Key takeaways
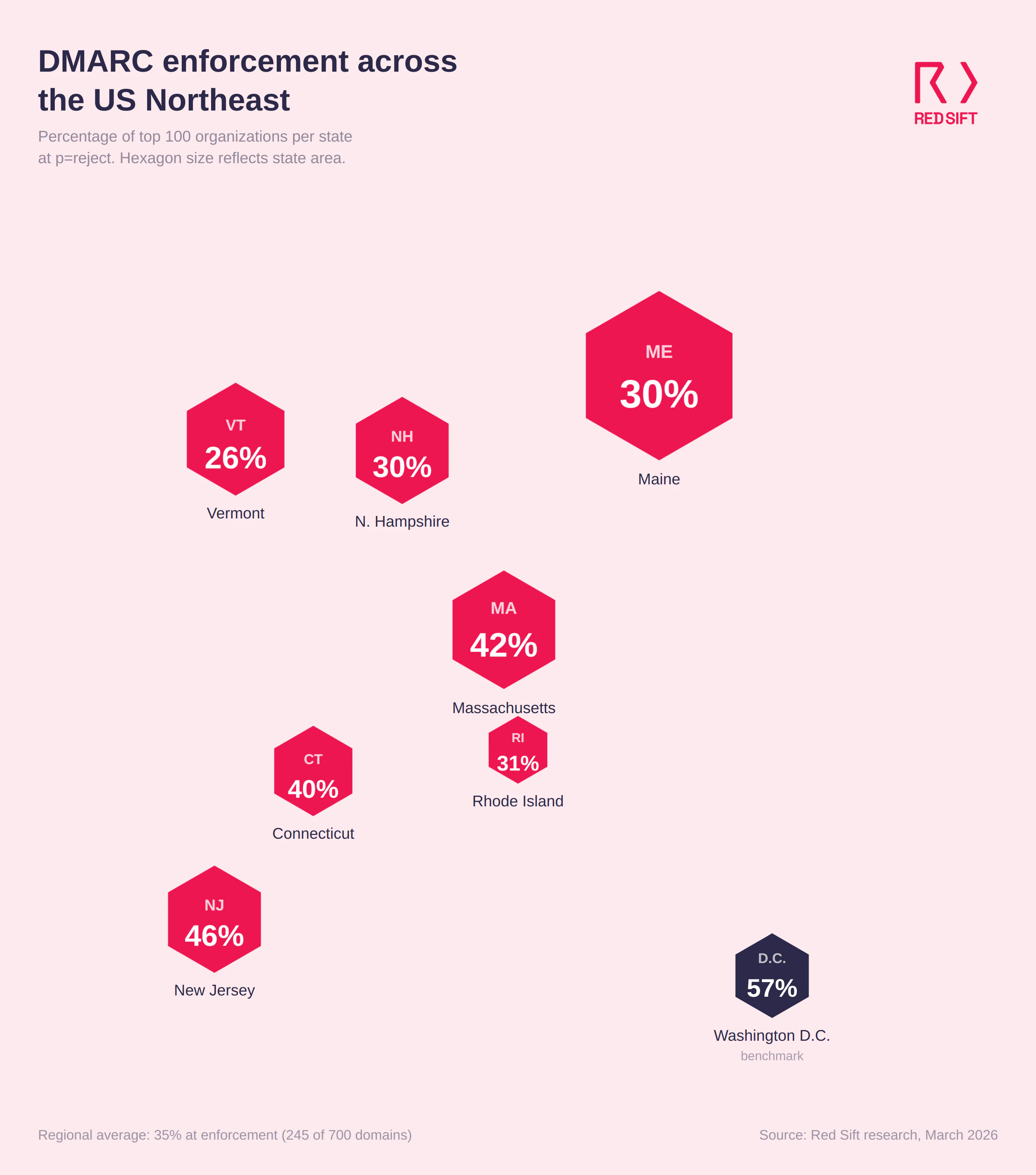
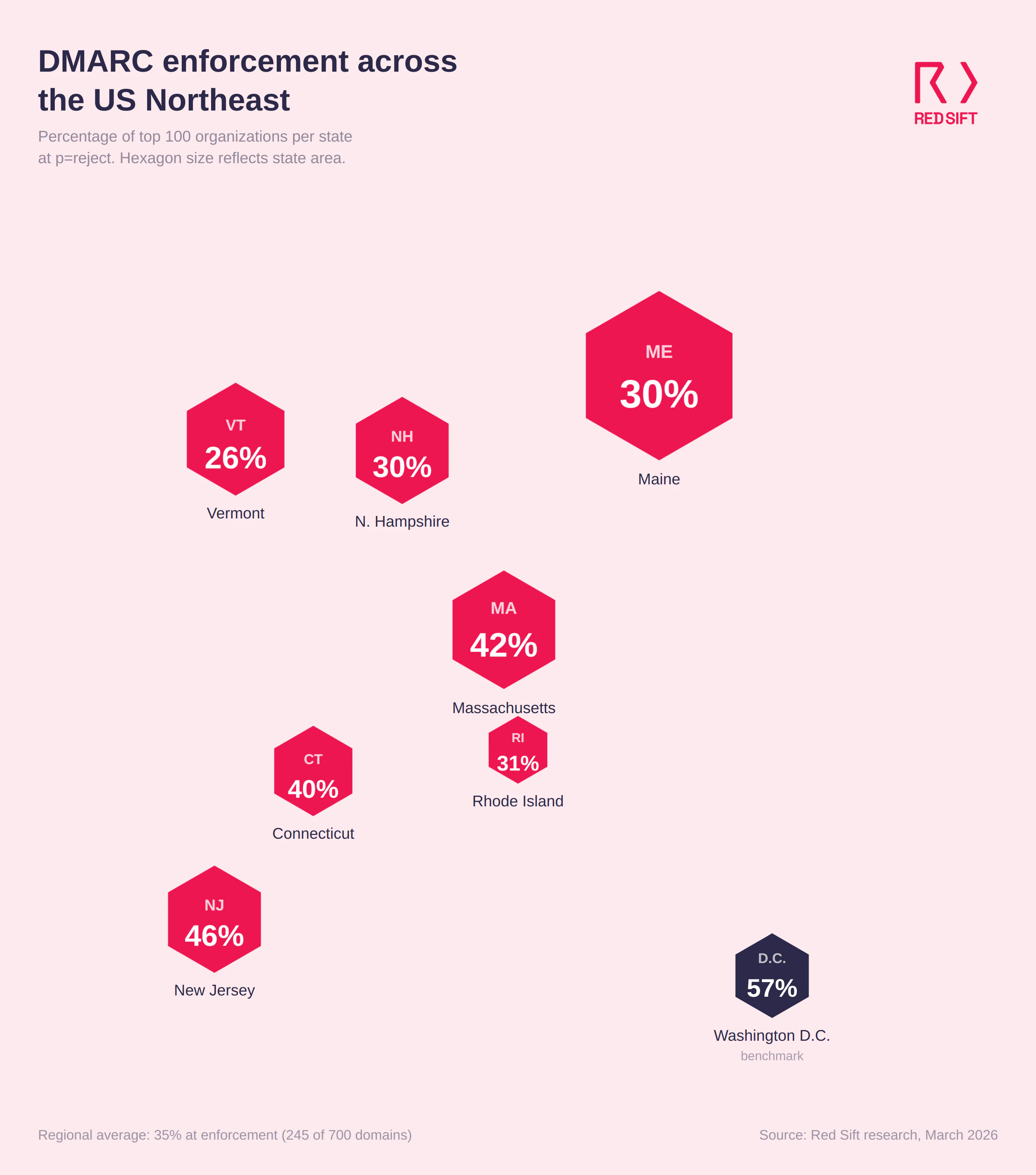
- Only 245 of 700 domains (35%) across seven Northeast states have reached DMARC enforcement (p=reject)
- 216 domains (30.9%) run p=none policies that monitor but take no action against spoofed emails
- 158 domains (22.6%) sit at p=quarantine, close to full protection but not finishing the move to reject
- 81 domains (11.6%) have no DMARC record published at all
- New Jersey leads the region at 46% enforcement. Vermont trails at 26%
What does the research reveal about email authentication in the Northeast?
