Guida Red Sift alla configurazione dei protocolli email

- Learn more about DKIM
- Why is DKIM key rotation important?
- How often should DKIM keys be rotated?
- What’s a long DKIM Key?
- What is DKIM canonicalization?
- What is a DKIM selector?
- What is the l= tag in DKIM?
- What are the security concerns around using the l= tag in DKIM?
- What is DKIM Header oversigning?
- What is a DKIM replay attack?
- How does DKIM help with forwarded mail?
- Can an email contain more than one DKIM signature i.e. be DKIM signed multiple times?
- How does ARC come into play when DKIM or DMARC fail?
- Common DKIM misconfigurations
- DKIM recommendations summary
- Technical DKIM configuration tips
- Generating 2048 bits DKIM public and private keys using OpenSSL on a Mac
- Learn more about DKIM
- Why is DKIM key rotation important?
- How often should DKIM keys be rotated?
- What’s a long DKIM Key?
- What is DKIM canonicalization?
- What is a DKIM selector?
- What is the l= tag in DKIM?
- What are the security concerns around using the l= tag in DKIM?
- What is DKIM Header oversigning?
- What is a DKIM replay attack?
- How does DKIM help with forwarded mail?
- Can an email contain more than one DKIM signature i.e. be DKIM signed multiple times?
- How does ARC come into play when DKIM or DMARC fail?
- Common DKIM misconfigurations
- DKIM recommendations summary
- Technical DKIM configuration tips
- Generating 2048 bits DKIM public and private keys using OpenSSL on a Mac
Learn more about DKIM
Why is DKIM key rotation important?
You can rotate DKIM keys by simply replacing the old pair with a new one to authenticate DKIM emails. If a threat actor steals or deciphers your private key, they won’t be able to use it for long if you practice regular DKIM key rotation.
In addition, regularly updating your DKIM keys increases your domain’s email deliverability rate.
How often should DKIM keys be rotated?
It’s generally suggested to rotate DKIM keys every 6 to 12 months. Frequent rotation stops hackers from intercepting and decoding your cryptographic keys. Less frequent rotation (say, once every couple of years) makes your domain more susceptible to the risk of intercepted or decoded keys.
What’s a long DKIM Key?
Some DNS editors can receive errors when DKIM keys or other TXT entries are longer than 255 characters.
To resolve this issue, you can enter your DKIM key by breaking it up into pieces on a single TXT entry.
For example, if your DKIM key is:
"v=DKIM1; k=rsa; p=abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabc"
You can enter it as:
"v=DKIM1; k=rsa; p=abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyz" "abcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabcdefghijklmnopqrstuvwxyzabc"
You can divide them at arbitrary places. The double quote enclosed parts should be separated by a single space character, not a new line.
What is DKIM canonicalization?
Canonicalization is a process whereby the headers and body of an email are converted to a canonical standard form before being DKIM signed. This can be thought of as converting data into a standard canonical form.
Some mail systems, such as forwarders, modify emails in transit that can potentially invalidate the DKIM signature applied. While some DKIM signers may accept minor mail modifications, others may be more strict and require stricter canonicalization.
Two canonicalization algorithms have been created to satisfy mild modification to a message and almost no modification to a message before signing. The two canonicalization algorithms are relaxed and simple respectively.
From DKIM’s perspective, the headers and body of an email are separate and canonicalization algorithms are specified for both, one for the headers and another for the body.
They are represented in the format of canonicalization/canonicalization for the header and body respectively. If no canonicalization is specified then simple is used for both headers and body, so it would look like this: simple/simple.
The simple/simple canonicalization is the stricter of the two and allows for almost no modification to the message header and body. However, this can affect the DKIM signature being invalidated by some forwarders as the email passes through them. Many of the issues with DKIM being invalidated during forwarding can be solved if the canonicalization is changed to relaxed/relaxed to allow for mild modifications to the emails.
What is a DKIM selector?
A DKIM selector is a string that points to a specific DKIM public key record in your DNS. It is specified as s= tag in the DKIM-Signature header field and can be found in the technical headers of an email.
Validation on the receiver side uses the selector in combination with the signing domain in order to carry out a DNS query and find the public key in your DNS.
For example:
“selector”._domainkey.yourdomain
When the receiver retrieves the public key it uses it to verify the DKIM signature.
No two services should use the same selector. For example, if you are sending emails from a number of services on behalf of your domain such as Google, Mailchimp, Salesforce, and Sendgrid, each one must use a unique key and selector in your DNS. If the selectors were the same the recipient would not be able to tell which key to use to decipher a particular email.
