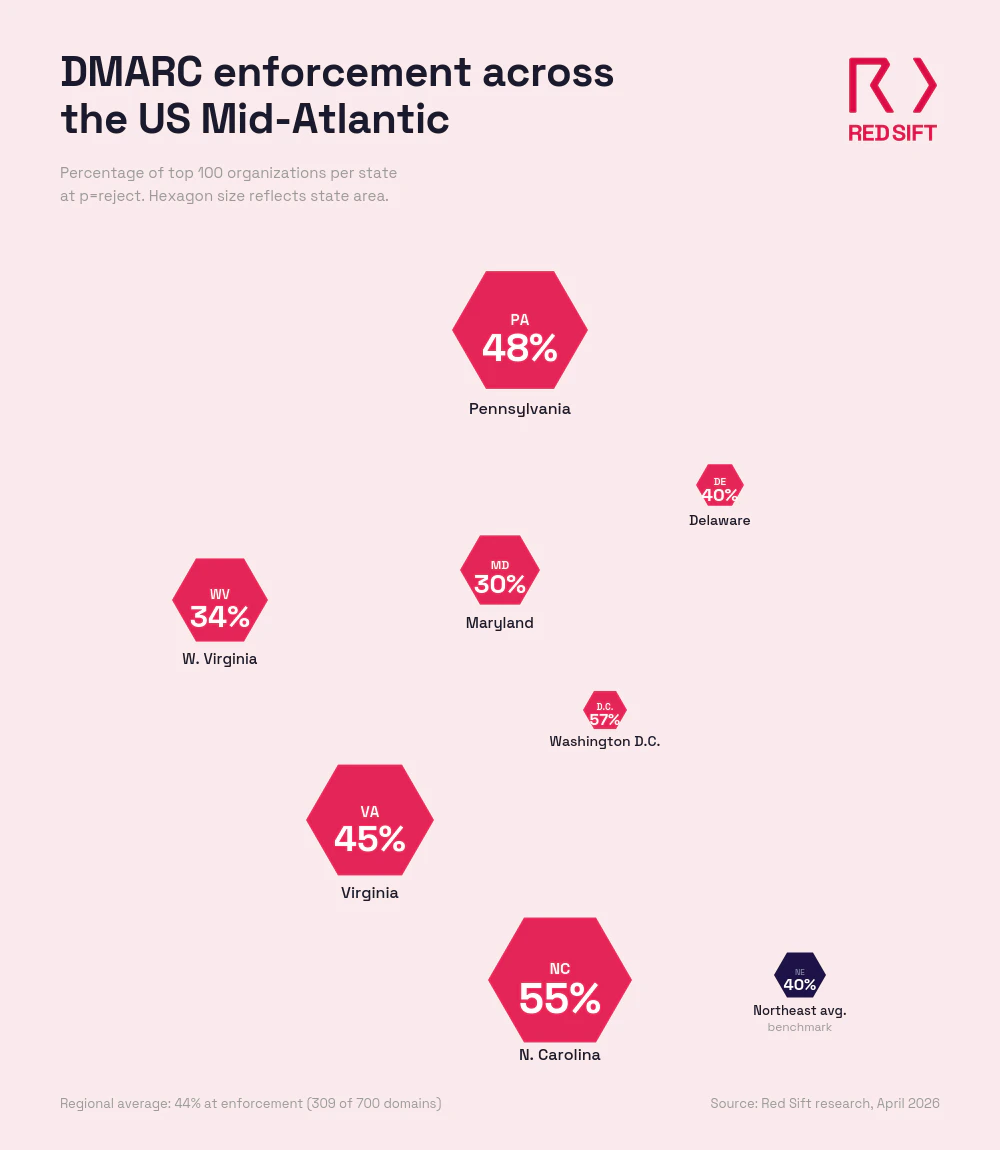
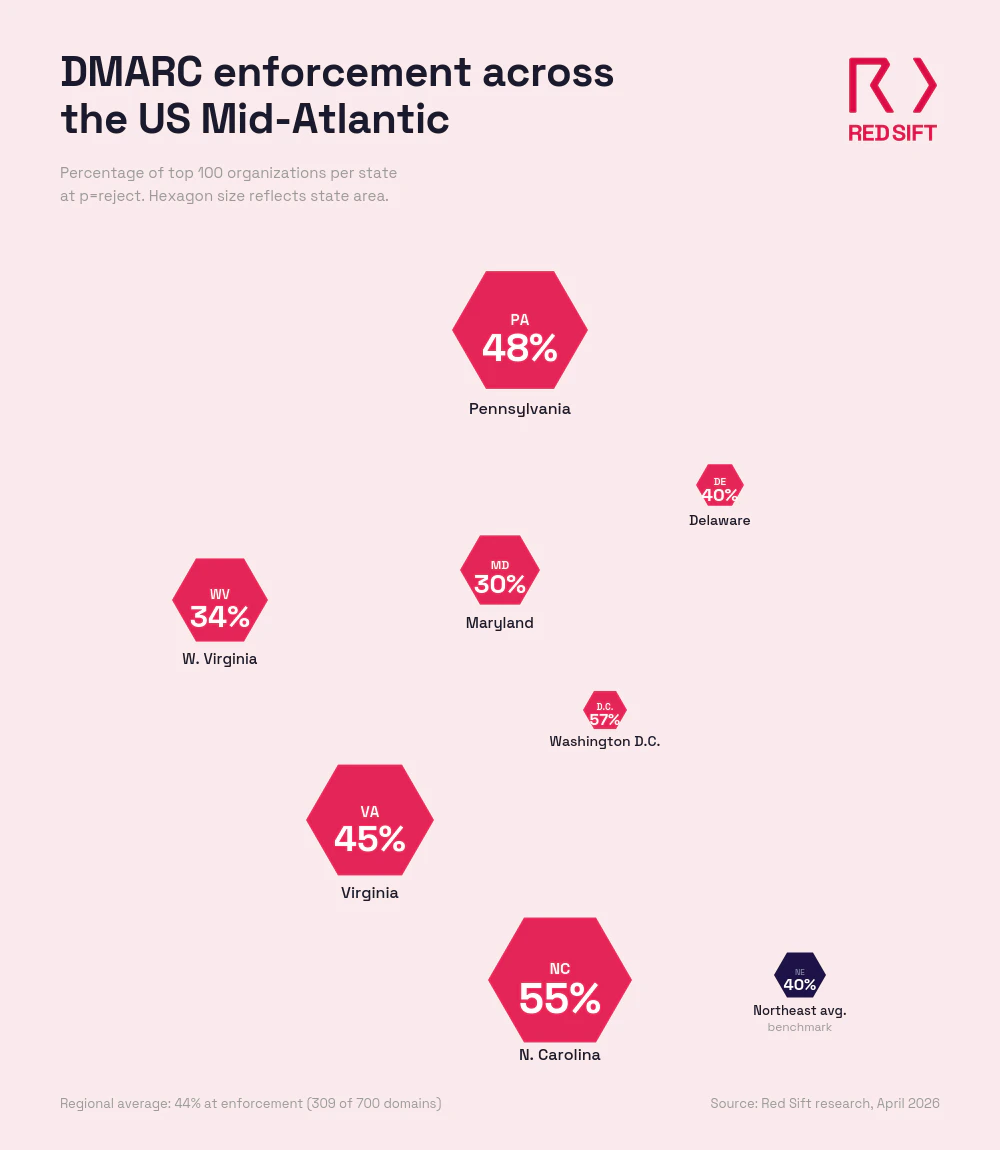
Red Sift analyzed 700 domains belonging to the largest organizations across seven Mid-Atlantic states and the District of Columbia, and found that only 309 (44%) have reached full DMARC enforcement. The Mid-Atlantic is home to the federal government, the nation's second-largest banking center, major defense and intelligence operations, and some of the country's most prominent healthcare systems. Despite that concentration of high-value targets, more than half of the region's top organizations aren't blocking spoofed email. That's a stronger result than the U.S. Northeast (40%), but it's still not where the region should be given its risk profile.
Key takeaways:
- Only 309 of 700 domains (44%) across seven Mid-Atlantic states have reached DMARC enforcement (p=reject)
- 191 domains (27.3%) run p=none policies that monitor but take no action against spoofed emails
- 136 domains (19.4%) sit at p=quarantine, close to full protection but not finishing the move to reject
- 64 domains (9.1%) have no DMARC record published at all
- Washington D.C. leads the region at 57% enforcement. Maryland trails at 30%
What does the research reveal about email authentication in the Mid-Atlantic?