Red Sift analyzed 100 domains from the top organizations in each of seven Northeast states: Connecticut, Maine, Massachusetts, New Hampshire, New Jersey, Rhode Island, and D.C. The results show a region where the majority of top organizations haven't implemented full email authentication, despite operating in sectors where trusted communication is the baseline.
Across all 700 domains, only 35% have reached p=reject, the DMARC policy level that actively blocks spoofed emails. That puts the Northeast well behind Washington D.C. (57%) in Red Sift's ongoing cross-region comparison.
State-by-state breakdown
- New York*: 73% at enforcement New York leads the region, with nearly three quarters having reached DMARC enforcement (p=reject), the highest rate Red Sift has recorded across major US city analyses.
- New Jersey: 46% at enforcement New Jersey comes second with 46 domains at p=reject. But more than half of the state's top organizations still aren't blocking spoofed emails: 26 run p=none, 19 sit at p=quarantine, and 9 haven't published a DMARC record. For a state with major pharmaceutical companies, financial institutions, and Port Newark handling billions in logistics, 46% isn't enough.
- Massachusetts: 42% at enforcement Massachusetts comes in second. 42 domains block spoofed email outright, but 28 are stuck at p=none and 26 at p=quarantine. The state is home to some of the country's largest hospital networks, biotech companies, and universities, all of which are high-value impersonation targets. Only 4 domains have no DMARC record, the lowest N/A rate in the study.
- Connecticut: 40% at enforcement 40 of Connecticut's top 100 domains have reached p=reject. The rest split between p=none (27), p=quarantine (26), and no record (7). Connecticut's insurance corridor and defense contractors send massive volumes of policy-related and contract email. Every one of those messages is more trustworthy when it's authenticated.
- Rhode Island: 31% at enforcement Rhode Island splits evenly between p=reject (31) and p=none (31), with 24 at p=quarantine. 14 domains have no DMARC record at all, one of the highest N/A rates in the study. The state's smaller organizational footprint doesn't reduce the risk. It concentrates it.
- Maine and New Hampshire: 30% at enforcement (tied) Both states have 30 domains at p=reject, but the shape of the remaining 70% differs. Maine has the region's highest p=none count at 37, meaning those organizations have published a DMARC record that does nothing to stop fraud. New Hampshire has 33 at p=none and 16 with no record. Regional healthcare systems in both states are particularly exposed given smaller security teams and high volumes of patient-facing email.
- Vermont: 26% at enforcement Vermont is at the bottom of the table. Only 26 domains block spoofed email, while 34 run p=none and 24 sit at p=quarantine. 16 have no record. Nearly three-quarters of the state's top organizations can have their domains impersonated without any email being blocked.
Regional comparison
State | Reject | Quarantine | None | No record |
New Jersey | 46% | 19% | 26% | 9% |
Massachusetts | 42% | 26% | 28% | 4% |
Connecticut | 40% | 26% | 27% | 7% |
Rhode Island | 31% | 24% | 31% | 14% |
Maine | 30% | 18% | 37% | 15% |
New Hampshire | 30% | 21% | 33% | 16% |
Vermont | 26% | 24% | 34% | 16% |
Regional total | 245 (35%) | 158 (22.6%) | 216 (30.9%) | 81 (11.6%) |
Washington D.C.* | 57% | 20% | 21% | 2% |
New York* | 73% | 15% | 12% | 1% |
*For comparison, we've also included Red Sift's earlier city-level analyses of Washington D.C. and New York. These are not part of the seven-state Northeast total.
The 158 organizations sitting at p=quarantine are close. They've done the DNS work, identified their senders, and configured SPF and DKIM. Moving from quarantine to reject typically takes 6 to 8 weeks. That's 158 domains where a short project finishes a job that's mostly complete.
Assess your domain today
Why DMARC is essential for the Northeast in 2026
The Northeast runs on industries where trust isn't optional. Financial services, healthcare, higher education, defense, and insurance all depend on email for high-stakes communication. And every one of those sectors is concentrated here more than anywhere else in the country.