What is the l= tag in DKIM?
The l= tag in DKIM specifies the length of the message body that should be included in the DKIM hashing and signing process. This means that only the specified portion of the message body is signed, while the remainder is not included in the cryptographic signature.
This tag is optional. If it is not used, the entire message body is included in the signature by default.
What are the security concerns around using the l= tag in DKIM?
When the l= tag is used in DKIM, only a specified portion of the message body is included in the cryptographic signature, leaving the rest unsigned. This creates a security risk, as attackers can modify the unsigned portion of the message without invalidating the DKIM signature.
This vulnerability means that an attacker could intercept a legitimate email from a reputable sender, append malicious content to the unsigned part of the message, and resend it to a recipient who trusts the sender. Such an attack could damage the reputation of the sending domain and potentially deceive recipients.
To mitigate this risk, it is recommended not to use the l= tag in your DKIM signing process. Additionally, audit your vendors to ensure they are not including this tag when sending emails on your behalf.
What is DKIM Header oversigning?
DKIM is used to sign specific headers or parts of the email body, such as the "From," "Subject," and other headers, to verify the identity of the sender and ensure the integrity of the message. If a signed header is modified after being sent, the DKIM verification will fail.
Attackers may attempt to inject additional headers into an email or modify existing ones for malicious purposes. Oversigning common headers, such as "From," "Subject," "Reply-To," etc., can help protect your emails from manipulation and replay attacks. Oversigning means that you include multiple instances of the same header, effectively signing each one to prevent tampering.
By sending a test email to Red Sift’s Investigate tool, you will be able to see what headers are DKIM signed in your email and if you are oversigning.
What is a DKIM replay attack?
A DKIM replay attack is a type of email attack in which an attacker takes a legitimate, DKIM-signed email and resends it to multiple recipients. The attacker exploits the DKIM signature, which verifies the email's authenticity and integrity, to benefit from the original sender's reputation. This increases the likelihood that the replayed email will bypass spam filters and land in the recipients' inboxes, as it appears to come from a trusted source.
How does DKIM help with forwarded mail?
DKIM helps with forwarded mail by providing a mechanism to verify the authenticity and integrity of an email, even after it has been forwarded. Forwarding can often alter email headers, which can cause issues with other email authentication methods like SPF (Sender Policy Framework).
Without DKIM, forwarded emails may fail to reach the recipient's inbox, especially if the sender's domain is protected by a strict DMARC (Domain-based Message Authentication, Reporting, and Conformance) policy. This is because SPF authentication often fails during forwarding, and without both SPF and DKIM, a DMARC policy of p=reject will instruct the recipient's server to reject the email.
It is strongly advised not to set a DMARC policy of "reject" without first implementing an aligned DKIM signature for all your email sending systems. This ensures that at least one authentication mechanism remains intact when SPF fails.
However, it's important to note that DKIM can also fail when an email is forwarded, particularly if the forwarder modifies any of the DKIM-signed headers or the body of the email. This can happen due to email security gateways, external disclaimer banners, or other modifications introduced during the forwarding process.
Can an email contain more than one DKIM signature i.e. be DKIM signed multiple times?
Yes, an email can contain multiple DKIM signatures, and this is quite normal. This typically occurs when an email passes through different systems that each apply their own DKIM signature. For example, an email service provider (ESP) might add a DKIM signature to track reputation feedback, and another DKIM signature might be added when the email is sent from one system to another on its way out to the internet. If both systems are configured to DKIM sign emails, the email will end up with multiple DKIM signatures.
It's important to note that one of the signatures may fail (often the first one, if the email is modified between the initial and subsequent signing), but as long as at least one signature passes verification, the DKIM check will be considered successful.
How does ARC come into play when DKIM or DMARC fail?
As mentioned earlier, DKIM may fail when an email is forwarded. ARC (Authenticated Received Chain) addresses the limitations of DKIM and DMARC in scenarios involving email forwarding and mailing lists by preserving the original authentication results through a sequence of cryptographic signatures, creating a chain of custody.
ARC helps ensure that legitimate emails can be trusted and delivered, even if modifications by intermediaries cause DKIM or DMARC failures. It does this by allowing the forwarding server to attest to the original authentication results and the integrity of the message when it was first received.
However, the use of ARC relies on the email forwarder to implement it, establishing this chain of custody. Even if an email passes ARC, it does not necessarily guarantee that the email will be trusted or delivered to the recipient's inbox. The final decision lies with the receiving system, which determines whether to trust the established chain of custody.
