Guida Red Sift alla configurazione dei protocolli email

- DNS setup instructions by Email Service Provider
- TXT record creation guidance
- How to create TXT records for SPF & DMARC with Amazon Route 53
- How to create TXT records for SPF & DMARC with Azure DNS
- How to create an SPF record in DNS using Cloudflare
- How to create TXT records for SPF & DMARC with Fasthosts
- How to create TXT records for SPF & DMARC with Google Domains
- How to create TXT records for SPF & DMARC with Hover
- How to create TXT records for SPF & DMARC with Ionos (Formerly 1&1)
- How to create TXT records for SPF & DMARC with Namecheap
- How to create TXT records for SPF & DMARC with Network Solutions
- How to create TXT records for SPF & DMARC with 123Reg
- DNS setup instructions
- AppRiver SPF and DKIM set up
- Brevo (formerly Sendinblue) SPF and DKIM set up
- Google Workspace SPF and DKIM set up
- Hubspot SPF and DKIM set up
- Kajabi SPF and DKIM set up
- Klaviyo SPF and DKIM set up
- Mailerlite SPF and DKIM setup
- Mandrill SPF and DKIM setup
- Mimecast DKIM signing setup
- Microsoft Dynamics 365 SPF and DKIM set up
- Microsoft Office 365 SPF and DKIM set up
- I get a warning from Microsoft 365 when using Dynamic SPF
- Set up your DKIM for Office 365
- Namecheap Private Email SPF and DKIM set up
- Proofpoint Protection Server (PPS) SPF and DKIM setup
- Salesforce Marketing Cloud SPF and DKIM set up
- Shopify SPF and DKIM record set up
- Squarespace SPF and DKIM set up
- DNS setup instructions by Email Service Provider
- TXT record creation guidance
- How to create TXT records for SPF & DMARC with Amazon Route 53
- How to create TXT records for SPF & DMARC with Azure DNS
- How to create an SPF record in DNS using Cloudflare
- How to create TXT records for SPF & DMARC with Fasthosts
- How to create TXT records for SPF & DMARC with Google Domains
- How to create TXT records for SPF & DMARC with Hover
- How to create TXT records for SPF & DMARC with Ionos (Formerly 1&1)
- How to create TXT records for SPF & DMARC with Namecheap
- How to create TXT records for SPF & DMARC with Network Solutions
- How to create TXT records for SPF & DMARC with 123Reg
- DNS setup instructions
- AppRiver SPF and DKIM set up
- Brevo (formerly Sendinblue) SPF and DKIM set up
- Google Workspace SPF and DKIM set up
- Hubspot SPF and DKIM set up
- Kajabi SPF and DKIM set up
- Klaviyo SPF and DKIM set up
- Mailerlite SPF and DKIM setup
- Mandrill SPF and DKIM setup
- Mimecast DKIM signing setup
- Microsoft Dynamics 365 SPF and DKIM set up
- Microsoft Office 365 SPF and DKIM set up
- I get a warning from Microsoft 365 when using Dynamic SPF
- Set up your DKIM for Office 365
- Namecheap Private Email SPF and DKIM set up
- Proofpoint Protection Server (PPS) SPF and DKIM setup
- Salesforce Marketing Cloud SPF and DKIM set up
- Shopify SPF and DKIM record set up
- Squarespace SPF and DKIM set up
DNS setup instructions by Email Service Provider
In this chapter, we provide guidance on how to create TXT records, as well as specific DNS setup instructions for some of the most popular ESPs - from Mailbox Providers (MBPs) like Gmail and Microsoft to Shopify and Squarespace, through to CRMs such as Salesforce and Hubspot.
TXT record creation guidance
How to create TXT records for SPF & DMARC with Amazon Route 53
- Log in to your Route 53 Console.
- In the navigation pane, choose 'Hosted zones'.
- Choose the domain that you want to add a
TXTorCNAMErecord to. - Choose 'Create record'.
- For 'Routing policy, choose Simple routing, and then choose Next.
- Choose Define simple record.
- In the Define simple record pane, do the following:
- - For Record name, Enter the host name for the TXT record. For example, leave this blank for an SPF record, or enter the value
_dmarcfor a DMARC record. - - For Value/Route traffic to, paste the value you are setting as the destination of the Host or the text value of the TXT.
- - For Record type, choose
TXTorCNAMEas appropriate. - - For TTL (seconds), type
1800. - - Choose Define simple record.
- Allow up to 24 hours for propagation of the newly created record.
For more information on adding TXT records to your domain’s Route53 DNS server, click here.
How to create TXT records for SPF & DMARC with Azure DNS
- Sign in to the Azure portal with your Azure account.
