentration of critical infrastructure, 64% of the region's top organizations aren't blocking spoofed email. Similar research on different regions by Red Sift includes the Northeast (35%), Mid-Atlantic (44%), and Southwest (40%).
Key takeaways
- Only 328 of 900 domains (36%) across nine Heartland states have reached DMARC enforcement (p=reject)
- 287 domains (31.9%) run p=none policies that monitor but take no action against spoofed emails
- 202 domains (22.4%) sit at p=quarantine, close to full protection but not finishing the move to reject
- 83 domains (9.2%) have no DMARC record published at all
- Nebraska leads the region at 46% enforcement. New Mexico trails at 25%
What does the research reveal about email authentication in the Heartland?
Red Sift analyzed 100 domains from the top organizations in each of nine Heartland states: Arkansas, Colorado, Kansas, Louisiana, Missouri, Nebraska, New Mexico, Oklahoma, and Texas. The results show a region where enforcement rates vary sharply between states and where the gap between critical infrastructure exposure and email security posture is wider than any region Red Sift has studied so far.
Across all 900 domains, 36% have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts the Heartland just one point above the Northeast (35%) and well behind the Mid-Atlantic (44%) and Southwest (40%) in Red Sift's ongoing cross-region comparison.
State-by-state breakdown
- Nebraska (46% at enforcement): Nebraska leads the Heartland with 46 domains at p=reject, the strongest enforcement rate in the study. The state is a major center for insurance, financial services, and agricultural commodities trading, with Omaha serving as headquarters for multiple Fortune 500 companies. 24 domains run p=none, 22 sit at p=quarantine, and 8 have no record. For a state that processes billions in financial transactions and insurance claims, 46% is a solid start but still leaves more than half of its top organizations exposed.
- Texas (45% at enforcement): Texas comes in second with 45 domains at p=reject. The state is the energy capital of the United States, home to the largest concentration of oil and gas companies in the world, a massive healthcare system, military installations including Fort Cavazos and Joint Base San Antonio, and a fast-growing technology sector in Austin and Dallas. Only 3 domains lack a DMARC record, the lowest N/A rate in the study. But 34 domains run p=none, collecting reports without acting on them.
- Kansas (42% at enforcement): Kansas has 42 domains at p=reject and the second-highest quarantine count in the study at 25. The state is central to the country's agriculture and food production supply chain, and is home to major aviation manufacturing in Wichita alongside a significant military presence at Fort Riley and McConnell Air Force Base. 28 domains run p=none and only 5 lack a record. Those 25 domains at quarantine have done most of the work already. The final step to reject is a short project.
- Missouri (40% at enforcement): Missouri has 40 domains at p=reject. St. Louis and Kansas City anchor a financial services, healthcare, and logistics sector that connects the eastern and western halves of the country. 34 domains run p=none, the joint-highest none count in the study, and 6 have no record. 40% enforcement isn't bad in isolation, but the 34 domains sitting at p=none are the concern. They've published a DMARC record. The data is flowing in. Nobody's acting on it.
- Oklahoma (37% at enforcement): Oklahoma has 37 domains at p=reject. The state's economy runs on energy, with a concentration of oil and gas companies, pipeline operators, and energy services firms alongside a growing aerospace sector. 34 domains run p=none, 23 sit at p=quarantine, and 6 have no record. Wire transfer instructions, drilling contracts, and joint venture agreements all move by email in this state. A spoofed domain targeting those workflows can redirect six-figure payments before anyone catches it.
- Colorado (33% at enforcement): Colorado has 33 domains at p=reject. The state is home to NORAD, U.S. Space Command, the U.S. Air Force Academy, and a dense cluster of defense contractors along the Front Range. Colorado also has a growing technology sector and a significant natural resources industry. 39 domains run p=none, the highest none count in the study, and 7 have no record. A state that hosts the command center responsible for North American aerospace defense should not have two-thirds of its top organizations failing to block spoofed email.