Common DKIM misconfigurations
- Using Weak or Deprecated Cryptographic Algorithms: Avoid using DKIM keys that are less than 1024 bits. A 2048-bit key is recommended for stronger security. Additionally, ensure you use up-to-date cryptographic algorithms, such as
rsa-sha256. - Not Splitting Longer Keys Correctly in DNS: When publishing a 2048-bit key in DNS, it may be necessary to split the key into multiple DNS records if your DNS host does not automatically handle this. Failure to do so can result in DKIM verification failures. Refer to the specific guidance or examples provided for splitting keys correctly.
- Enabling DKIM in a Third-Party System Without Publishing the Corresponding Public Key: DKIM relies on a private/public key pair. The sender (e.g., a third-party vendor) holds the private key, which is used to sign outgoing emails. It is crucial to publish the corresponding public key in your domain's DNS records, provided by the vendor, to enable proper DKIM verification.
- Missing Required Tags in a DKIM Record: Ensure that your DKIM record begins with
v=DKIM1;. This is a required tag that identifies the record as a DKIM record. - Using the Wrong Record Type: Make sure to publish your DKIM record using the correct DNS record type, such as TXT or CNAME, as specified by the third-party sender. Some providers may require a TXT record for DKIM, while others might use CNAME. Additionally, some vendors, like Microsoft 365 or Amazon SES, may provide multiple DKIM records to facilitate easy key rotation and management.


DKIM recommendations summary
- Oversign email headers.
- Rotate DKIM keys at least once a year.
- Use strong keys (at least 1024-bit) and up-to-date algorithms.
- Avoid using the l= tag.
- Remove unused DKIM records from DNS.
- Implement DMARC with DKIM for better insight and protection.
Technical DKIM configuration tips
Generating 2048 bits DKIM public and private keys using OpenSSL on a Mac
Learn how to generate 2048 bits DKIM public and private keys using the Mac terminal and create a DNS record.
How to generate the private and public keys
- Open the terminal and type
openssl - To generate a private key type:
openssl genrsa -out private.key 2048 - To generate a public key from the private key type:
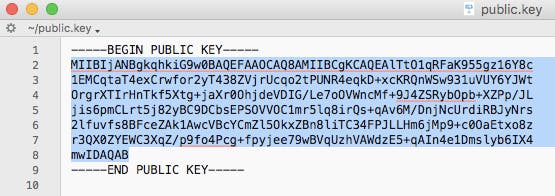
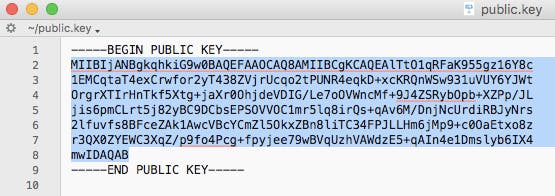
openssl rsa -in private.key -pubout -out public.key - Find the folder that contains your public key and open it. It should look something like the image below.
- Manually convert the highlighted text above to a single line ie. remove the spaces between new lines.
How to create the DNS record
The generated 2048-bit DKIM public key is too long to fit into a single TXT DNS record. A DNS record can be up to 255 characters. Therefore your public key will need to be split into two separate TXT records using quotes and slash or brackets and quotes as shown below.
Note: this depends on your DNS provider.
TXT"part one" \ "part two"TXT( "part one" "part two" )
To create the DNS record you will have to specify the Name, Type, and Value of the DNS record.
The DNS record Name will look like this:
selector._domainkey.domain
Where the selector is defined by you and can be called anything, for example, the date, device, or service that will sign the emails.
For example:
20180719._domainkey.redsift.io
The DNS record Type is TXT.
The DNS record Value should look like the examples below. The part in bold is copied from the generated public key file and remember that you will need to split the public key into two records.