- Create a DNS zone (If a DNS zone for the domain is already created, skip to step 3.)
- At upper left, select Create a resource, then Networking, and then DNS zone.
- On the Create DNS zone page, type or select the following values:
- Name: Type contoso.xyzcontoso.xyz for this quickstart example. The DNS zone name can be any value that is not already configured on the Azure DNS servers. A real-world value would be a domain that you bought from a domain name registrar.
- Resource group: Select Create new, enter MyResourceGroup, and select OK. The resource group name must be unique within the Azure subscription.
- Select Create.
- Create a DNS record
- In the Azure portal, under All resources, open the contoso.xyzcontoso.xyz DNS zone in the MyResourceGroup resource group. You can enter contoso.xyzcontoso.xyz in the Filter by name box to find it more easily.
- At the top of the DNS zone page, select + Record set.
- On the Add record set page, type or select the following values:
- Host: Enter the host name for the
TXTrecord. For example, enter @ for an SPF record, or enter the value_dmarcfor a DMARC record. - Type:
TXT - Value: The value you are setting as the destination of the Host.
- TTL: Determine how long the server should cache information.
- Click 'Save' to publish the newly created record.
For more information on creating DNS records using Azure DNS, click here
How to create an SPF record in DNS using Cloudflare
For this scenario, we will use G Suite as the sending service and our domain would be test.ondmarc.com. To authorize G Suite to send emails on behalf of our domain we need to create the following SPF record in DNS.
v=spf1 include:_spf.google.com ~all
How to create the SPF record
Now that we have the value for our SPF record that needs to be created let’s go ahead and add it to the DNS for test.ondmarc.com in Cloudflare.
1. Log in to Cloudflare.
2. Select the account under which your domain exists.
3. Select the domain (ondmarc.com) under which you would like to create the SPF record.
4. Click the DNS app from the row of apps.
5. You will be presented with the following UI. Create and fill in the fields as shown at the beginning of this article.
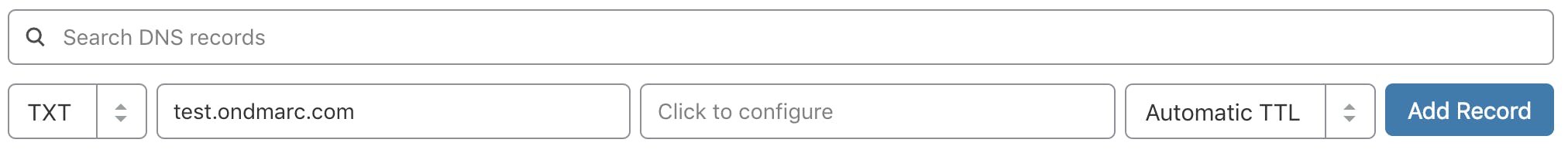
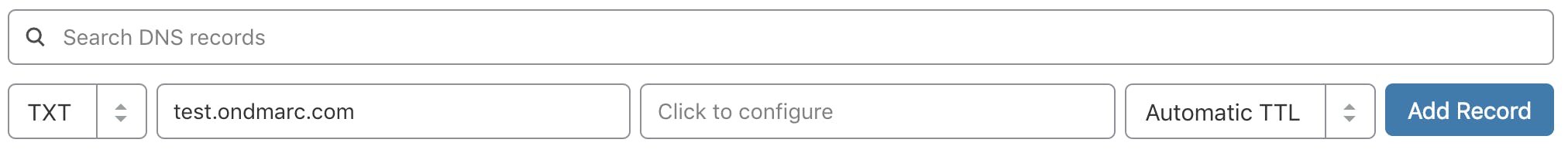
- The record type is
TXT - The name of the record in this case would be test.ondmarc.comtest.ondmarc.com.
- The value portion of the record above contains the following:
v=spf1 include:_spf.google.com ~all
We will leave the TTL set to Automatic and click Add Record.
Please allow some time for the record to propagate and be detected.
How to create TXT records for SPF & DMARC with Fasthosts
- Log into your FastHosts account.
- Under the Domain menu click Manage Domains.
- Select the domain name from the list that you wish to add the DNS records to.
- Click into the Configure Advanced DNS link.
- A list of DNS records will be shown.
- Scroll Down the list and click on the blue icon "ADD TXT RECORD"
- Fill out the fields with the following info: a) Hostname: Enter the host name for the TXT record. For example, enter @ for an SPF record, or enter the value _dmarc for a DMARC record. b) Destination TXT Value: The value you are setting as the destination of the Host.
- When the information are entered, click Save.
For more information on managing DNS in Fasthosts, click here.
How to create TXT records for SPF & DMARC with Google Domains
- Log in to your Google Domains account, select your 'Domain', and go to the 'DNS' section.