- Louisiana (32% at enforcement): Louisiana has 32 domains at p=reject and the second-highest quarantine count at 30. The state runs one of the largest petrochemical corridors in the world along the Gulf Coast, operates the Port of South Louisiana (the largest tonnage port in the Western Hemisphere), and has a major healthcare and higher education sector. 23 domains run p=none and 15 have no record. Those 30 domains at quarantine are the standout here. They've identified their senders, configured SPF and DKIM, and set a quarantine policy. The step from quarantine to reject is measured in weeks.
- Arkansas (28% at enforcement): Arkansas has 28 domains at p=reject and the third-highest N/A rate in the study at 13. The state is home to Walmart's headquarters and a major retail and logistics corridor, alongside poultry and agriculture industries that rank among the largest in the country. 37 domains run p=none and 22 sit at p=quarantine. 28% enforcement puts Arkansas among the lowest-performing states in any region Red Sift has studied.
- New Mexico (25% at enforcement): New Mexico sits at the bottom with 25 domains at p=reject, the lowest enforcement rate in the Heartland and the second-lowest single-state rate Red Sift has recorded after Hawaii (29% in the Southwest study). The state is home to Sandia National Laboratories and Los Alamos National Laboratory, two of the most important nuclear and defense research facilities in the world, alongside Kirtland Air Force Base and White Sands Missile Range. 34 domains run p=none and 20 have no DMARC record at all, the highest N/A rate in the study. The gap between New Mexico's national security significance and its email authentication posture is hard to justify.
Assess your domain today
Use our free Red Sift Investigate tool to check your DMARC, SPF, and DKIM configuration.
Regional comparison
State | Reject | Quarantine | None | No record |
Nebraska | 46% | 22% | 24% | 8% |
Texas | 45% | 18% | 34% | 3% |
Kansas | 42% | 25% | 28% | 5% |
Missouri | 40% | 20% | 34% | 6% |
Oklahoma | 37% | 23% | 34% | 6% |
Colorado | 33% | 21% | 39% | 7% |
Louisiana | 32% | 30% | 23% | 15% |
Arkansas | 28% | 22% | 37% | 13% |
New Mexico | 25% | 21% | 34% | 20% |
Regional total | 328 (36%) | 202 (22.4%) | 287 (31.9%) | 83 (9.2%) |
Northeast* | 35% | 22.6% | 30.9% | 11.6% |
Mid-Atlantic* | 44% | 19.4% | 27.3% | 9.1% |
Southwest* | 40% | 22.8% | 27.6% | 9.4% |
New York* | 73% | 15% | 12% | 1% |
Regional comparison
The 202 organizations sitting at p=quarantine are close. They've done the DNS work, identified their senders, and configured SPF and DKIM. Moving from quarantine to reject typically takes 6 to 8 weeks. That's 202 domains where a short project finishes a job that's mostly complete.
Why DMARC is essential for the Heartland in 2026
The Heartland runs on industries where a spoofed email can trigger wire fraud, compromise classified research, disrupt energy supply chains, or contaminate food safety communications. The region's spread across nine states and multiple critical sectors makes the risk diffuse but no less severe.
The energy sector is the country's biggest email fraud target
Texas, Oklahoma, Louisiana, Colorado, and New Mexico produce the majority of the country's oil, gas, and renewable energy. Wire transfer instructions, drilling contracts, pipeline right-of-way agreements, and joint venture payments all travel by email. The FBI's IC3 logged $3.04 billion in BEC losses in 2025, with 86% of those funds moving via wire transfer or ACH. Energy companies are high-value targets because their payment workflows involve large sums, multiple counterparties, and time-sensitive approvals. A spoofed email from an operator to a midstream company, or from an EPC contractor to a project owner, can move seven-figure sums before anyone flags it. DMARC enforcement at p=reject stops the impersonation before it reaches the inbox.