Splitting examples
Example 1 using quotes
TXT record 1:
“v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAlTtO1qRFaK955gz16Y8c1EMCqtaT4exCrwfor2yT438ZVjrUcqo2tPUNR4eqkD+xcKRQnWSw931uVUY6YJWtOrgrXTIrHnTkf5Xtg+jaXr0OhjdeVDIG/Le7oOVWncMf+9J4ZSRybOpb+XZPp/JLjis6pmC”
TXT record 2:
“Lrt5j82yBC9DCbsEPSOVVOC1mr5lq8irQs+qAv6M/DnjNcUrdiRBJyNrs2lfuvfs8BFceZAk1AwcVBcYCmZl5OkxZBn8liTC34FPJLLHm6jMp9+c0OaEtxo8zr3QX0ZYEWC3XqZ/p9fo4Pcg+fpyjee79wBVqUzhVAWdzE5+qAIn4e1Dmslyb6IX4mwIDAQAB”
Example 2 using brackets and quotes
TXT record 1:
(“v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAlTtO1qRFaK955gz16Y8c1EMCqtaT4exCrwfor2yT438ZVjrUcqo2tPUNR4eqkD+xcKRQnWSw931uVUY6YJWtOrgrXTIrHnTkf5Xtg+jaXr0OhjdeVDIG/Le7oOVWncMf+9J4ZSRybOpb+XZPp/JLjis6pmC”
TXT record 2:
“Lrt5j82yBC9DCbsEPSOVVOC1mr5lq8irQs+qAv6M/DnjNcUrdiRBJyNrs2lfuvfs8BFceZAk1AwcVBcYCmZl5OkxZBn8liTC34FPJLLHm6jMp9+c0OaEtxo8zr3QX0ZYEWC3XqZ/p9fo4Pcg+fpyjee79wBVqUzhVAWdzE5+qAIn4e1Dmslyb6IX4mwIDAQAB”)


Domande frequenti: Guida alla configurazione dei protocolli email
Prima di DMARC, nei record SPF era spesso usato il meccanismo “-all” per applicare restrizioni rigorose alle policy dei mittenti. Tuttavia, le attuali raccomandazioni del settore per il 2026 privilegiano “~all” per bilanciare sicurezza e deliverability ed evitare il rifiuto non necessario di email legittime che falliscono SPF, ma superano DKIM e DMARC.
Il motivo è che “~all” in combinazione con DMARC (in p=reject) consente comunque di non recapitare email non autenticate quando SPF e DKIM falliscono, senza bloccare email legittime – migliorando così la deliverability complessiva.
Le specifiche DMARC (RFC 7489) affermano che un prefisso “-” nel meccanismo SPF del mittente – come “-all” – può comportare il rifiuto di un’email già nella fase iniziale, cioè prima che venga applicato DMARC. Utilizza “-all” solo per domini inattivi che non inviano mai email. DMARC non distingue tra Soft Fail e Hard Fail su SPF: considera entrambi semplicemente come un errore SPF.
DMARC richiede non solo che SPF o DKIM abbiano esito positivo, ma anche che almeno uno dei domini usati con SPF o DKIM corrisponda al dominio presente nell'intestazione From. Un corretto allineamento è fondamentale nel 2026 per la consegna delle email, perché i principali provider ora richiedono questa verifica.
Per SPF, l’allineamento significa che la verifica di MAIL FROM/Return-PATH è andata a buon fine e la parte dominio di MAIL FROM/Return-PATH coincide con il dominio dell’indirizzo From. In modalità Strict le due devono essere identiche; in modalità Relaxed vengono accettate anche le sottodomini se appartengono alla stessa organizational domain.
Esempio: se MAIL-FROM/RETURN-PATH è @ondmarc.com e il From-header è @knowledge.ondmarc.com, non sono allineati in modalità Strict, ma DMARC li considererebbe validi in modalità Relaxed.
Un report aggregato DMARC contiene informazioni sullo stato di autenticazione dei messaggi inviati per conto di un dominio. Si tratta di un bounce report in XML che riepiloga quali email hanno superato o fallito SPF e DKIM. Permette ai possessori di dominio di avere una panoramica precisa delle fonti che inviano email a loro nome e cosa succede (policy del destinatario).
I destinatari usano il tag 'rua' del record DMARC per inviare i report. Puoi definire la frequenza usando il tag ri nel record DMARC (valore predefinito: 86400 secondi, ovvero 24h). I report forensi forniscono dettagli molto più precisi su ogni fallimento di autenticazione. I dati personali vengono rimossi, ma tutte le informazioni utili alla risoluzione dei problemi, come header SPF/DKIM e indirizzo mittente completo e oggetto, sono trasmesse.
L’indirizzo di ricezione dei report forensi DMARC si indica tramite il tag 'ruf'. Non tutti i sistemi supportano questi report. Red Sift OnDMARC è tra le poche soluzioni che può ricevere report forensi – grazie alla partnership con Yahoo.