- Scroll down to the 'Custom resource records' and create the following record(s):
- SPF Record:
- Name: For the SPF record, enter the host name. Typically, you can use "@" to indicate the root domain.
- Type: Select
TXTas the record type. - Data: Enter the value for your SPF record. This value specifies which email servers are authorized to send emails on behalf of your domain.
- TTL: Determine the Time-to-Live for the record. This dictates how long DNS servers should cache the information.
- DMARC Record:
- Name: For the DMARC record, use the host name
_dmarc. - Type: Select
TXTas the record type. - Data: Set the value for your DMARC record. This value defines the DMARC policy and how email receivers should handle emails that fail authentication checks.
- TTL: Set the appropriate Time-to-Live value for the DMARC record.
- Click 'Add' to publish the new record.
How to create TXT records for SPF & DMARC with Hover
- Sign in to your Hover account.
- If you have multiple domain names, choose the domain name you want to edit.
- Select the 'DNS' tab.
- Select 'Add New' and enter the following:
- Host: Enter the host name for the TXT record. For example, leave the host blank for an SPF record, or enter the value _dmarc for a DMARC record.
- TXT Value: The value you are setting as the destination of the Host.
- TTL: Determine how long the server should cache information.
- Select Save.
For more information on managing DNS records with Hover, click here.
How to create TXT records for SPF & DMARC with Ionos (Formerly 1&1)
- Log in to IONOS.
- For the desired domain, click on the gear symbol under Actions and select DNS.
- Click Add Record and select
TXTunder Type. - In the Host name field, specify the desired host, For example, enter @ for an SPF record, or enter the value
_dmarcfor a DMARC record. - In the Value field, paste the value you are setting as the destination of the Host (i.e. the value of the SPF or DMARC record to be used).
- Optional: Select the desired TTL (Time to Live). By default, your settings are immediately active.
- Click Save. The TXT record has now been added.
For more information on adding TXT records in Ionos, click here.
How to create TXT records for SPF & DMARC with Namecheap
- Login to your Namecheap Account, choose 'Domain List' on the left, and click on the 'Manage' button next to your domain.
- Navigate to the 'Advanced DNS' tab from the top menu and click on the 'Add new record' button.
- Select
TXTRecord for 'Type'. - Host: Enter the hostname for the
TXTrecord. For example, leave the host blank for an SPF record, or enter the value_dmarcfor a DMARC record. TXTValue: The value you are setting as the destination of the Host.- TTL: Determine how long the server should cache information.
NOTE: The domain name itself should not be included in the Host field. It means that if you need to add the record for dmarc.yourdomain.tld, dmarc.yourdomain.tld, only dmarcdmarc is to be added as a Host value. For more information, click here.
How to create TXT records for SPF & DMARC with Network Solutions
- Log in to your Network Solutions Account Manager.
- Enter the username and password you created when you purchased your domain from Network Solutions.
- Click Login.
- From the Network Solutions Account Manager, under My Domain Names, click 'Edit DNS'.
- Click 'Change Where Domain Points'.
- Select 'Advanced DNS' and click 'Continue'.
- Open the instructions for the type of DNS record you want to add for your domain. (TXT steps included below)
- Host: Enter the host name for the
TXTrecord. For example, enter @ for an SPF record, or enter the value_dmarcfor a DMARC record. TXTValue: The value you are setting as the destination of the Host.- TTL: Determine how long the server should cache information.
- Scroll down and click 'Continue'.
- Click 'Save Changes' to publish the record.
For more information on managing DNS records with Network Solutions, click here.
How to create TXT records for SPF & DMARC with 123Reg
- Login to your 123Reg Control Panel.
- Search your Domain Name next to DOMAINS and Click on MANAGE.
- Scroll down to Advanced Domain Settings and click on Manage DNS (
A,MX,CNAME,TXT,SRV). - Click on the Advanced DNS tab.
- Select
TXTorCNAMEas the Type and fill out the fields with the following info: a) Hostname: Enter the host name for theTXT/CNAMErecord. For example, enter @ for an SPF record, or enter the value_dmarcfor a DMARC record. b) DestinationTXTValue: The value you are setting as the destination of the Host. - When the information is entered, select Add.
For more information on managing DNS records in 123Reg, click here.
DNS setup instructions
AppRiver SPF and DKIM set up
SPF
AppRiver was bought by Zix, so your SPF record will depend on which product you have.
For more information on SPF at Zix, please click here.
DKIM
For more information on enabling DKIM, please contact AppRiver support.
Brevo (formerly Sendinblue) SPF and DKIM set up
Increase the deliverability of your Brevo (formerly Sendinblue) emails by correctly configuring SPF and DKIM.