Agriculture and food supply chains connect every state in the region
Kansas, Nebraska, Missouri, and Arkansas sit at the center of the country's agricultural production. These states handle grain trading, livestock processing, food distribution, and the vendor payment networks that connect farmers, processors, distributors, and retailers. Supply chain communications, including purchase orders, phytosanitary certificates, delivery confirmations, and payment instructions, move by email. A spoofed domain targeting a grain elevator, a meatpacking plant, or a food distributor can redirect payments, delay shipments, or introduce fraudulent instructions into a supply chain that feeds millions of people. The 31.9% of Heartland domains sitting at p=none are watching this happen in their DMARC reports without blocking any of it.
National laboratories and defense installations demand better
New Mexico hosts Sandia National Laboratories and Los Alamos National Laboratory, two facilities responsible for nuclear weapons stewardship, advanced defense research, and national security programs. Colorado hosts NORAD, U.S. Space Command, and the U.S. Air Force Academy. Texas has one of the highest concentrations of military installations in the country. Defense contractors, research partners, and government agencies operating in these states send email tied to classified programs, procurement, and intelligence operations. New Mexico's 25% enforcement rate and 20% N/A rate are the lowest in the study, and they belong to a state where a spoofed domain targeting the defense supply chain isn't a phishing attempt. It's a national security risk.
Mailbox providers are now rejecting unauthenticated email
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025 with its own enforcement for high-volume senders to Outlook, Hotmail, and Live.com addresses. Non-compliant messages are now rejected outright. For Heartland organizations sending energy contracts, agricultural invoices, insurance claims, or defense correspondence, a missing or weak DMARC policy means those messages may never arrive. The 83 domains with no DMARC record at all are the most exposed, but the 287 at p=none are also at risk as enforcement tightens across all major mailbox providers.
Compliance pressure spans every major Heartland industry
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data, hitting retail, financial services, and energy companies across the region. NIS2 applies to any Heartland firm with EU operations or clients. NERC CIP standards govern cybersecurity for bulk power system operators, and email authentication is increasingly part of that compliance picture for utilities in Texas, Oklahoma, and Colorado. Cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For defense contractors in New Mexico and Colorado, CMMC and NIST frameworks already recommend DMARC as a baseline control.
Why choose Red Sift OnDMARC
Heartland organizations face a mix of pressures: energy sector fraud targeting, agricultural supply chain complexity, defense and research facility security, and rapid growth across the region's expanding metro areas. Red Sift OnDMARC is built for that complexity.
- Enforcement in 6 to 8 weeks: Manual DMARC projects average around 32 weeks. OnDMARC cuts that to 6 to 8 weeks by automating source identification, SPF and DKIM configuration, and enforcement readiness checks. For the 202 Heartland organizations sitting at p=quarantine, the final step to reject could be measured in weeks, not months.
- Dynamic SPF for complex sender lists: Heartland organizations tend to have long lists of authorized email senders: energy trading platforms, agricultural commodity systems, insurance claims processors, logistics tools, marketing platforms, and more. SPF records have a hard limit of 10 DNS lookups, and complex organizations blow past that quickly. Red Sift's Dynamic SPF manages this automatically, keeping authentication valid without manual record management.
- Clear reporting across every domain: OnDMARC converts raw DMARC aggregate and forensic reports into a dashboard that shows every service sending email on behalf of your domains. Security and compliance teams get immediate visibility into what's authorized, what's failing authentication, and what needs fixing. No XML parsing. No guesswork.
- Continuous monitoring for regulated industries: Energy, financial services, defense, and agriculture organizations all face ongoing audit and compliance requirements. OnDMARC provides continuous monitoring and alerting, so enforcement holds even as new senders are added, domains change hands, or infrastructure evolves through mergers and acquisitions.
36% enforcement across the Heartland puts the region behind the Southwest (40%) and Mid-Atlantic (44%), and barely ahead of the Northeast (35%). Nebraska's 46% shows the path works. New Mexico's 25% shows how far some states still need to go. For the 572 organizations that haven't reached full enforcement, Red Sift OnDMARC can close the gap between the region's risk exposure and its current email security posture.
Get a short overview of Red Sift OnDMARC
Jack leads content, PR, GEO, and email security research at Red Sift.