Una macro SPF è un meccanismo nei record SPF che consente di definire insiemi riutilizzabili di indirizzi IP. Le macro SPF offrono maggiore flessibilità e mantenibilità: puoi definire set complessi di IP in un unico meccanismo e referenziarli in vari record. Ad esempio, invece di elencare ogni IP autorizzato, puoi usare una macro come “%{i}”, che richiama l’IP in uscita dell’email. In questo modo puoi gestire facilmente grandi elenchi IP senza superare il limite di lookup SPF e rendere meno evidenti le autorizzazioni IP durante le interrogazioni DNS.
A seconda della struttura della macro nel record SPF, una mancata espansione della macro può causare errori SPF o un risultato neutro (?all). Se l’invio di email legittime dipende dalle macro SPF, queste ultime possono portare a maggiori fallimenti o a segnalare come sospetto il traffico verso sistemi che si basano su SPF.
Mail Transfer Agent Strict Transport Security (MTA-STS) è uno standard per la cifratura dei messaggi tra due server di posta. Comunica ai server mittenti che le email devono essere recapitate solo tramite connessione sicura, tramite Transport Layer Security (TLS), proteggendo così dai tentativi di intercettazione da parte dei criminali informatici.
L’adozione di MTA-STS è cresciuta rapidamente e nel 2026 la sicurezza dei trasporti sarà considerata essenziale per la protezione della posta in transito. Per attivare MTA-STS su un dominio ricevente, occorre dichiarare il supporto tramite DNS e rendere disponibile un file di policy sul proprio sito.
MTA-STS va attivato con cautela per non causare blocchi accidentalmente. Si consiglia di iniziare con la modalità Test: in questo modo, grazie ai rapporti TLS, puoi identificare e risolvere eventuali errori prima di passare alla modalità strict. Questo approccio graduale sarà probabilmente lo standard per la protezione della posta in transito nel 2026.
SMTP TLS Reporting (TLS-RPT), secondo RFC8460, serve a segnalare problemi di connettività TLS dai server MTA mittenti. Proprio come per DMARC, anche qui vengono inviati report via email al titolare del dominio quando problemi TLS ostacolano la consegna. I report contengono le policy MTA-STS rilevate, statistiche di traffico, connessioni fallite e motivi di errore.
Con la funzione MTA-STS in Red Sift OnDMARC non dovrai preoccuparti delle complesse implementazioni. Basta aggiungere gli MTA-STS Smart Record forniti da OnDMARC al proprio DNS e Red Sift si occuperà dell’hosting del file di policy, la gestione del certificato SSL e l’invio automatico di segnalazioni di violazione via report TLS. Nel 2026, l’MTA-STS in hosting è sempre più uno standard previsto nelle moderne piattaforme DMARC, rendendo più semplice l’integrazione della cifratura nei trasporti.
Secondo RFC 7671, DANE (DNS-based Authentication of Named Entities) è un nuovo standard Internet per la creazione di comunicazioni TLS tra client e server senza dipendere dalle autorità di certificazione (CA) tradizionali.
Nel modello attuale, qualsiasi CA può rilasciare un certificato per qualunque dominio. DANE adotta un altro approccio, sfruttando l’infrastruttura DNSSEC (Domain Name System Security Extensions) per associare in modo crittografico un nome di dominio a un certificato. DANE si basa sul protocollo DNSSEC esistente per garantire autenticità e integrità della ricezione.
DANE introduce inoltre un nuovo tipo di record DNS, TLSA, che segnala al client il supporto server a TLS. È raccomandato implementare sia MTA-STS sia DANE. DANE è d’obbligo per molti enti pubblici, in particolare in UE.
MTA-STS e DANE sono efficaci solo se anche il server mittente li supporta – molti implementano solo uno dei due. Attivare entrambi aumenta la sicurezza generale. Nel 2026 le organizzazioni adottano spesso MTA-STS prima, per massima compatibilità, e aggiungono DANE per livelli di sicurezza superiori quando richiesto.
La policy per le sottodomini permette agli amministratori di proteggere in modo differenziato diversi domini e sottodomini a seconda dello stadio di implementazione di DMARC. Ad esempio, se tutti i servizi di invio associati al dominio principale sono già protetti da SPF e DKIM, puoi impostare una policy DMARC p=reject sul dominio principale e p=none sulle sottodomini – o viceversa.
Se un servizio di invio non supporta DMARC (cioè non implementa SPF o DKIM) puoi assegnargli una sottodominio separata con una policy DMARC propria, senza compromettere la protezione dei domini restanti. Ciò consente di distribuire il traffico tra diverse sottodomini e proteggerle separatamente secondo le esigenze.