SPF
Adding SPF for Brevo (formerly Sendinblue) for DMARC purposes is not needed because the Return-Path address of the emails is set to their default domain in order to track bounces on your behalf. Therefore, SPF will not pass for Brevo from a DMARC perspective, however, as long as DKIM passes, the emails will be DMARC compliant.
DKIM
To enable DKIM you will have to create a few DNS records. Please follow the instructions using the button below for more information.
Google Workspace SPF and DKIM set up
SPF
To authorize Google to send emails on your behalf you will need to create an SPF record that includes the following value:
include:_spf.google.com <-- this part allows all Gsuite IPs to send emails on your behalf.
If you already have an existing SPF record you will just have to copy the include include:_spf.google.com and append it to your current SPF record, however, it has to be put after the v=spf1 and before the ~all ending mechanism in your record.
If you already have an existing SPF record such as:
v=spf1 include:mail.zendesk.com ~all
and you would like to add Gsuite as an additional sending service, you will have to copy the include include:_spf.google.com and append it to your current SPF record.
The final SPF record should look like this:
v=spf1 include:mail.zendesk.com include:_spf.google.com ~all
Do not create a second SPF record if you already have one. You should only have one SPF record per domain/subdomain.
To learn more about SPF and how to configure it for Google Workspace please click here.
DKIM
To implement DKIM for your domain you will have to follow the steps below.
- Log in as administrator and go to the Admin Console.
- Go to Apps --> G Suite
- Click on the Gmail app.
- Click on Authenticate email
- For the key length you can choose between 1024 or 2048. The longer the key the better, however, some DNS providers do not support keys longer than 1024. They should be able to implement 2048 as well but there may be some additional work that needs to be carried out.
- Select your prefix selector, you can leave the default of "google" or type in your own. This will be your DKIM selector.
- Once the key is generated, you will need to take the information provided and put it in your DNS ie. create the
TXTrecord. It will look like the example below, except that you will have to replace the word "selector" below with the one that you created earlier.
Type | Host | TXT value | TTL |
TXT | selector._domainkey | Paste the key generated here | 1 hour (default) |
NOTE: it may take up to 48 hours for the DNS changes to propagate.
Also, you can't add a custom DKIM selector for 24 hours.
For more information please click here.
Hubspot SPF and DKIM set up
SPF
Adding SPF for Hubspot for DMARC purposes is not needed because the Return-Path address of the emails is set to Hubspot's default domain in order to track bounces on your behalf. Therefore, SPF will not pass for Hubspot from a DMARC's perspective, however, as long as DKIM passes, the emails will be DMARC compliant.
DKIM
For information on how to configure DKIM and add the necessary DNS records please click here.
Kajabi SPF and DKIM set up
As Kajabi constantly updates its documentation, please click here for the most accurate information.
Klaviyo SPF and DKIM set up
To authorize Klaviyo to send emails on your behalf and customize those emails to match your domain you will have to carry out full domain whitelabeling. During this process, you will be provided with the necessary DNS records that need to be created so your emails start passing SPF and DKIM.
For more information and instructions on how to complete the full whitelabeling process please click here.
Mailerlite SPF and DKIM setup
Mailerlite provides two ways of authenticating your domain. They can either manage the authentication for you or allow you to manage it yourself. If you let Mailerlite authenticate your emails then your receivers would see Mailerlite as the sender of your emails. If you would like your receivers to see your domain only then you will have to choose the option to authenticate emails yourself.
Configuring SPF and DKIM with Mailerlite for your custom domain is pretty easy. All you have to do is choose Authentication, insert your domain and select Show DNS record.
The necessary SPF and DKIM records will be generated and presented to you which you will then have to add to your DNS. For more information please click here.
Once you have created SPF and DKIM but still showing as inactive in your account, please click here for information on how to troubleshoot this.
Mandrill SPF and DKIM setup
Mandrill is a product created by Mailchimp and is a service used to send transactional emails. To improve your email deliverability, Mandrill requires that every domain of yours is configured with SPF and DKIM.
SPF
To allow Mandrill to send emails on your domain’s behalf, you must include them as part of your SPF record.
The SPF mechanism used by Mandrill is the following:
include:spf.mandrillapp.com
Mandrill uses their own domain as part of the Return-Path address (used by SPF) and hence SPF alignment would not occur. However, this can be modified as per their help article.
For more information, visit the Mandrill help article.
DKIM
To set up DKIM for Mandrill, you will need to add a new TXT record in your DNS.
The name for the TXT record should be:
mandrill._domainkey.yourdomain.comReplace “yourdomain.com” above with the domain you are setting up.