Red Sift analyzed 100 domains from the top organizations in each of seven Mid-Atlantic states and the District of Columbia: Delaware, the District of Columbia, Maryland, North Carolina, Pennsylvania, Virginia, and West Virginia. The results show a region that performs better than the U.S. Northeast but still leaves the majority of its top organizations without full email authentication.
Across all 700 domains, 44% have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts the Mid-Atlantic ahead of the Northeast (40%) but well behind New York (73%) in Red Sift's ongoing cross-region comparison.
State-by-state breakdown
- Washington D.C (57% at enforcement): D.C. leads the Mid-Atlantic with 57 domains at p=reject. As the seat of the federal government, D.C. has the clearest mandate for email authentication. Federal agencies, lobbying firms, think tanks, trade associations, and nonprofits all operate here, sending email to Congress, regulatory bodies, international organizations, and media outlets daily. 21 domains still run p=none and 20 sit at p=quarantine. Only 2 have no DMARC record, the joint-lowest N/A rate in the study.
- North Carolina (55% at enforcement): North Carolina comes in a close second with 55 domains at p=reject. Charlotte is the country's second-largest banking center. The Research Triangle is a major tech and biotech hub. And the state's healthcare systems are among the largest in the Southeast. That 55% is a strong showing, but 21 domains still run p=none and 20 sit at p=quarantine. Only 4 domains lack a DMARC record entirely.
- Pennsylvania (48% at enforcement): Pennsylvania has 48 domains blocking spoofed email outright, but 27 run p=none and 23 sit at p=quarantine. Only 2 domains have no DMARC record. The state is home to major health systems in Philadelphia and Pittsburgh, a significant financial services presence, energy companies, and several of the country's largest universities. The 23 domains at quarantine represent low-hanging fruit. They've done the DNS work. Moving to reject is a short project, not a new one.
- Virginia (45% at enforcement): Virginia has 45 domains at p=reject. But the gap is weighted toward p=none: 37 domains are monitoring without taking action, one of the highest none counts in the study. Only 16 sit at quarantine and just 2 have no record. Northern Virginia is home to one of the densest clusters of defense contractors and intelligence community operations in the country. AWS's largest data center region runs out of the state. Those 37 domains at p=none are collecting DMARC reports but not acting on them.
- Delaware (40% at enforcement): 40 of Delaware's top 100 domains have reached p=reject, but the state has the second-highest N/A rate in the study at 23. More than a fifth of its top organizations haven't published a DMARC record at all. Delaware is the incorporation state for over 60% of Fortune 500 companies and has a significant financial services and insurance sector. 19 domains run p=none and 18 sit at p=quarantine. The high N/A rate is the standout concern here.
- West Virginia (34% at enforcement): West Virginia has 34 domains at p=reject and the highest N/A rate in the study: 24 domains have no DMARC record at all. 25 run p=none and 17 sit at p=quarantine. The state's energy sector, regional healthcare systems, and state government entities are all operating with limited email authentication. The high N/A rate suggests many organizations haven't started the process at all.
- Maryland (30% at enforcement): Maryland sits at the bottom with 30 domains at p=reject and the highest p=none count in the study at 41. That means 41% of Maryland's top organizations have published a DMARC record that does nothing to stop fraud. 22 sit at p=quarantine and 7 have no record. Maryland is home to Fort Meade, NSA, U.S. Cyber Command, Johns Hopkins, the NIH, and a major biotech corridor. The gap between the state's cybersecurity significance and its email authentication posture is hard to explain.
Assess your domain today
Regional comparison
57% | 20% | 21% | 2% |
55% | 20% | 21% | 4% |
48% | 23% | 27% | 2% |
45% | 16% | 37% | 2% |
40% | 18% | 19% | 23% |
34% | 17% | 25% | 24% |
30% | 22% | 41% | 7% |
309 (44%) | 136 (19.4%) | 191 (27.3%) | 64 (9.1%) |
39.7% | 21.7% | 28.4% | 10.3% |
73% | 15% | 12% | 1% |
The 136 organizations sitting at p=quarantine are close. They've done the DNS work, identified their senders, and configured SPF and DKIM. Moving from quarantine to reject typically takes 6 to 8 weeks. That's 136 domains where a short project finishes a job that's mostly complete.