Financial services and insurance are prime BEC targets
Connecticut's insurance corridor, New Jersey's pharmaceutical giants, and the financial firms spread across the region send billions of emails tied to policies, claims, wire transfers, and regulatory filings. The FBI's IC3 reported $2.77 billion in BEC losses in 2024, and nearly $8.5 billion lost between 2022 and 2024 combined. A spoofed email from an insurer to a broker, or from a bank to a corporate treasury team, can move six- and seven-figure sums before anyone notices. DMARC enforcement stops the impersonation before it reaches the inbox.
Patient data flows through email, and spoofed domains put it at risk
Massachusetts is home to some of the country's largest hospital systems and biotech firms. Patient data, clinical trial coordination, insurance claims, and referral networks all travel by email. A spoofed hospital domain can compromise protected health information, trigger HIPAA investigations, and erode patient trust. Maine, New Hampshire, and Vermont have significant regional healthcare systems that face the same exposure with smaller security teams to manage it.
The densest university cluster in America is largely unprotected
The Northeast has more universities per square mile than anywhere else in the country. Massachusetts, Connecticut, Rhode Island, New Hampshire, and Vermont all have major institutions that email students, alumni, donors, research partners, and government agencies daily. Universities are frequent phishing targets because they combine large, rotating user populations with decentralized IT. A spoofed .edu domain can harvest credentials, distribute malware, or run financial aid scams. And most of the institutions in this study aren't blocking those spoofed emails.
Mailbox providers are now rejecting unauthenticated email
Google and Yahoo began requiring DMARC for bulk senders in February 2024. Microsoft followed in May 2025. As of late 2025, Google now issues permanent rejection errors for non-compliant messages. For Northeast organizations sending policy renewals, patient communications, alumni appeals, or procurement updates, a missing or weak DMARC policy means those messages may never arrive.
Compliance pressure is building from multiple directions
PCI DSS 4.0.1 mandates DMARC for organizations handling payment card data. NIS2 applies to any Northeast firm with EU operations or clients. Cyber insurers are tightening requirements, with some excluding BEC payouts for organizations that lack basic email authentication. For the region's defense contractors, these requirements overlap with CMMC and NIST frameworks that already recommend DMARC as a baseline control.
Why choose Red Sift OnDMARC
Northeast organizations operate in a complex environment: multiple regulatory frameworks, sprawling vendor ecosystems, legacy infrastructure, and sectors where email is the default channel for sensitive communication. Red Sift OnDMARC is built for that complexity.
- Enforcement in 6 to 8 weeks: Manual DMARC projects average around 32 weeks. OnDMARC cuts that to 6 to 8 weeks by automating source identification, SPF and DKIM configuration, and enforcement readiness checks. For the 158 Northeast organizations sitting at p=quarantine, the final step to reject could be measured in weeks, not months.
- Dynamic SPF for complex sender lists: Northeast organizations tend to have long lists of authorized email senders: CRM platforms, patient portals, alumni systems, claims processing, marketing tools, and more. SPF records have a hard limit of 10 DNS lookups, and complex organizations blow past that quickly. Red Sift's Dynamic SPF manages this automatically, keeping authentication valid without manual record management.
- Clear reporting across every domain: OnDMARC converts raw DMARC aggregate and forensic reports into a dashboard that shows every service sending email on behalf of your domains. Security and compliance teams get immediate visibility into what's authorized, what's failing authentication, and what needs fixing. No XML parsing. No guesswork.
- Continuous monitoring for regulated industries: Healthcare, financial services, insurance, and defense contractors all face ongoing audit and compliance requirements. OnDMARC provides continuous monitoring and alerting, so enforcement holds even as new senders are added, domains change hands, or infrastructure evolves through mergers and acquisitions.
35% enforcement across seven states isn't where the Northeast should be. The 245 organizations at p=reject have proven the path works. For the other 455, Red Sift OnDMARC can close the gap between the region's risk exposure and its current email security posture.
Jack leads content, PR, GEO, and email security research at Red Sift.