The value of the DNS record should be the following:
v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCrLHiExVd55zd/IQ/J/mRwSRMAocV/hMB3jXwaHH36d9NaVynQFYV8NaWi69c1veUtRzGt7yAioXqLj7Z4TeEUoOLgrKsn8YnckGs9i3B3tVFB+Ch/4mPhXWiNfNdynHWBcPcbJ8kjEQ2U8y78dHZj1YeRXXVvWob2OaKynO8/lQIDAQAB;
After you have added the required DNS records, you can use the Test the DNS Settings button in your control panel to make sure that everything that you have added has a green checkmark. Please allow 24-48 hrs for the DNS changes to take effect.
For more information, visit the Mandrill help article.
Mimecast DKIM signing setup
To setup DKIM signing in Mimecast you need to create a definition and a policy.
Setting up a definition
- Login to Mimecast
- Select Administration console
- From the top left select Administration > Gateway > policies
- Select definitions drop down select DNS Authentication - Outbound
- Select New DNS Authentication - Outbound signing
- Set a name for the definition
- Tick the checkbox Sign outbound mail with DKIM
- Use the lookup option to select domain to DKIM sign
- Select generate
- Create a
TXTrecord within your DNS with the public key provided save and exit - Verify public key in Mimecast console
Setting up a policy
- Login to Mimecast
- Select Administration Console
- From the top left select Administration > Gateway > policies
- Search for DNS authentication outbound
- Select New Policy
- Name the policy
- Under emails from use address based on "Both"
- Save and Exit
Microsoft Dynamics 365 SPF and DKIM set up
SPF
To authorize Microsoft Dynamics 365 to send emails on your behalf, you must include it in your SPF record. The SPF record mechanism used for Microsoft Dynamics 365 is shown below. Find more information here.
include:marketing.dynamics.com
DKIM
Microsoft Dynamics 365 supports DKIM signing for your custom domain. For more information on how to set it up please click on the button below. Find more information here.
Microsoft Office 365 SPF and DKIM set up
Set up your SPF record for Office 365
To authorize Microsoft 365 (formerly Office 365) to send emails on behalf of your domain you will have to add it to your SPF record. The SPF record mechanism used for Microsoft 365 is:
include:spf.protection.outlook.com <-- this part allows all Office 365 IPs to send emails on your behalf.
If Microsoft 365 is your only legitimate source of emails, your SPF record should look like the below example:
v=spf1 include:spf.protection.outlook.com ~all
If you already have an existing SPF record such as:
v=spf1 include:mail.zendesk.com ~all
and you would like to add Office 365 as an additional sending service, you will have to copy the include include:spf.protection.outlook.com and append it to your current SPF record. The final SPF record should look like this:
v=spf1 include:mail.zendesk.com include:spf.protection.outlook.com ~all
However, do not create a second SPF record if you already have one. You should only have one SPF record per domain/subdomain.
I get a warning from Microsoft 365 when using Dynamic SPF
If you are using Dynamic SPF and you also use Microsoft 365 for email, you may have noticed that Microsoft will give you a warning about your SPF include being incorrect.
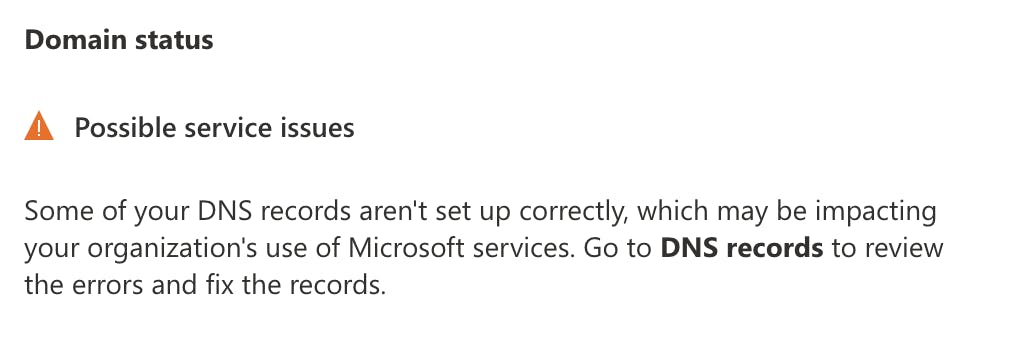
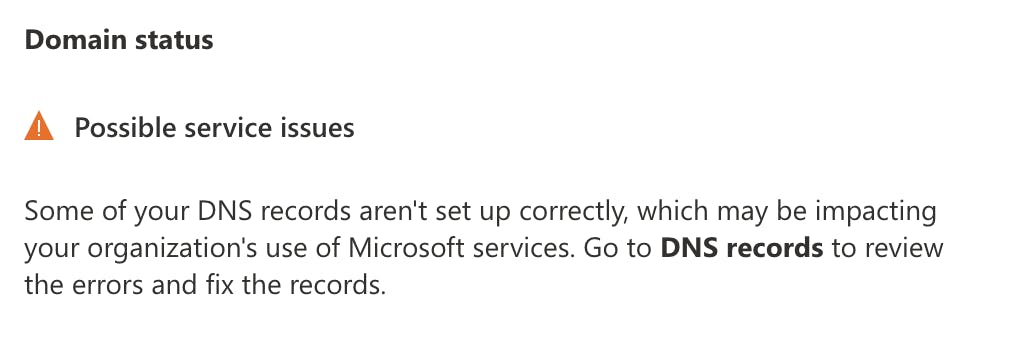
This is expected and you can safely ignore it. Microsoft is looking for the literal string they provide in your DNS and does not know that their IP ranges are already included in Dynamic SPF.