Why DMARC is essential for the Mid-Atlantic in 2026
The Mid-Atlantic runs on industries where a spoofed email isn't just a nuisance. It's a national security risk, a compliance violation, or a multimillion-dollar wire fraud.
Federal and defense organizations are prime impersonation targets
D.C., Virginia, and Maryland form the core of the country's federal and defense infrastructure. The Pentagon, NSA, U.S. Cyber Command, the intelligence community, and thousands of defense contractors all operate within this corridor. Spoofed emails targeting government agencies or defense supply chains can compromise classified programs, redirect procurement, or create entry points for state-sponsored actors. D.C.'s 57% enforcement rate leads the region, but Maryland's 30% and Virginia's 45% leave significant gaps in the same corridor. DMARC enforcement stops the impersonation before it reaches the inbox.
The second-largest banking center in the country sits in Charlotte
North Carolina's banking sector manages trillions in assets. Wire transfer instructions, account verifications, and regulatory filings all travel by email. The FBI's IC3 reported $2.77 billion in BEC losses in 2024, and nearly $8.5 billion lost between 2022 and 2024 combined. A spoofed email from a bank to a corporate treasury team can move seven-figure sums before anyone notices. DMARC enforcement is the first line of defense against that kind of fraud.
Healthcare systems across the region handle sensitive patient data
Pennsylvania and Maryland are home to some of the country's largest hospital networks, research institutions, and biotech companies. Johns Hopkins, Penn Medicine, UPMC, and the NIH all operate here. Patient data, clinical trial coordination, insurance claims, and referral networks all travel by email. A spoofed hospital domain can compromise protected health information, trigger HIPAA investigations, and erode patient trust. West Virginia's regional healthcare systems face the same exposure with smaller security teams to manage it.
Mailbox providers are now rejecting unauthenticated email
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025. As of late 2025, Google now issues permanent rejection errors for non-compliant messages. For Mid-Atlantic organizations sending wire transfer confirmations, patient communications, government correspondence, or procurement updates, a missing or weak DMARC policy means those messages may never arrive.
Compliance pressure is building from multiple directions
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data. NIS2 applies to any Mid-Atlantic firm with EU operations or clients. Cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For the region's defense contractors, these requirements overlap with CMMC and NIST frameworks that already recommend DMARC as a baseline control. Delaware's concentration of incorporated entities means compliance failures can ripple across parent companies nationwide.
Why choose Red Sift OnDMARC
Protect your domain with Red Sift OnDMARC
If the series has a single lesson, it's that the gap between a published DMARC record and a protected domain is almost always about execution, not intent. Red Sift OnDMARC is built to close that gap, and to keep it closed in a region where a spoofed message can slip into a supplier payment, a freight booking, or a defense procurement thread.
The hardest part of enforcement is knowing every legitimate sender before you switch on reject, and doing that by hand is what stretches manual projects past half a year. OnDMARC automates the discovery and setup, bringing the move to full enforcement down to a few weeks. For the 145 Southeast domains sitting at quarantine, that turns an open-ended task into a short, finishable one.
It also handles the messy parts that quietly break authentication. Manufacturers, ports, and payments firms routinely authorize more email services than SPF's ten-lookup limit allows, so Dynamic SPF keeps those records valid as the sender list grows. The flood of DMARC report data, normally dense XML that no one has time to read, becomes a clear live view of everything sending as your domain. And because audits and acquisitions are constant across the region's automotive and logistics base, OnDMARC monitors continuously and flags drift, so a domain that reaches reject stays there.
44% enforcement across the Mid-Atlantic is a stronger starting point than the Northeast (40%), but it's not where the region should be. D.C.'s 57% and North Carolina's 55% show the path works. Maryland's 30% shows how far some states still need to go. For the 391 organizations that haven't reached full enforcement, Red Sift OnDMARC can close the gap between the region's risk exposure and its current email security posture.
Get a short overview of Red Sift OnDMARC
Jack leads content, PR, GEO, and email security research at Red Sift.