You can test Dynamic SPF is working correctly by sending a test email to the address listed in the Investigate section of the OnDMARC console.
Set up your DKIM for Office 365
In order to DKIM sign your custom domain emails you will need to complete the following steps.
Creating the CNAME records
The CNAME records are used to map an alias name to the true or canonical domain name. In essence, when you provision a new domain name in Microsoft 365 you will need to create two CNAME records for it so that it points to your initial domain.
We will use example.onmicrosoft.com as our initial domain, also called the tenant domain. But we actually own example.com and after we provision it in Office 365 we need to publish the two CNAME records so that example.com points to example.onmicrosoft.com using the format below.
Please note that if you are a Microsoft 365 US Government Cloud (GCC) customer, the domainGUID method below will not work for you. You will need to use the proper MX value for your domain. Example:
selector1-<domain-key>._domainkey.<initialDomain>
Use this article to find the MX record needed for your domain-key value.
Host name: selector1._domainkey.<domain> Points to address or value: selector1-<domainGUID>._domainkey.<initialDomain> TTL: 3600
Host name: selector2._domainkey.<domain> Points to address or value: selector2-<domainGUID>._domainkey.<initialDomain> TTL: 3600
In our example the CNAME records will look like this:
Host name: selector1._domainkey.example.com Points to address or value: selector1-example-com._domainkey.example.onmicrosoft.com TTL: 3600
Host name: selector2._domainkey.example.com Points to address or value: selector2-example-com._domainkey.example.onmicrosoft.com TTL: 3600
Please pay close attention to the domainGUID which does not use a full stop "." but a dash "-" instead. This is taken from the MX record of your custom domain, in this case, example.com.example.com.
The reason behind the two CNAME records is that Microsoft rotates the two keys for added security.
Enabling DKIM signing
Once you have added the CNAME records (two per domain) DKIM signing can be enabled through the Microsoft 365 Security admin center at http://security.microsoft.com/dkimv2
For more information on how to configure DKIM in Office 365 please click here.
Namecheap Private Email SPF and DKIM set up
SPF
To authorize Namecheap Private Email to send emails on your behalf you will have to include it in your SPF record. The SPF record mechanism used is shown below.
include:spf.privateemail.com
For more information on SPF set up for Namecheap Private Email please click here.
DKIM
For instructions on how to set up DKIM, please click here.
Proofpoint Protection Server (PPS) SPF and DKIM setup
SPF
To authorize Proofpoint to send emails on your behalf, you must include it in your SPF record. Refer to your Deployment Information email for the details, as the SPF is unique to each PPS cluster.
It usually follows the format:
include:spf-{clusterid}.pphosted.comDKIM
To set up DKIM on PPS, follow these steps:
- Navigate to Email Protection tab > Email Authentication > DKIM Signing > Keys
- Click Generate Key to create a key for a domain and selector. Each key must have a unique domain and a unique selector within the domain. Proofpoint-generated domain keys are 2048-bits in length.
- At the Generate Key Entry dialog box type or specify your domain, the selector, the scope of the key, and the policy routes. For the policy routes, only check Disable processing for selected policy routes… Under Available scroll down and select default_inbound Click the >> to add it to Disable For Any Of:
- Click on Add Entry.
- Click View in the DNS Text Record column to see the text record for a DKIM key.
- A pop-up window displays the DNS text record that contains the public key. Copy the DNS text record for each domain-selector pair to your DNS servers
- Once the DNS record has been created, wait a few minutes to ensure the record has time to propagate.
- On the PPS Admin Console and click on Test to verify if the DNS record was created correctly.
- The feedback for the test will appear above the navigation tabs (System, Email Protection, Information Protection).
- Once the DNS record has been validated click the Enabled box and then click Save Changes.
- Turn on DKIM Signing by navigating to Email Protection tab > Email Authentication > DKIM Signing > General
- Click On next to Enable
- Click Save Changes
For more details or detailed screenshots, refer to the Proofpoint documentation here.
Salesforce Marketing Cloud SPF and DKIM set up
SPF
To authorize Marketing Cloud to send emails on your behalf you will have to include it in your SPF record. The SPF record mechanism used for Marketing Cloud is shown below. Found out more here.
include:cust-spf.exacttarget.com
DKIM
If you have the Sender Authentication Package you will be able to enable DKIM. Please contact your account manager at Marketing Cloud for more information.
Shopify SPF and DKIM record set up
What is the SPF record mechanism and DKIM selectors used by Shopify that I need to configure in DNS?
SPF
To allow Shopify to send emails on your behalf you will have to add it to your SPF record. The SPF record mechanism used for Shopify is shown below.
include:shops.shopify.com
DKIM
To set up DKIM for Shopify, you can authenticate your domain by clicking Authenticate on the Sender email page of your Shopify admin console. A new window will open and provide you with instructions on how to create four new records with your domain provider.
Custom domain settings for Shopify
Squarespace SPF and DKIM set up
SPF
To allow Squarespace to send emails on your behalf, you will have to add them to your SPF record. The SPF mechanism used by Squarespace is shown below.
include:squarespace-mail.com
DKIM
For DKIM support, you need to create a CNAME record in your DNS.
It should have the following properties:
Host: squarespace._domainkeyValue: squarespace-domainkey.squarespace-mail.comFor more information please click here.


Domande frequenti: Guida alla configurazione dei protocolli email
Prima di DMARC, nei record SPF era spesso usato il meccanismo “-all” per applicare restrizioni rigorose alle policy dei mittenti. Tuttavia, le attuali raccomandazioni del settore per il 2026 privilegiano “~all” per bilanciare sicurezza e deliverability ed evitare il rifiuto non necessario di email legittime che falliscono SPF, ma superano DKIM e DMARC.
Il motivo è che “~all” in combinazione con DMARC (in p=reject) consente comunque di non recapitare email non autenticate quando SPF e DKIM falliscono, senza bloccare email legittime – migliorando così la deliverability complessiva.
Le specifiche DMARC (RFC 7489) affermano che un prefisso “-” nel meccanismo SPF del mittente – come “-all” – può comportare il rifiuto di un’email già nella fase iniziale, cioè prima che venga applicato DMARC. Utilizza “-all” solo per domini inattivi che non inviano mai email. DMARC non distingue tra Soft Fail e Hard Fail su SPF: considera entrambi semplicemente come un errore SPF.
DMARC richiede non solo che SPF o DKIM abbiano esito positivo, ma anche che almeno uno dei domini usati con SPF o DKIM corrisponda al dominio presente nell'intestazione From. Un corretto allineamento è fondamentale nel 2026 per la consegna delle email, perché i principali provider ora richiedono questa verifica.
Per SPF, l’allineamento significa che la verifica di MAIL FROM/Return-PATH è andata a buon fine e la parte dominio di MAIL FROM/Return-PATH coincide con il dominio dell’indirizzo From. In modalità Strict le due devono essere identiche; in modalità Relaxed vengono accettate anche le sottodomini se appartengono alla stessa organizational domain.
Esempio: se MAIL-FROM/RETURN-PATH è @ondmarc.com e il From-header è @knowledge.ondmarc.com, non sono allineati in modalità Strict, ma DMARC li considererebbe validi in modalità Relaxed.
Un report aggregato DMARC contiene informazioni sullo stato di autenticazione dei messaggi inviati per conto di un dominio. Si tratta di un bounce report in XML che riepiloga quali email hanno superato o fallito SPF e DKIM. Permette ai possessori di dominio di avere una panoramica precisa delle fonti che inviano email a loro nome e cosa succede (policy del destinatario).
I destinatari usano il tag 'rua' del record DMARC per inviare i report. Puoi definire la frequenza usando il tag ri nel record DMARC (valore predefinito: 86400 secondi, ovvero 24h). I report forensi forniscono dettagli molto più precisi su ogni fallimento di autenticazione. I dati personali vengono rimossi, ma tutte le informazioni utili alla risoluzione dei problemi, come header SPF/DKIM e indirizzo mittente completo e oggetto, sono trasmesse.
L’indirizzo di ricezione dei report forensi DMARC si indica tramite il tag 'ruf'. Non tutti i sistemi supportano questi report. Red Sift OnDMARC è tra le poche soluzioni che può ricevere report forensi – grazie alla partnership con Yahoo.
Una macro SPF è un meccanismo nei record SPF che consente di definire insiemi riutilizzabili di indirizzi IP. Le macro SPF offrono maggiore flessibilità e mantenibilità: puoi definire set complessi di IP in un unico meccanismo e referenziarli in vari record. Ad esempio, invece di elencare ogni IP autorizzato, puoi usare una macro come “%{i}”, che richiama l’IP in uscita dell’email. In questo modo puoi gestire facilmente grandi elenchi IP senza superare il limite di lookup SPF e rendere meno evidenti le autorizzazioni IP durante le interrogazioni DNS.
A seconda della struttura della macro nel record SPF, una mancata espansione della macro può causare errori SPF o un risultato neutro (?all). Se l’invio di email legittime dipende dalle macro SPF, queste ultime possono portare a maggiori fallimenti o a segnalare come sospetto il traffico verso sistemi che si basano su SPF.
Mail Transfer Agent Strict Transport Security (MTA-STS) è uno standard per la cifratura dei messaggi tra due server di posta. Comunica ai server mittenti che le email devono essere recapitate solo tramite connessione sicura, tramite Transport Layer Security (TLS), proteggendo così dai tentativi di intercettazione da parte dei criminali informatici.
L’adozione di MTA-STS è cresciuta rapidamente e nel 2026 la sicurezza dei trasporti sarà considerata essenziale per la protezione della posta in transito. Per attivare MTA-STS su un dominio ricevente, occorre dichiarare il supporto tramite DNS e rendere disponibile un file di policy sul proprio sito.
MTA-STS va attivato con cautela per non causare blocchi accidentalmente. Si consiglia di iniziare con la modalità Test: in questo modo, grazie ai rapporti TLS, puoi identificare e risolvere eventuali errori prima di passare alla modalità strict. Questo approccio graduale sarà probabilmente lo standard per la protezione della posta in transito nel 2026.
SMTP TLS Reporting (TLS-RPT), secondo RFC8460, serve a segnalare problemi di connettività TLS dai server MTA mittenti. Proprio come per DMARC, anche qui vengono inviati report via email al titolare del dominio quando problemi TLS ostacolano la consegna. I report contengono le policy MTA-STS rilevate, statistiche di traffico, connessioni fallite e motivi di errore.
Con la funzione MTA-STS in Red Sift OnDMARC non dovrai preoccuparti delle complesse implementazioni. Basta aggiungere gli MTA-STS Smart Record forniti da OnDMARC al proprio DNS e Red Sift si occuperà dell’hosting del file di policy, la gestione del certificato SSL e l’invio automatico di segnalazioni di violazione via report TLS. Nel 2026, l’MTA-STS in hosting è sempre più uno standard previsto nelle moderne piattaforme DMARC, rendendo più semplice l’integrazione della cifratura nei trasporti.
Secondo RFC 7671, DANE (DNS-based Authentication of Named Entities) è un nuovo standard Internet per la creazione di comunicazioni TLS tra client e server senza dipendere dalle autorità di certificazione (CA) tradizionali.
Nel modello attuale, qualsiasi CA può rilasciare un certificato per qualunque dominio. DANE adotta un altro approccio, sfruttando l’infrastruttura DNSSEC (Domain Name System Security Extensions) per associare in modo crittografico un nome di dominio a un certificato. DANE si basa sul protocollo DNSSEC esistente per garantire autenticità e integrità della ricezione.
DANE introduce inoltre un nuovo tipo di record DNS, TLSA, che segnala al client il supporto server a TLS. È raccomandato implementare sia MTA-STS sia DANE. DANE è d’obbligo per molti enti pubblici, in particolare in UE.
MTA-STS e DANE sono efficaci solo se anche il server mittente li supporta – molti implementano solo uno dei due. Attivare entrambi aumenta la sicurezza generale. Nel 2026 le organizzazioni adottano spesso MTA-STS prima, per massima compatibilità, e aggiungono DANE per livelli di sicurezza superiori quando richiesto.
La policy per le sottodomini permette agli amministratori di proteggere in modo differenziato diversi domini e sottodomini a seconda dello stadio di implementazione di DMARC. Ad esempio, se tutti i servizi di invio associati al dominio principale sono già protetti da SPF e DKIM, puoi impostare una policy DMARC p=reject sul dominio principale e p=none sulle sottodomini – o viceversa.
Se un servizio di invio non supporta DMARC (cioè non implementa SPF o DKIM) puoi assegnargli una sottodominio separata con una policy DMARC propria, senza compromettere la protezione dei domini restanti. Ciò consente di distribuire il traffico tra diverse sottodomini e proteggerle separatamente secondo le esigenze.






